Defense: Feature Extraction and Fusion for Supervised and Semi-supervised Classification: Application to fMRI and LTM Data
Dissertation Defense
Feature Extraction and Fusion for Supervised and Semi-supervised
Classification: Application to fMRI and LTM Data
Wei Du
2:00pm Thursday, 24 April 2014, ITE 325B
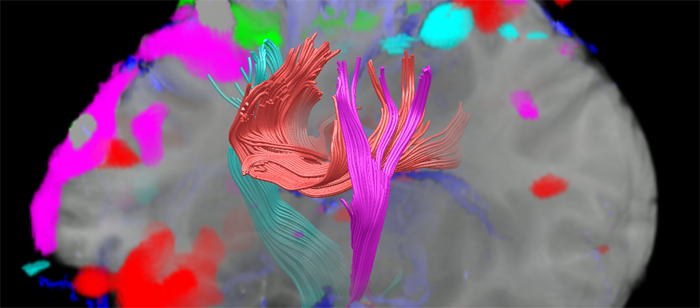
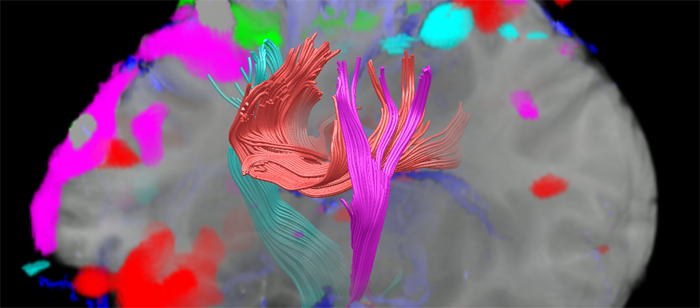
Extracting powerful features from high dimensional noisy data promises to significantly improve the effectiveness of further analysis, especially of classification. Since there is no single feature selection and extraction method or classifier that works best on all given problems, developing effective and efficient feature selection and extraction methods and classifiers for specific applications has became one of the most active areas in the machine learning field. The aim of this dissertation is to develop novel data-driven methods for extracting and selecting the most distinguishing features for performing classification using functional magnetic resonance imaging (fMRI) and laser tread mapping (LTM) tire data.
FMRI data have the potential to characterize and classify various brain disorders including schizophrenia. However, the high dimensionality and unknown nature of fMRI data present numerous challenges to accurate analysis and interpretation. Independent component analysis (ICA), as a data-driven method, has proven very useful for fMRI analysis in extracting spatial components as multivariate features used in classification, and more recently, for the analysis of fMRI data in its native complex-valued form. In this dissertation, we first present a novel framework to extract powerful features from components estimated by ICA, allowing us to remove the redundancy and retain the most discriminative activation patterns from multivariate ICA features. We apply the proposed three-phase feature extraction framework to two real-valued fMRI data sets, and achieve high classification rates in discriminating healthy controls from patients with schizophrenia. Second, due to the iterative nature of ICA algorithms, typically independent components (ICs) are not estimated consistently during different ICA runs, and hence it is not clear which result to use further. We present a statistical framework that utilizes an objective criterion to select the best of multiple ICA runs such that the multivariate ICA features from the best run can be used for further analysis and inference. Using the proposed framework, we study the performance of a novel complex ICA algorithm for fMRI analysis, entropy rate bound minimization, which takes all three types of diversity into account, including non-Gaussianity, sample dependence and noncircularity that are present in the complex-valued fMRI data. We show that CERBM leads to significant improvement in ICs that provide higher classification accuracy, and thus is a promising ICA algorithm for the analysis of complex-valued fMRI data.
