UMBC designated a Center of Academic Excellence in Information Assurance

UMBC has been redesignated as a National Center of Academic Excellence in Information Assurance by the National Security Agency and Department of Homeland Security for both Cyber Defense Research (CAE-R) and Education (CAE-IA/CD) for the academic years 2014-2021. UMBC is one of only 38 institutions in the US. that have recognized by NSA and DHS for both education and research.
The CAE educational designation includes (among other elements) a certification that our curriculum satisfies focus areas and knowledge units (KUs) as outlined in the NICE Framework. This framework aims to establish a common lexicon for students, universities, and employers for describing knoweldge and skills needed for various cybersecurity jobs. The CAE research designation signifies UMBC’s demonstrated excellence in conducting quality research activities pertaining to cybersecurity.
The CAE certification process was coordinated by Dr. Alan Sherman through the Center for Information Security and Assurance (CISA). Among other things, CISA oversees UMBC’s Federal CyberCorps Scholarship For Service program and is actively involved with cybersecurity education and research activities at UMBC, to include the upcoming Innovations in Cybersecurity Education Workshop on June 24.
]]>
UMBC has been redesignated as a National Center of Academic Excellence in Information Assurance by the National Security Agency and Department of Homeland Security for both Cyber Defense Research...
http://www.csee.umbc.edu/2014/05/umbc-redesignated-cybersecurity-center-of-excellence/
https://my3.my.umbc.edu/api/v0/pixel/news/44842/guest@my.umbc.edu/2684840aa14e63a0927d2c2ab8874e0d/api/pixel
computer-engineering
computer-science
csee
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Wed, 28 May 2014 10:31:20 -0400
Dr. Rick Forno discusses cyberwar on NPR
In recent days, the United States and China have traded accusations about each nation’s alleged (or actual) espionage activities in cyberspace. Moreover, high-profile events like Stuxnet and recurring high-profile cyber-attacks such as the Target data breach continue to keep ‘cyber’ and cybersecurity issues in the news.
Today, CSEE’s Dr. Rick Forno, Cybersecurity GPD and Assistant Director of the UMBC Center for Cybersecurity, was a guest on PRI’s ‘The World’ where he discussed issues related to cyberwarfare, cybersecurity and the international application of cyberpower.
]]>
In recent days, the United States and China have traded accusations about each nation’s alleged (or actual) espionage activities in cyberspace. Moreover, high-profile events like Stuxnet and...
http://www.csee.umbc.edu/2014/05/dr-rick-forno-discusses-cyberwar-on-npr/
https://my3.my.umbc.edu/api/v0/pixel/news/44836/guest@my.umbc.edu/82fcf2a1eedff9e6e2105426f998fe42/api/pixel
computer-science
cybersecurity
in-the-news
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 27 May 2014 20:21:50 -0400
Tue, 27 May 2014 20:21:50 -0400
Innovations in Cybersecurity Education Workshop, Tue 24 June 2014
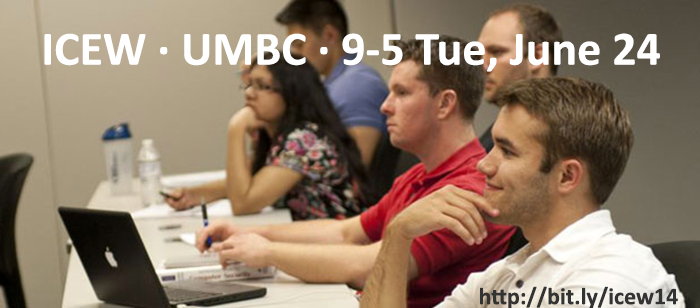
Innovations in Cybersecurity Education Workshop
University of Maryland, Baltimore County
9:30 – 4:30 Tuesday, 24 June 2014
Innovations in Cybersecurity Education is a regional workshop on cybersecurity education at all levels, from Kindergarden through post-graduate. It will include discussions about cyber competitions, hands-on exercises, educational games, and integrating cybersecurity throughout the curriculum. There will be an opportunity to experience hands-on cyber defense exercises and to play new computer security education games, including SecurityEmpire developed at UMBC.
