PhD defense: Accurate Dynamic Power Supply Analysis and Delay Estimation, 4/3
Ph.D. Dissertation Defense
Computer Engineering
PSANDE: A Framework for Accurate Dynamic
Power Supply Analysis and Delay Estimation
Sushmita K. Rao
11:30am Friday, 3 April 2015, ITE 325b, UMBC
Power-supply noise is a major contributing factor for yield loss in sub-micron designs. Excessive switching in test mode causes supply voltage to droop more than in functional mode, leading to failures in delay tests that would not occur otherwise under normal operation. There exists a need to accurately estimate on-chip supply noise early in the design phase to meet power requirements in normal mode and during test to prevent over-stimulation during testing and avoid false failures. Simultaneous switching activity (SSA) of several logic components is one of the main sources of power-supply noise (PSN) which results in reduction of supply voltages at the power-supplies of the logic gates. Current research concentrates on static IR-drop, which accounts for only part of the total voltage drop on the power grid and therefore is insufficient for nanometer designs. Inductive drop is not included in current noise analysis techniques for simplification.
The power delivery networks in today’s very deep-submicron chips are susceptible to slight variations and cause sudden large current spikes leading to higher Ldi/dt drop than resistive drop, necessitating the need to be accounted. Especially of concern is simultaneous switching in localized areas in a chip because it concentrates current drawn on a particular power bump further reducing supply voltage. Thus, there arises a growing need to accurately characterize the resistive and inductive voltage drop caused by simultaneous switching of multiple paths. Power-supply noise also impacts circuit operation, causing a significant increase in path delays. It is critical to account for this increase in delay during the ATPG process otherwise it can lead to overkill during transition and delay testing. However, it is infeasible to carry out full-chip SPICE-level simulations on a design to validate the large number of ATPG generated test patterns. Accurate and efficient techniques are required to quantify supply noise and its impact on path delays to ensure reliable operation in both mission mode and during test.
A scalable current-based dynamic method is presented to estimate both IR and Ldi/dt drop caused by simultaneous switching activity. Also presented is a technique to predict the increase in path delays caused by supply noise. The noise and delay estimation techniques use simulations of individual extracted switching logic in comparison to time-consuming full-chip simulations and thus it can be integrated with existing ATPG tools. A design partitioning technique is also presented that makes the framework feasible for larger designs. Supply noise estimation error is less than 12% of SPICE level full-chip results across all test cases in the combinational and sequential benchmark circuits. The effect of power supply noise on path delays is modeled effectively. Results from multiple designs show that using the convolution-based technique the increase in path delay can be accurately predicted with a worst case error of 4% as compared to full-chip simulation results demonstrating the effectiveness of the technique.
Committee: Drs. Chintan Patel (Chair), Dhananjay Phatak, Ryan Robucci, Nilanjan Banerjee and Ismed Hartanto (Xilinx)
]]>
Ph.D. Dissertation Defense Computer Engineering PSANDE: A Framework for Accurate Dynamic Power Supply Analysis and Delay Estimation Sushmita K. Rao 11:30am Friday, 3 April 2015, ITE 325b,...