Classification using LTM data is another problem we address where we first study the use of highly multivariate solutions such as ICA and then note the advantages using lower-level features for classification. In this case, an important problem is the selection of best set of features for the best classification performance. Additionally, there are a large amount of unlabeled tire data that are easy to collect but only a few of them can be easily labeled by expert. In this dissertation, we propose a novel mutual information (MI) based approach to achieve feature splits for co-training, a practical and powerful data-driven method in semi-supervised learning. Inspired by the idea of dependent component analysis, the proposed MI-based approach presents feature splits that are maximally independent between- or within- subsets, and thus selects and fuses features more effectively than other feature split methods. Experimental results on both simulated study and LTM tire data indicate that co-training with MI-based feature splits yields significantly higher accuracy than supervised classification.
Committee: Profs. Tulay Adali (Chair), Joel Morris, Janet Rutledge, Charles E. Laberge, Vince D. Calhoun (University of New Mexico and the Mind Research Network), and Dr. Matthew Anderson (Northrop Grumman Corp.)
]]>
Dissertation Defense Feature Extraction and Fusion for Supervised and Semi-supervised Classification: Application to fMRI and LTM Data Wei Du 2:00pm Thursday, 24 April 2014, ITE 325B...
http://www.csee.umbc.edu/2014/04/defense-feature-extraction-and-fusion-for-supervised-and-semi-supervised-classification-application-to-fmri-and-ltm-data/
https://my3.my.umbc.edu/api/v0/pixel/news/43889/guest@my.umbc.edu/bd7e3827cbf460e70bd82781aac32c15/api/pixel
defense
electrical-engineering
graduate
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 23 Apr 2014 23:50:08 -0400
UMBC Cybersecurity MPS Alumna Nidhi Mittal
Nidhi Mittal, a 2013 graduate of UMBC’s Cybersecurity Master’s in Professional Studies program talks about her experience. In this video Ms. Mital talks about the value of the cybersecurity program’s instructors, who bring with them a wealth of experience in the public and private sector.
UMBC offers a variety of master’s degree and certificate options. Our cybersecurity graduate programs leverage a student’s experience toward a range of opportunities within the cybersecurity profession. UMBC’s in-person cybersecurity programs are designed to prepare computer science, information systems, and other experienced professionals to fill management and leadership roles in cybersecurity and cyber operations.
]]>
Click for video Nidhi Mittal, a 2013 graduate of UMBC’s Cybersecurity Master’s in Professional Studies program talks about her experience. In this video Ms. Mital talks about the value of...
http://www.csee.umbc.edu/2014/04/umbc-cybersecurity-mps-alumna-nidhi-mittal/?utm_source=rss&utm_medium=rss&utm_campaign=umbc-cybersecurity-mps-alumna-nidhi-mittal
https://my3.my.umbc.edu/api/v0/pixel/news/43802/guest@my.umbc.edu/6bc67428fad52e94e61aa8179c11220a/api/pixel
cybersecurity
graduate
meet-the-students
news
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 22 Apr 2014 10:16:26 -0400
UMBC Cybersecurity MPS Alumna Nidhi Mittal
Nidhi Mittal, a 2013 graduate of UMBC’s Cybersecurity Master’s in Professional Studies program talks about her experience. In this video Ms. Mital talks about the value of the cybersecurity program’s instructors, who bring with them a wealth of experience in the public and private sector.
UMBC offers a variety of master’s degree and certificate options. Our cybersecurity graduate programs leverage a student’s experience toward a range of opportunities within the cybersecurity profession. UMBC’s in-person cybersecurity programs are designed to prepare computer science, information systems, and other experienced professionals to fill management and leadership roles in cybersecurity and cyber operations.
]]>
Click for video Nidhi Mittal, a 2013 graduate of UMBC’s Cybersecurity Master’s in Professional Studies program talks about her experience. In this video Ms. Mital talks about the value of...
http://www.csee.umbc.edu/2014/04/umbc-cybersecurity-mps-alumna-nidhi-mittal/
https://my3.my.umbc.edu/api/v0/pixel/news/43866/guest@my.umbc.edu/82d0d9455797bbf6e80d98baafdd206e/api/pixel
cybersecurity
graduate
meet-the-students
news
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 22 Apr 2014 10:16:26 -0400
Jane Gethmann receives outstanding non-exempt staff award
CSEE’s Jane Gethmann, Assistant to the Chair, received UMBC’s inaugural Karen L. Wensch Endowment Award for Outstanding Non-Exempt Staff earlier this month. She has played a leadership role in our Department since she joined it in 1997 and has been a key staff member for the thousands of faculty, staff and students who have been part of our department in the past 17 years.