The workshop is free and open to the public — all are welcome to attend. This workshop will to be of interest to educators, school administrators, undergraduate and graduate students, and government officials. Lunch will be provided and there is ample free parking for participants.
Please see the links above for the schedule and location and register to help us plan for the number of participants.
The workshop is organized by Dr. Alan T. Sherman with support provided in part by the National Science Foundation under SFS grant 1241576.
]]>
Home · Schedule · Location · Organizers · Register · Resources Innovations in Cybersecurity Education Workshop University of Maryland, Baltimore County 9:30 – 4:30...
http://www.csee.umbc.edu/2014/05/innovations-in-cybersecurity-education-workshop-tue-24-june-2014/
https://my3.my.umbc.edu/api/v0/pixel/news/44833/guest@my.umbc.edu/85ac91c058c833fda827b43cb4b0b174/api/pixel
cybersecurity
news
teaching-innovation
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 27 May 2014 16:18:08 -0400
Maryland Cybersecurity Roundtable, 1:30pm Thr. May 29

The Maryland Cybersecurity Roundtable will be launched at an open meeting at the Hotel at Arundel Mills Preserve from 1:30-2:30 on Thursday, May 29. Attend to learn about the Roundtable, hear about the organization’s goals and initiatives and discover ways to get involved. RSVP online by May 27.
The Maryland Cybersecurity Roundtable is a premiere forum for the discussion of cybersecurity challenges and solution development, advancement of cyber-related business innovation and growth, programs, policies, and education within Maryland and the region. The Roundtable is dedicated to creating connections and building relationships among current cyber professionals and businesses and fostering the development of the next generation of cyber thought leaders.
]]>
The Maryland Cybersecurity Roundtable will be launched at an open meeting at the Hotel at Arundel Mills Preserve from 1:30-2:30 on Thursday, May 29. Attend to learn about the Roundtable, hear...
http://www.csee.umbc.edu/2014/05/maryland-cybersecurity-roundtable-130pm-thr-may-29/
https://my3.my.umbc.edu/api/v0/pixel/news/44832/guest@my.umbc.edu/202f05f554d749fc433ec963c236651b/api/pixel
cybersecurity
events
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 27 May 2014 15:33:09 -0400
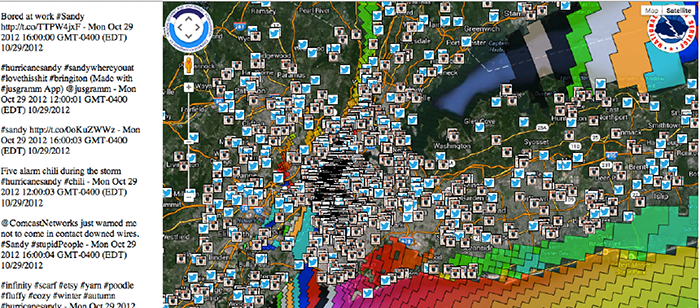
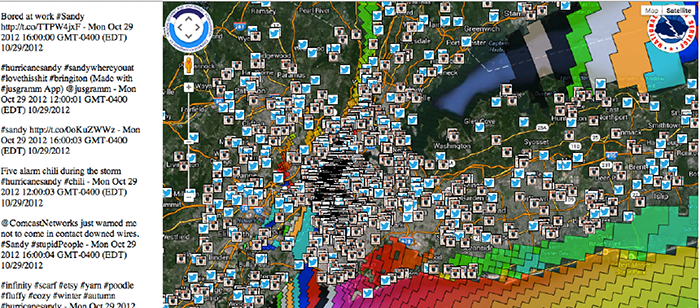
PhD defense: Oleg Aulov, Human Sensor Networks for Disasters, 11am Thr 5/29
Ph.D. Dissertation Defense
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Human Sensor Networks for Disasters
Oleg Aulov
11:00am Thursday, 29 May 2014, ITE325b, UMBC
This dissertation, presents a novel approach that utilizes quantifiable social media data as a human aware near real-time observing system coupled with geophysical predictive models for improved response to disasters and extreme events. It shows that social media data has the potential to significantly improve disaster management beyond informing the public and emphasizes the importance of different roles that social media can play in management, monitoring, modeling and mitigation of natural and human-caused disasters.