http://www.csee.umbc.edu/2015/04/phd-defense-accurate-dynamic-power-supply-analysis-and-delay-estimation-43/
https://my3.my.umbc.edu/api/v0/pixel/news/50914/guest@my.umbc.edu/6453ae634e73c8744e72f515b8545423/api/pixel
computer-engineering
defense
graduate
news
research
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 02 Apr 2015 20:15:53 -0400
MS defense: Graph-Theoretical Analysis using Data-Driven Features: Application to Rehabilitation After Stroke
ENEE MS Thesis Defense
Graph-Theoretical Analysis using Data-Driven Features:
Application to Rehabilitation After Stroke
Jonathan Laney
1:30pm Friday, 3 April 2015, ITE 346, UMBC
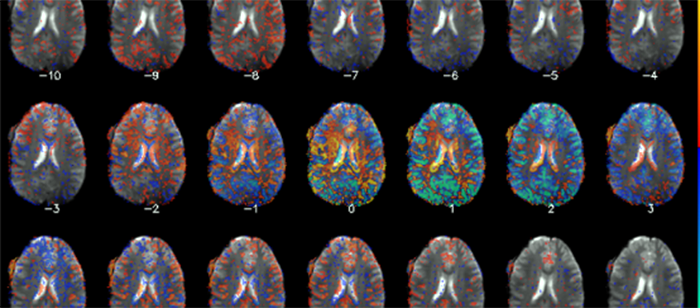
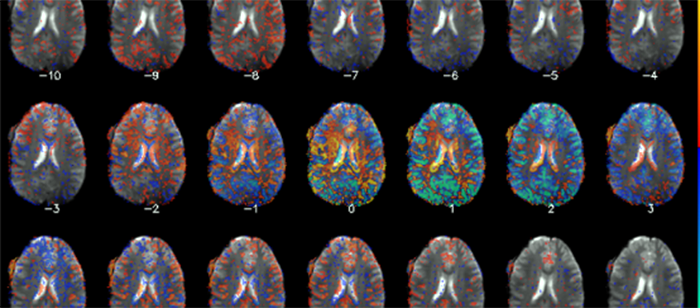
The assessment of neuroplasticity after stroke through functional magnetic resonance imaging (fMRI) analysis is a developing field where the objective is to better understand the neural process of recovery and to better target rehabilitation interventions. In this study, the connectivity structure of the stroke-affected brain is analyzed before and after a rehabilitation intervention. The challenge associated with our fMRI data stems from the large amount of individual spatial variability exhibited by the dataset and the need to summarize entire brain maps by generating simple, yet discriminating features, to highlight differences in patients’ functional connectivity. The comparison of algorithms in terms of their ability to capture spatial variability for each subject is not straightforward due to the lack of a ground truth for real fMRI data.
We provide a graph-theoretical (GT) framework to effectively make such a comparison for real data. We investigate and discuss the important role of order selection for data that exhibits large amounts of subject variability. Furthermore, we demonstrate that Independent vector analysis (IVA) provides superior performance in preserving subject variability when compared with widely used methods such as group independent component analysis. We pair IVA with GT analysis to produce discriminative features, which highlight neuroplastic changes between the groups before and after intervention. Resulting GT features are shown to capture connectivity changes that are not evident through direct comparison of the group t-maps, i.e., brain maps obtained by a t-test taken across subjects’ spatial brain maps. Additionally, we compare the responders to the intervention with the non-responders and demonstrate that their relative improvements, as shown through our fMRI analysis, correspond to clinical findings. In this study, increased small worldness across components and greater centrality in key motor networks are demonstrated as a result of the intervention, suggesting improved efficiency in neural communication. Clinically, these results bring forth new possibilities as a means to observe the neural processes underlying improvements in motor function.
Committee: Drs. Tulay Adali (Chair), Joel Morris, Chuck LaBerge, Kelly Westlake and Charles Cavalcante
]]>
ENEE MS Thesis Defense Graph-Theoretical Analysis using Data-Driven Features: Application to Rehabilitation After Stroke Jonathan Laney 1:30pm Friday, 3 April 2015, ITE 346, UMBC The...
http://www.csee.umbc.edu/2015/04/ms-defense-graph-theoretical-analysis-using-data-driven-features-application-to-rehabilitation-after-stroke/
https://my3.my.umbc.edu/api/v0/pixel/news/50864/guest@my.umbc.edu/0947a01ef07af94a802448e4d09bec92/api/pixel
defense
electrical-engineering
graduate
news
research
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Wed, 01 Apr 2015 17:05:55 -0400
Freeman Hrabowski on the future of learning

Team HueBotics, a video-game development team at UMBC, is among the final four student teams competing to represent the U.S. in the Games division of the 2015 Microsoft Imagine World Cup competition. The teammates are (l. to r.) Jasmin Martin, Erika Shumacher, Tad Cordle, and Michael Leung. Source: Nicolas Deroin
UMBC President Freeman Hrabowski has a commentary article on CNBC, Video games in the classroom? Welcome to the future of learning, that talks about new ways to engage students in learning.