The following is the citation for her well deserved award.

Jane Gethmann first came to UMBC in 1971, and over the years has worked in Financial Aid, the Department of Biological Sciences, and the Graduate School. She joined the Department of Computer Science and Electrical Engineering in 1997, and is known as the glue that holds the department together, going above and beyond her responsibilities.
In addition to assisting the chair and handling administrative and financial duties, Gethmann also takes the lead when additional resources are needed or when she sees a way to increase efficiency in the department. She has served as facilities manager and scheduling coordinator, managed the Computer Science Help Center, coordinated part-time faculty hiring, and created a graduate admissions database. She also managed the installation of a new teaching laboratory, working with faculty and Facilities Management in order to get it up and running by the start of the semester.
A leader and trusted advisor, Gethmann’s vast knowledge of UMBC and departmental procedures as well as her excellent judgment make her invaluable to those she serves. She is a dedicated people person with a helpful and positive attitude. Whether working with faculty, staff, students, or visitors, her goal is to help people solve whatever problem they are facing, and ensure that they have what they need.
Jane plans to retire at the end of this academic year. We will miss her and all that that she has done for UMBC and our department.
]]>
click for video CSEE’s Jane Gethmann, Assistant to the Chair, received UMBC’s inaugural Karen L. Wensch Endowment Award for Outstanding Non-Exempt Staff earlier this month. She has played a...
http://www.csee.umbc.edu/2014/04/jane-gethmann-receives-outstanding-non-exempt-staff-award/?utm_source=rss&utm_medium=rss&utm_campaign=jane-gethmann-receives-outstanding-non-exempt-staff-award
https://my3.my.umbc.edu/api/v0/pixel/news/43766/guest@my.umbc.edu/674d18b12c32cc6effa8f9c8eff24659/api/pixel
csee
faculty-and-staff
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
5
2
true
Mon, 21 Apr 2014 08:48:02 -0400
Jane Gethmann receives outstanding non-exempt staff award
CSEE’s Jane Gethmann, Assistant to the Chair, received UMBC’s inaugural Karen L. Wensch Endowment Award for Outstanding Non-Exempt Staff earlier this month. She has played a leadership role in our Department since she joined it in 1997 and has been a key staff member for the thousands of faculty, staff and students who have been part of our department in the past 17 years.
The following is the citation for her well deserved award.

Jane Gethmann first came to UMBC in 1971, and over the years has worked in Financial Aid, the Department of Biological Sciences, and the Graduate School. She joined the Department of Computer Science and Electrical Engineering in 1997, and is known as the glue that holds the department together, going above and beyond her responsibilities.
In addition to assisting the chair and handling administrative and financial duties, Gethmann also takes the lead when additional resources are needed or when she sees a way to increase efficiency in the department. She has served as facilities manager and scheduling coordinator, managed the Computer Science Help Center, coordinated part-time faculty hiring, and created a graduate admissions database. She also managed the installation of a new teaching laboratory, working with faculty and Facilities Management in order to get it up and running by the start of the semester.
A leader and trusted advisor, Gethmann’s vast knowledge of UMBC and departmental procedures as well as her excellent judgment make her invaluable to those she serves. She is a dedicated people person with a helpful and positive attitude. Whether working with faculty, staff, students, or visitors, her goal is to help people solve whatever problem they are facing, and ensure that they have what they need.
Jane plans to retire at the end of this academic year. We will miss her and all that that she has done for UMBC and our department.