In the proposed approach, social media sources are viewed as a Human Sensor Network, and Social Media users are viewed as “human sensors” that are “deployed” in the field, and their posts are considered to be “sensor observations”. I have utilized the “human sensor observations”, i.e. data acquired from social media, as boundary value forcings to show improved geophysical model forecasts of extreme disaster events when combined with other scientific data such as satellite observations and sensor measurements. In addition, I have developed a system called ASON maps that dynamically combines model forecast outputs with specified social media observations and physical measurements to define the regions of event impacts such as flood distributions and levels, beached tarballs, power outages etc. Real time large datasets were collected, archived and are available for following recent extreme disasters events as use case scenarios.
In the case of the Deepwater Horizon oil spill disaster of 2010 that devastated the Gulf of Mexico, the research demonstrates how social media data can be used as a boundary forcing condition of the oil spill plume forecast model, and results in an order of magnitude forecast improvement. In the case of Hurricane Sandy NY/NJ landfall impact of 2012, owing to inherent uncertainties in the weather forecasts, the NOAA operational surge model only forecasts the worst-case scenario for flooding from any given hurricane. This dissertation demonstrates how the model forecasts, when combined with social media data in a single framework, can be used for near-real time forecast validation, damage assessment and disaster management. Geolocated and time-stamped photos allow near real-time assessment of the surge levels at different locations, which can validate model forecasts give timely views of the actual levels of surge, as well as provide an upper bound regional street level maps beyond which the surge did not spread. In the case of the Tohoku Earthquake and Tsunami of 2011, social media aspects of handheld devices such as Geiger counters that can potentially detect radioactive debris are discussed as well.
Committee: Dr. Milton Halem (chair), Tim Finin, Anupam Joshi, James Smith, Yelena Yesha
]]>
Ph.D. Dissertation Defense Computer Science and Electrical Engineering University of Maryland, Baltimore County Human Sensor Networks for Disasters Oleg Aulov 11:00am Thursday, 29 May...
http://www.csee.umbc.edu/2014/05/phd-defense-oleg-aulov-human-sensor-networks-for-disasters-11am-thr-529/
https://my3.my.umbc.edu/api/v0/pixel/news/44776/guest@my.umbc.edu/3c5021bfcb23f9c60728760842a63e58/api/pixel
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 21 May 2014 07:43:04 -0400
Summer internship with Concurrent Technologies Corp., Annapolis Junction
Concurrent Technologies Corporation (http://www.ctc.com/) is trying to fill a internship with an undergrad with good software skills to start as soon as possible in their Annapolis Junction, MD facility. If you meet the qualifications and are interested, please follow the directions at the end of this announcement.
—
Are you ready to start your career at a corporation with a respected national reputation for solving complex technical challenges? Become a part of our team. Concurrent Technologies Corporation (CTC) has an opportunity for qualified Software Development Intern.
SOFTWARE DEVELOPMENT INTERN
Primary Responsibilities: CTC is offering a Participative Internship Program (PIP), which is a twelve week, technically focused group internship experience. The PIP is a mix of direct project work coupled with a relevant research project and end of internship presentation. It is a structured internship program providing student mentorship, leadership, technical subject matter expertise, and competency development opportunities.
The research project will include an evaluation of leading edge cloud, mobile, and virtual application based solutions enabling the integration and/or mobility of CTC’s highly scalable Cross Domain Solutions.
Basic Qualifications:
• Qualifying applicants should have course expertise in software development and best practices.