“Our university is headed to the “final four” — in game design. Next month, a team from the University of Maryland, Baltimore County (UMBC) will travel to San Francisco to compete against three other teams in the games category of the final U.S. round of the Microsoft Imagine Cup, a global student technology competition. The team will pitch its project to a panel of judges composed of Silicon Valley technology leaders and entrepreneurs. As the students vie for the honor of representing the U.S. internationally, they’re also showing us the future of teaching, learning, and careers.”
Dr. Hrabowski makes an important observations on collaborations between STEM the arts and STEM disciplines, the need for diversity and how to excite and inspire today’s students.
“The UMBC team reflects the American workplace of the near future, bringing together two men and two women from diverse racial and ethnic backgrounds. The team also illustrates the potential of “STEAM” collaborations, where science, technology, engineering, and math (STEM) are combined with art and design. Two members of the team are studying the computer sciences and two the visual arts, focusing on interactive media. … Moreover, Team Huebotics provides clues about how to improve education for students of all backgrounds. Too many young people today are bored at every level of education. And yet our student game developers voluntarily put in hundreds of hours on their winning creation. American education, from pre-K to college, must find ways to inspire similar dedication and to bring content to life. Digital environments are second nature to today’s young people. Playing well-designed games, as well as creating them, can pack an educational punch.”
Dr. Hrabowski also mentions the game Bandit (though not by name), in which you play a fox sneaking around civil war Baltimore in the time leading up to the Pratt Street Riot. This game, designed to teach about an important episode of civil war history, is being developed by a team of computer science and visual arts students in collaboration with students in history and music under the faculty guidance of professors Anne Rubin and Marc Olano, the director of UMBC’s Computer Science Game Development Track.
You can read Dr. Hrabowski’s full commentary piece online here.
]]>
Team HueBotics, a video-game development team at UMBC, is among the final four student teams competing to represent the U.S. in the Games division of the 2015 Microsoft Imagine World Cup...
http://www.csee.umbc.edu/2015/04/dr-hrabowski-on-the-future-of-learning/
https://my3.my.umbc.edu/api/v0/pixel/news/50856/guest@my.umbc.edu/0803ba76f702b95db2031f22e95fecc3/api/pixel
education
game-track
news
students
undergraduate
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Wed, 01 Apr 2015 11:04:26 -0400
Fri, 03 Apr 2015 10:20:26 -0400
PhD defense: Rayleigh-Scattering-Induced Noise in Analog RF-Photonic Links

Ph.D. Dissertation Defense
Rayleigh-Scattering-Induced Noise in Analog RF-Photonic Links
James Cahill
3:00pm Tuesday, 7 April 2015, ITE 325b
Analog RF-photonic links hold the potential to increase the precision of time and frequency synchronization in commercial applications by orders of magnitude. However, current RF-photonic links that are used for synchronization must suppress optical-fiber-induced noise by using active feedback schemes that are incompatible with most existing fiber-optic networks. Unless this noise can be suppressed using different methods, RF-photonic time and frequency synchronization will remain accessible only to the research community. As a first step towards identifying alternate means of suppressing the optical-fiber-induced noise, this thesis presents an extensive experimental characterization and limited theoretical discussion of the dominant optical-intensity and RF-phase noise source in a laboratory setting, where environmental fluctuations are small. The experimental results indicate that the optical-fiber-induced RF-phase noise and optical-intensity noise are caused by the same physical mechanism. The experimental results demonstrate that this mechanism is related to the laser phase noise but not the laser intensity noise. The bandwidth of the optical-fiber-induced noise depends on the optical fiber length for lasers with low phase noise, while for lasers with high phase noise, the bandwidth is constant. I demonstrate that the optical-intensity and RF-phase noise can be mitigated without active feedback by dithering the laser frequency. Based on these results, I hypothesize that interference from Rayleigh scattering is the underlying mechanism of the optical-intensity and RF-phase noise. The literature predicts that the noise induced by this process will have a bandwidth that is proportional to the laser linewidth and constant with respect to the optical fiber length, for lasers with high-phase noise, which is consistent with the experimental results. I derive a simplified model that is valid for low-phase-noise lasers. I compare this model with the experimental results and find that it matches the optical-fiber-length-dependent bandwidth measured for low-phase-noise lasers.