]]>
click for video CSEE’s Jane Gethmann, Assistant to the Chair, received UMBC’s inaugural Karen L. Wensch Endowment Award for Outstanding Non-Exempt Staff earlier this month. She has played a...
http://www.csee.umbc.edu/2014/04/jane-gethmann-receives-outstanding-non-exempt-staff-award/
https://my3.my.umbc.edu/api/v0/pixel/news/43867/guest@my.umbc.edu/1002f0bf08e7fd5501b742fdf8426fe4/api/pixel
csee
faculty-and-staff
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 21 Apr 2014 08:48:02 -0400
ACM uses online end-to-end verifiable voting system in 2014 elections
We were happy to see that ACM is using the Helios online voting system for a number its elections this year, including the 2014 ACM Council election. ACM members, all 100,000 of them, have the option of voting online via the Web or requesting a paper ballot in the election of ACM’s top officers. This demonstrates the confidence that the “world’s largest educational and scientific computing society” has in the technology of online verifiable voting systems.
Helios is an example of an end-to-end verifiable voting system that uses cryptographic techniques that can provide ballot privacy as well as high confidence that errors and fraud will be detected and that the election outcome is correct. Such systems let voters verify that their votes were not modified and were counted without revealing which candidates were voted for. In some cases, they allow anyone to determine that all of an election’s ballots have been correctly counted and also help prevent coercion and vote selling by making it impossible for a voter to prove how she voted to a third party.
Among the things we like about Helios is that it provides a free service that anyone can use to hold end-to-end verifiable votes on the Web and that its code is open sourced, allowing one to study the (mostly Python) code and install and run it on their own computers.
Developing verifiable voting systems has been one of the research activities of UMBC’s Center for Information Security and Assurance for more than six years. Professor Alan Sherman and his students contributed to Scantegrity, the first end-to-end verifiable voting system used in a binding municipal election. The UMBC team oversaw that first use in the Takoma Park, Maryland municipal election in November, 2009. A subsequent system, Remotegrity, was used to allow Takoma Park residents to submit absentee ballots over the Internet in the November 2011 Takoma Park election. A current secure voting project in Professor Sherman’s lab is led by Ph.D. student Christopher Nguyen, who is developing techniques to support random-sample elections.
]]>
We were happy to see that ACM is using the Helios online voting system for a number its elections this year, including the 2014 ACM Council election. ACM members, all 100,000 of them, have the...
http://www.csee.umbc.edu/2014/04/acm-uses-online-end-to-end-verifiable-voting-system-in-2014-elections/?utm_source=rss&utm_medium=rss&utm_campaign=acm-uses-online-end-to-end-verifiable-voting-system-in-2014-elections
https://my3.my.umbc.edu/api/v0/pixel/news/43762/guest@my.umbc.edu/bb334fd6de9ba0818637e29741b7629d/api/pixel
computer-science
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 20 Apr 2014 15:24:08 -0400
ACM uses online end-to-end verifiable voting system in 2014 elections
We were happy to see that ACM is using the Helios online voting system for a number its elections this year, including the 2014 ACM Council election. ACM members, all 100,000 of them, have the option of voting online via the Web or requesting a paper ballot in the election of ACM’s top officers. This demonstrates the confidence that the “world’s largest educational and scientific computing society” has in the technology of online verifiable voting systems.
Helios is an example of an end-to-end verifiable voting system that uses cryptographic techniques that can provide ballot privacy as well as high confidence that errors and fraud will be detected and that the election outcome is correct. Such systems let voters verify that their votes were not modified and were counted without revealing which candidates were voted for. In some cases, they allow anyone to determine that all of an election’s ballots have been correctly counted and also help prevent coercion and vote selling by making it impossible for a voter to prove how she voted to a third party.
Among the things we like about Helios is that it provides a free service that anyone can use to hold end-to-end verifiable votes on the Web and that its code is open sourced, allowing one to study the (mostly Python) code and install and run it on their own computers.
Developing verifiable voting systems has been one of the research activities of UMBC’s Center for Information Security and Assurance for more than six years. Professor Alan Sherman and his students contributed to Scantegrity, the first end-to-end verifiable voting system used in a binding municipal election. The UMBC team oversaw that first use in the Takoma Park, Maryland municipal election in November, 2009. A subsequent system, Remotegrity, was used to allow Takoma Park residents to submit absentee ballots over the Internet in the November 2011 Takoma Park election. A current secure voting project in Professor Sherman’s lab is led by Ph.D. student Christopher Nguyen, who is developing techniques to support random-sample elections.