• Should be capable of handling multiple roles (development of software, writing test plans and test cases, requirements traceability, leading test teams) in a team-based environment.
• Currently pursuing a Bachelor of Science Degree in Computer Science or related discipline.
• Must have course familiarity with object-oriented software design and development using languages such as VBA, Java, C and/or C++ and basic computer networking knowledge and Familiarity with iOS and Android development.
• Hadoop, Groovy, Graph Database, iOS, Android and MongoDB experience are considered a plus.
Clearance: U.S. Citizenship.
Join us! Qualified candidates should submit their resumes online at:
http://careers.ctc.com
Email: Sorry, you need javascript to view this email address. or Sorry, you need javascript to view this email address.
Reference Code: SR # 2014-0064
EOE, M/F/D/V
]]>
Concurrent Technologies Corporation (http://www.ctc.com/) is trying to fill a internship with an undergrad with good software skills to start as soon as possible in their Annapolis Junction, MD...
http://www.csee.umbc.edu/2014/05/summer-internship-with-concurrent-technologies-corp-annapolis-junction/
https://my3.my.umbc.edu/api/v0/pixel/news/44775/guest@my.umbc.edu/863a550d0fd476bda4c3e2826662d259/api/pixel
in-the-news
jobs
students
undergraduate
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 20 May 2014 22:43:57 -0400
Tue, 20 May 2014 22:43:57 -0400
UMBC Knights 2014

The 2014 UMBC team preparing for the match at the New York Athletic Club.
UMBC student Nicholas Pascarella created a short video on UMBC’s chess program and the current team, including its participation in the 2014 Final Four of College Chess match held at the New York Athletic Club in April. This match has been held each year since 2001 and determines the U.S. college team chess champion. In the 14 years that it has been held, UMBC has won six times and placed second six times.
Nicholas is a rising junior majoring in Media and Communication Studies.
]]>
The 2014 UMBC team preparing for the match at the New York Athletic Club. UMBC student Nicholas Pascarella created a short video on UMBC’s chess program and the current team, including...
http://www.csee.umbc.edu/2014/05/umbc-knights-2014/
https://my3.my.umbc.edu/api/v0/pixel/news/44758/guest@my.umbc.edu/810a51bb5debff5a1d3207fe87ddaeec/api/pixel
chess
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 19 May 2014 23:13:19 -0400
Ph.D. student Omar Shehab receives travel grants
UMBC graduate student Omar Shehab received a travel grant to attend two co-located events, the 14th Canadian Quantum Information Summer School and the 11th Canadian Quantum Information Student Conference. Both events are organized by the Fields Institute and will be held at the University of Guelph.
Omar is a fourth year PhD student in Computer Science working with by Professor Samuel Lomonaco. His Ph.D.research involves determining the quantum computational complexity of topological problems. He is also interested in quantum games, randomness and cryptography. This summer he will be working as a Visiting Research Assistant the USC Information Sciences Institute facility in Arlington, Virginia.
]]>
UMBC graduate student Omar Shehab received a travel grant to attend two co-located events, the 14th Canadian Quantum Information Summer School and the 11th Canadian Quantum Information Student...
http://www.csee.umbc.edu/2014/05/ph-d-student-omar-shehab-receives-travel-grants/
https://my3.my.umbc.edu/api/v0/pixel/news/44756/guest@my.umbc.edu/3d1b2da6e9671d1ed3ec2218cb04b1c0/api/pixel
graduate
news
research
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 19 May 2014 15:18:52 -0400
Primer on cybersecurity and public policy for nonspecialists
The Computer Science and Telecommunications Board (CSTB) of the National Academies has released of a report entitled At the Nexus of Cybersecurity and Public Policy: Some Basic Concepts and Issues in prepublication form. The final book version of the report will be available around end of May, and a PDF of that final version will also be available for free at this web site.