Committee: Drs. Gary Carter (Chair), Curtis Menyuk, Fow-sen Choa, Olukayode Okusaga, Weimin Zhou
]]>
Ph.D. Dissertation Defense Rayleigh-Scattering-Induced Noise in Analog RF-Photonic Links James Cahill 3:00pm Tuesday, 7 April 2015, ITE 325b Analog RF-photonic links hold the potential to...
http://www.csee.umbc.edu/2015/04/phd-defense-rayleigh-scattering-induced-noise-in-analog-rf-photonic-links/
https://my3.my.umbc.edu/api/v0/pixel/news/50841/guest@my.umbc.edu/463d52516543c194e97eac0e68429099/api/pixel
defense
electrical-engineering
graduate
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 01 Apr 2015 09:03:43 -0400
CSEE Hi Tea, 3:00pm Friday, 3 April 2015 :-D

The UMBC ACM Student Chapter invites you to Hi Tea this week. Mingle, network, discuss research and ideas, explore opportunities to collaborate and treat yourself to a snack while you’re at it. Faculty, staff and students across the computer science, electrical engineering, computer engineering and cybersecurity programs are encouraged to participate. Friends of the department are also welcome.
Date: Friday, April 3, 2015
Time: 3:00 p.m.- 4:00 p.m.
Location: CSEE hallway outside ITE 325
Hosted by: Chi Zhang
If you or your lab are interested in volunteering for or hosting Hi Tea, please contact Genaro Hernandez Jr. at genaroh1 @ umbc.edu. We need volunteers for 4/17/15 and 4/24/15.
]]>
The UMBC ACM Student Chapter invites you to Hi Tea this week. Mingle, network, discuss research and ideas, explore opportunities to collaborate and treat yourself to a snack while you’re at it....
http://www.csee.umbc.edu/2015/03/csee-hi-tea-300pm-friday-3-april-2015-d/
https://my3.my.umbc.edu/api/v0/pixel/news/50805/guest@my.umbc.edu/ebb6445844b7029380a05232a3ae8502/api/pixel
graduate
news
students
undergraduate
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Mon, 30 Mar 2015 20:25:26 -0400
UMBC CyberDawgs win Mid-Atlantic Regional CCDC Finals

This weekend, UMBC’s Cyber Defense Team (the ‘CyberDawgs’) took first place at the 2015 National CyberWatch Mid-Atlantic Collegiate Cyber Defense Competition (CCDC).
UMBC was one of ten teams that advanced to the regional finals held at the Johns Hopkins Applied Physics Lab on March 25-28. As the first place winner, the CyberDawgs will represent UMBC and the Mid-Atlantic region at the National CCDC in San Antonio, Texas April 24-26, 2015.

According to CyberDawgs president Jacob Rust (CMSC ’16), UMBC maintained a strong lead throughout the event, finishing with a raw score of 1674450 — which was 353400 more points than the second place team. Jacob also reported that UMBC ended the first day solidly in first place and remained in the lead for almost the entire competition.
The final standings for this weekend’s action are:
1st: UMBC 1674450
2nd: UMCP 1321050
3rd: Towson 1159925
The CyberDawgs participating in the MA-CCDC finals were Jacob Rust, Tyler Campbell, Anh Ho, John Beers, Joshua Domangue, Chris Gardner, Julio Valcarcel, and David Young.
 As a highly motivated and self-directed team, this is the first time the CyberDawgs have won MA-CCDC, but certainly will not be the last. We wish the team luck as they prepare to compete in the National CCDC finals!