]]>
We were happy to see that ACM is using the Helios online voting system for a number its elections this year, including the 2014 ACM Council election. ACM members, all 100,000 of them, have the...
http://www.csee.umbc.edu/2014/04/acm-uses-online-end-to-end-verifiable-voting-system-in-2014-elections/
https://my3.my.umbc.edu/api/v0/pixel/news/43868/guest@my.umbc.edu/97f8cbc9672e950badc294390504ee33/api/pixel
computer-science
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 20 Apr 2014 15:24:08 -0400
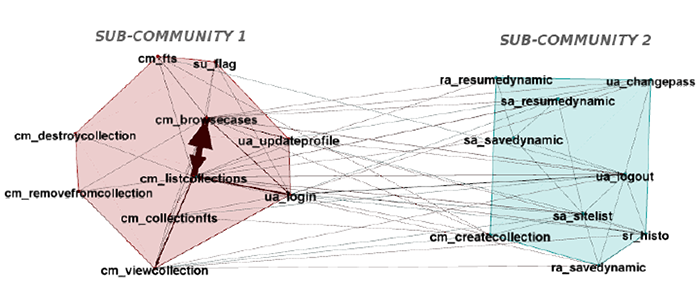
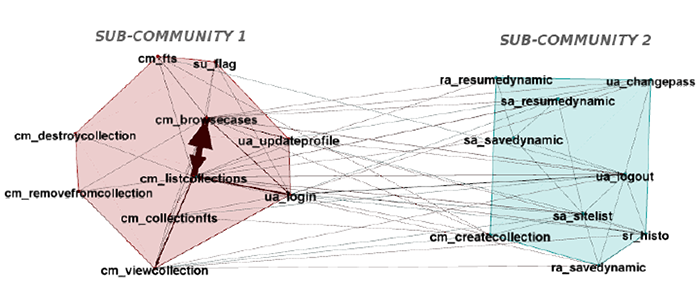
defense: Learning Hierarchical Workflows Using Community Detection, 4/18
MS Thesis Defense
Learning Hierarchical Workflows Using Community Detection
Akshay Peshave
1:00pm Friday, 18 April 2014, ITE 325b
Workflows identified from user event logs and click-stream data are useful as knowledge bases for behavioral analysis and recommendation systems. In this study we identify abstractions or summaries of event logs modeled as user activity flow networks. The abstractions are identified based on structural properties as well as user activity flow dynamics over the network using community detection methods. We apply a fast modularity optimization and multi-level resolution approach to detect hierarchical community structure in user activity flow networks. The detected communities are compared to those detected by the information-theoretic map equation minimization approach to weigh pros and cons of the fast modularity optimization approach in the workflows context. We further attempt to identify the most probable sources and sinks of user activity in individual communities and trim the network accordingly to reduce entropy of the workflow abstractions.
Committee: Drs. Tim Oates (chair), Matt Schmill and Tim Finin
]]>
MS Thesis Defense Learning Hierarchical Workflows Using Community Detection Akshay Peshave 1:00pm Friday, 18 April 2014, ITE 325b Workflows identified from user event logs and click-stream...