According to the study director and CSTB chief scientist Dr. Herb Lin, “This report is a first for CSTB in that it seeks to distill the cybersecurity wisdom and insight of this entire body of Academy work in a form that is easily accessible to nonspecialists. It provides the essential technical background for understanding cyber threats and the basic principles of cybersecurity, and is pretty much self-contained in this regard. At the same time, it underscores the point that improvements in cybersecurity depend at least as much on non-technical factors, based in fields such as economics and psychology, as on secure code or tamper-resistant hardware.”
National Research Council. At the Nexus of Cybersecurity and Public Policy: Some Basic Concepts and Issues. Washington, DC: The National Academies Press, 2014. ( Download )
We depend on information and information technology (IT) to make many of our day-to-day tasks easier and more convenient. Computers play key roles in transportation, health care, banking, and energy. Businesses use IT for payroll and accounting, inventory and sales, and research and development. Modern military forces use weapons that are increasingly coordinated through computer-based networks. Cybersecurity is vital to protecting all of these functions. Cyberspace is vulnerable to a broad spectrum of hackers, criminals, terrorists, and state actors. Working in cyberspace, these malevolent actors can steal money, intellectual property, or classified information; impersonate law-abiding parties for their own purposes; damage important data; or deny the availability of normally accessible services. Cybersecurity issues arise because of three factors taken together – the presence of malevolent actors in cyberspace, societal reliance on IT for many important functions, and the presence of vulnerabilities in IT systems. What steps can policy makers take to protect our government, businesses, and the public from those would take advantage of system vulnerabilities?
At the Nexus of Cybersecurity and Public Policy offers a wealth of information on practical measures, technical and nontechnical challenges, and potential policy responses. According to this report, cybersecurity is a never-ending battle; threats will evolve as adversaries adopt new tools and techniques to compromise security. Cybersecurity is therefore an ongoing process that needs to evolve as new threats are identified. At the Nexus of Cybersecurity and Public Policy is a call for action to make cybersecurity a public safety priority. For a number of years, the cybersecurity issue has received increasing public attention; however, most policy focus has been on the short-term costs of improving systems. In its explanation of the fundamentals of cybersecurity and the discussion of potential policy responses, this book will be a resource for policy makers, cybersecurity and IT professionals, and anyone who wants to understand threats to cyberspace.
]]>
[Video] The Computer Science and Telecommunications Board (CSTB) of the National Academies has released of a report entitled At the Nexus of Cybersecurity and Public Policy: Some Basic Concepts...
http://www.csee.umbc.edu/2014/05/primer-on-cybersecurity-and-public-policy-for-nonspecialists/
https://my3.my.umbc.edu/api/v0/pixel/news/44744/guest@my.umbc.edu/74f39e566156a77af7649f0e89a2ab52/api/pixel
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 17 May 2014 23:04:07 -0400
PhD defense: Lushan Han, Schema Free Querying of Semantic Data, 10am Fri 5/23
Ph.D.Dissertation Defense
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Schema Free Querying of Semantic Data
Lushan Han
10:00am Friday, 23 May 2014, ITE 325b
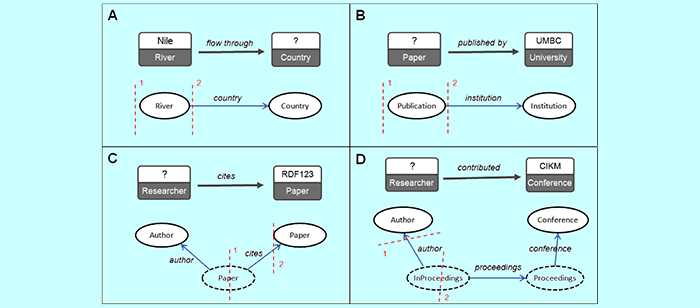
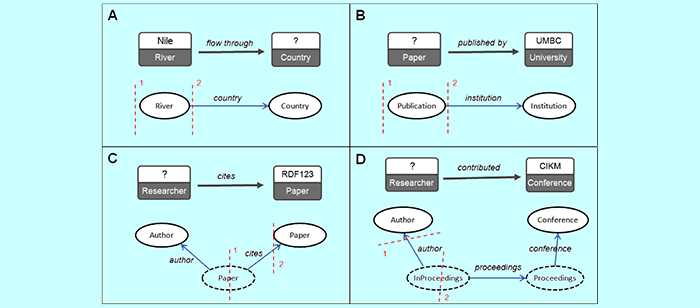
Developing interfaces to enable casual, non-expert users to query complex structured data has been the subject of much research over the past forty years. We refer to them as as schema-free query interfaces, since they allow users to freely query data without understanding its schema, knowing how to refer to objects, or mastering the appropriate formal query language. Schema-free query interfaces address fundamental problems in natural language processing, databases and AI to connect users’ conceptual models and machine representations.