As a highly motivated and self-directed team, this is the first time the CyberDawgs have won MA-CCDC, but certainly will not be the last. We wish the team luck as they prepare to compete in the National CCDC finals!
Interested in joining the CyberDawgs? Contact Jacob Rust (Sorry, you need javascript to view this email address. ) for more information — they’re always looking for new members! (The team meets weekly on Tuesdays at 7PM in ITE 227.)
The CyberDawg faculty advisors are Dr. Charles Nicholas and Dr. Richard Forno.
]]>
This weekend, UMBC’s Cyber Defense Team (the ‘CyberDawgs’) took first place at the 2015 National CyberWatch Mid-Atlantic Collegiate Cyber Defense Competition (CCDC). UMBC was one of ten teams...
http://www.csee.umbc.edu/2015/03/cyberdawgs-win-mid-atlantic-regional-ccdc-finals/
https://my3.my.umbc.edu/api/v0/pixel/news/50779/guest@my.umbc.edu/0aecf47d7b76719872bea65f5f0f649c/api/pixel
computer-engineering
computer-science
csee
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
56
6
true
Sun, 29 Mar 2015 17:19:26 -0400
Sun, 29 Mar 2015 17:19:26 -0400
talk: Enhancing System Security & Privacy with Program Analysis, 12p Tue 3/31, UMBC
Enhancing System Security and Privacy with Program Analysis
Yinzhi Cao
Columbia University
12:00-1:00pm Tuesday, 31 March 2015, ITE 325b, UMBC
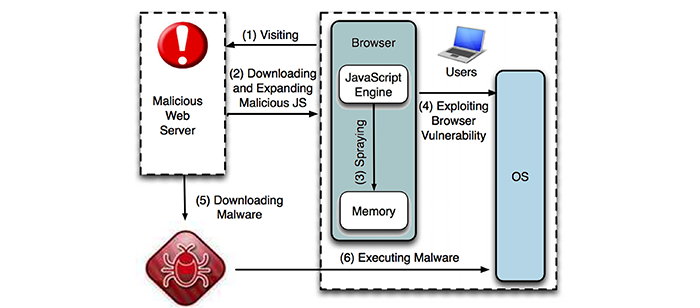
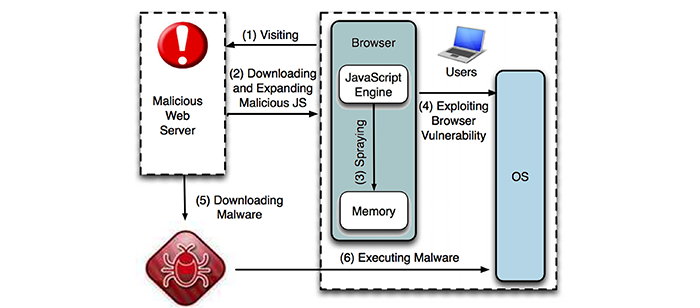
Cyber security and privacy have brought the attention from the general public these days. Melissa Hathaway, who advised both President Obama and President Bush, estimated in a report that governments and consumers lost $125 billion annually to cyber-attacks, including losses in tax revenue. In this talk, from the perspective of program analysis, I will discuss the security and privacy of two important computer systems: Web browser and Android system. In the first part, I will introduce how to prevent and detect drive-by download attacks, which penetrate the boundary of a browser principal. In particular, I will present JShield, a vulnerability-based detection engine that is more robust to obfuscated drive-by download attacks, when compared to various anti-virus software and most recent research papers. In the second part, I will introduce EdgeMiner, the first automatic tool that creates summaries of Android framework in the form of callback and registration pairs. With the summaries, existing static analysis system can correctly construct a control flow graph with hidden control flow dependencies introduced by callback methods.
Yinzhi Cao is a postdoctoral scientist at Columbia University. He earned his PhD in computer science at Northwestern University. Before that, he obtained his B.E. degree in electronics engineering at Tsinghua University in China. His research mainly focuses on the security and privacy of web, smart phones, and machine learning. He has published more than ten papers at various security conferences, such as Oakland, NDSS, ACSAC and DSN. His JShield system has been adopted by Huawei, the world’s largest telecommunication company. In the past, he served as a program committee member for IEEE CNS’14 and web chair for AsiaCCS SESP’13. Previously, he also conducted research at SRI International and UC Santa Barbara as a summer intern.
]]>
Enhancing System Security and Privacy with Program Analysis Yinzhi Cao Columbia University 12:00-1:00pm Tuesday, 31 March 2015, ITE 325b, UMBC Cyber security and privacy have brought the...
http://www.csee.umbc.edu/2015/03/talk-enhancing-system-security-and-privacy-with-program-analysis-noon-tue-331/
https://my3.my.umbc.edu/api/v0/pixel/news/50756/guest@my.umbc.edu/378ad886d00bb56d537a26d7cae00b20/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 27 Mar 2015 09:29:58 -0400
Fri, 27 Mar 2015 09:29:58 -0400
talk: Blind Hashing; securing passwords against offline attack, 11a Fri 3/27 MP101 UMBC
UMBC Cyber Defense Lab
Blind Hashing; a new way to secure
passwords against offline attack
Jeremy Spilman
Founder/CTO of TapLink
11-12 Friday 27 March 2015, M/P 101, UMBC
Industry best practice is to secure passwords using a tunable hashing algorithm; pick the right hashing algorithm, tune its cost factors so it runs slowly and makes optimal use of your hardware, and it’s possible to protect very strong passwords from being cracked. However when average password strength and login latency requirements face off against bot-nets and GPU powered dictionary attacks, the vast majority of passwords are easily cracked. Blind hashing entangles password hashes with a massive pool of random data, so large it cannot be stolen over the network. A simple protocol allows any number of sites to share a centralized petabyte-scale data pool, amortizing the cost for defenders, while protecting low-entropy passwords with minimal run-time cost. Blind hashing can also be used as a general-purpose PBKDF to protect against brute-force attacks, and providing the opportunity to add server-based access policies and revocability to the key derivation process. Following his talk, Jeremy will be happy to discuss potential research opportunities with the company for students interested in developing new implementations of blind hashing for password-based authentication and encryption services.
Jeremy Spilman is the Founder and CTO of TapLink, a startup company that is developing systems using its patented Blind Hashing technique, which can completely protect passwords against offline attack, even if the password database is stolen. He was a double major in Computer Science and Economics at Brandeis University.
]]>
UMBC Cyber Defense Lab Blind Hashing; a new way to secure passwords against offline attack Jeremy Spilman Founder/CTO of TapLink 11-12 Friday 27 March 2015, M/P 101, UMBC Industry best...
http://www.csee.umbc.edu/2015/03/talk-blind-hashing-securing-passwords-against-offline-attack-11a-fri-327-mp101-umbc/
https://my3.my.umbc.edu/api/v0/pixel/news/50722/guest@my.umbc.edu/98819f2b5fd804bc1c88ddd9490578e1/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 25 Mar 2015 00:15:23 -0400
talk: Fei Liu (CMU) Summarizing Information in Big Data, 12p Fri 3/27

Summarizing Information in Big Data: Algorithms and Applications
Dr. Fei Liu
School of Computer Science
Carnegie Mellon University
12:00p Friday, 27 March 2015, ITE 325b
Information floods the lives of modern people, and we find it overwhelming. Summarization systems that identify salient pieces of information and present it concisely can help. In this talk, I will discuss both algorithmic and application perspectives of summarization. Algorithm-wise, I will describe keyword extraction, sentence extraction, and summary generation, including a range of techniques from information extraction to semantic representation of data sources; application-wise, I focus on summarizing human conversations, social media contents, and news articles. The data sources span low-quality speech recognizer outputs and social media chats to high-quality content produced by professional writers. A special focus of my work is exploring multiple information sources. In addition to better integration across sources, this allows abstraction to shared research challenges for broader impact. Finally, I try to identify the missing links in cross-genre summarization studies and discuss future research directions.