However, schema-free query interface systems are faced with three hard problems. First, we still lack a practical interface. Natural Language Interfaces (NLIs) are easy for users but hard for machines. Current NLP techniques are still unreliable in extracting the relational structure from natural language questions. Keyword query interfaces, on the other hand, have limited expressiveness and inherit ambiguity from the natural language terms used as keywords. Second, people express or model the same meaning in many different ways, which can result in the vocabulary and structure mismatches between users’ queries and the machines’ representation. We still rely on ad hoc and labor-intensive approaches to deal with this ‘semantic heterogeneity problem’. Third, the Web has seen increasing amounts of open domain semantic data with heterogeneous or unknown schemas, which challenges traditional NLI systems that require a well-defined schema. Some modern systems gave up the approach of translating the user query into a formal query at the schema level and chose to directly search into the entity network (ABox) for the matchings of the user query. This approach, however, is computationally expensive and has an ad hoc nature.
In this thesis, we develop a novel approach to address the three hard problems. We introduce a new schema-free query interface, SFQ interface, in which users explicitly specify the relational structure of the query as a graphical “skeleton” and annotate it with freely chosen words, phrases and entity names. This circumvents the unreliable step of extracting complete relations from natural language queries.
We describe a framework for interpreting these SFQ queries over open domain semantic data that automatically translates them to formal queries. First, we learn a schema statistically from the entity network and represent as a graph, which we call the schema network. Our mapping algorithms run on the schema network rather than the entity network, enhancing scalability. We define the probability of “observing” a path on the schema network. Following it, we create two statistical association models that will be used to carry out disambiguation. Novel mapping algorithms are developed that exploit semantic similarity measures and association measures to address the structure and vocabulary mismatch problems. Our approach is fully computational and requires no special lexicons, mapping rules, domain-specific syntactic or semantic grammars, thesauri or hard-coded semantics.
We evaluate our approach on two large datasets, DBLP+ and DBpedia. We developed DBLP+ by augmenting the DBLP dataset with additional data from CiteSeerX and ArnetMiner. We created 220 SFQ queries on the DBLP+ dataset. For DBpedia, we had three human subjects (who were unfamiliar with DBpedia) translate 33 natural language questions from the 2011 QALD workshop into SFQ queries. We carried out cross-validation on the 220 DBLP+ queries and cross-domain validation on the 99 DBpedia queries in which the parameters tuned for the DBLP+ queries are applied to the DBpedia queries. The evaluation results on the two datasets show that our system has very good efficacy and efficiency.
Committee: Drs. Li Ding (Memect), Tim Finin (chair), Anupam Joshi, Paul McNamee (JHU), Yelena Yesha
]]>
Ph.D.Dissertation Defense Computer Science and Electrical Engineering University of Maryland, Baltimore County Schema Free Querying of Semantic Data Lushan Han 10:00am Friday, 23 May...
http://www.csee.umbc.edu/2014/05/defense-lushan-han-schema-free-querying-of-semantic-data-10am-fri-523/
https://my3.my.umbc.edu/api/v0/pixel/news/44742/guest@my.umbc.edu/781cb82ef3839dc023aa0a01e9fa8cba/api/pixel
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 17 May 2014 16:30:09 -0400