Dr. Fei Liu is a postdoctoral fellow at Carnegie Mellon University, member of Noah’s ARK. Fei’s research interests are in the areas of natural language processing, machine learning, and data mining, with special emphasis on automatic summarization and social media. From 2011 to 2013, Fei worked as a Senior Research Scientist at Bosch Research, Palo Alto, California, one of the largest German companies providing intelligent car systems and home appliances. Fei received her Ph.D. in Computer Science from the University of Texas at Dallas in 2011, supported by Erik Jonsson Distinguished Research Fellowship. Prior to that, she obtained her Bachelors and Masters degrees in Computer Science from Fudan University, Shanghai, China. Fei has published over twenty peer reviewed articles, and she serves as a referee for leading journals and conferences.
Host: Nilanjan Banerjee and Mohamed Younis
]]>
Summarizing Information in Big Data: Algorithms and Applications Dr. Fei Liu School of Computer Science Carnegie Mellon University 12:00p Friday, 27 March 2015, ITE 325b Information...
http://www.csee.umbc.edu/2015/03/dr-fei-liu-cmu-summarizing-information-in-big-data-12p-fri-326/
https://my3.my.umbc.edu/api/v0/pixel/news/50719/guest@my.umbc.edu/5f27d92e0396de676c5b597362ebb5f1/api/pixel
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Tue, 24 Mar 2015 23:05:03 -0400
Tue, 24 Mar 2015 23:05:03 -0400
Rick Forno discusses cyber warfare in The Diplomatic Courier

CSEE’s Dr. Rick Forno discussed cyber warfare in Ash Hunt’s latest policy paper ‘Cyber Quantifiable Restrictions: The Requirements to Generate Agreed Restrictions on the Use of Cyber Capabilities’ appearing in The Diplomatic Courier. Among other things, Hunt attempts to show that agreed restrictions should not blanket the use of cyber capabilities, but rather the unacceptable use of a range of capabilities that could be used to harm human life.
Recently, it has become apparent that “we’re in a [cyber] arms race” in a largely unregulated domain—the cyber wild west. With the increased diffusion of technology, nations have begun amassing offensive cyber capabilities: utilizing zero-day exploits, distributed denial of server (DDOS) attacks, and weaponized malware technology. Already, “the U.S. has poured billions of dollars into an electronic arsenal,” whilst the “stockpile of exploits runs into the thousands, aimed at every conceivable device.” This exponential growth of cyber arms is particularly dangerous considering the lack of rules and conventions governing the fifth arena of warfare. Dr. Richard Forno from the University of Maryland concedes, “there is no international agreement over what level of cyber warfare is acceptable.” He further recognizes that national systems such as power grids, water treatment plants and medical facilities “do not have adequate protection from hackers.” Clearly, “principles and agreements on cyber warfare must designate sensitive infrastructure as red lines.” It is necessary to afford our critical organizations the same level of protection from cyber hostility as we do from the multitude of other tangible threats.
Source: The Diplomatic Courier Volume 9, Issue 1, January/February 2015
]]>
CSEE’s Dr. Rick Forno discussed cyber warfare in Ash Hunt’s latest policy paper ‘Cyber Quantifiable Restrictions: The Requirements to Generate Agreed Restrictions on the Use of Cyber Capabilities’...
http://www.csee.umbc.edu/2015/03/rick-forno-discusses-cyber-warfare-in-the-diplomatic-courier/
https://my3.my.umbc.edu/api/v0/pixel/news/50657/guest@my.umbc.edu/2d99631931ecc0ebfee18eb412547f1e/api/pixel
computer-science
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 22 Mar 2015 10:26:09 -0400
Sun, 22 Mar 2015 10:26:09 -0400





 As a highly motivated and self-directed team, this is the first time the CyberDawgs have won MA-CCDC, but certainly will not be the last. We wish the team luck as they prepare to compete in the National CCDC finals!
As a highly motivated and self-directed team, this is the first time the CyberDawgs have won MA-CCDC, but certainly will not be the last. We wish the team luck as they prepare to compete in the National CCDC finals!