http://www.csee.umbc.edu/2014/04/defense-learning-hierarchical-workflows-using-community-detection-418/?utm_source=rss&utm_medium=rss&utm_campaign=defense-learning-hierarchical-workflows-using-community-detection-418
https://my3.my.umbc.edu/api/v0/pixel/news/43727/guest@my.umbc.edu/c99f8a59d37a8c6ab66a0c89d9fdbc6c/api/pixel
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 18 Apr 2014 00:16:53 -0400
defense: Learning Hierarchical Workflows Using Community Detection, 4/18
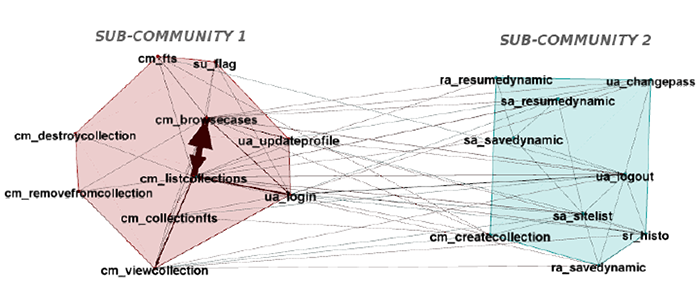
MS Thesis Defense
Learning Hierarchical Workflows Using Community Detection
Akshay Peshave
1:00pm Friday, 18 April 2014, ITE 325b
Workflows identified from user event logs and click-stream data are useful as knowledge bases for behavioral analysis and recommendation systems. In this study we identify abstractions or summaries of event logs modeled as user activity flow networks. The abstractions are identified based on structural properties as well as user activity flow dynamics over the network using community detection methods. We apply a fast modularity optimization and multi-level resolution approach to detect hierarchical community structure in user activity flow networks. The detected communities are compared to those detected by the information-theoretic map equation minimization approach to weigh pros and cons of the fast modularity optimization approach in the workflows context. We further attempt to identify the most probable sources and sinks of user activity in individual communities and trim the network accordingly to reduce entropy of the workflow abstractions.
Committee: Drs. Tim Oates (chair), Matt Schmill and Tim Finin
]]>
MS Thesis Defense Learning Hierarchical Workflows Using Community Detection Akshay Peshave 1:00pm Friday, 18 April 2014, ITE 325b Workflows identified from user event logs and click-stream...
http://www.csee.umbc.edu/2014/04/defense-learning-hierarchical-workflows-using-community-detection-418/
https://my3.my.umbc.edu/api/v0/pixel/news/43869/guest@my.umbc.edu/f0772c96b78e4cd73b4252ece960614b/api/pixel
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 18 Apr 2014 00:16:53 -0400
talk: Translational Bioinformatics Approaches to Evaluate and Implement Genomic Medicine Programs, 1pm 4/25

Translational Bioinformatics Approaches to Evaluate
and Implement Genomic Medicine Programs
Dr. Casey Overby, Assistant Professor
Program for Personalized and Genomic Medicine
University of Maryland – Baltimore
1:00pm Friday, 25 April 2014, ITE 325b, UMBC
There is a growing evidence base to support the use of many genomic applications in healthcare. There are, however, several barriers to healthcare providers making use of genomic data and information on a routine basis. In this talk, I will describe some of our challenges and successes with implementing genomic medicine programs within the Program for Personalized and Genomic Medicine at UMB, introduce one way to conceptualize translational research and translational bioinformatics in this context, describe a proposed model for evaluating and implementing genomic medicine programs, and describe some of my current and planned research in translational bioinformatics.
Casey L. Overby is an Assistant Professor of Medicine in the Program for Personalized and Genomic Medicine and the Center for Health-related Informatics and Bio-Imaging at the University of Maryland School of Medicine. She received her Masters of Biotechnology from the University of Pennsylvania in 2006, her PhD in Biomedical and Health Informatics and a Graduate Certificate in Public Health Genetics from the University of Washington in 2011. In 2013, she completed her post-doctoral training in the Department of Biomedical Informatics at Columbia University and started her position at University of Maryland, Baltimore.
Host: Marie desJardins, Sorry, you need javascript to view this email address.
]]>
Translational Bioinformatics Approaches to Evaluate and Implement Genomic Medicine Programs Dr. Casey Overby, Assistant Professor Program for Personalized and Genomic Medicine University of...
http://www.csee.umbc.edu/2014/04/talk-translational-bioinformatics-approaches-to-evaluate-and-implement-genomic-medicine-programs-1pm-425/?utm_source=rss&utm_medium=rss&utm_campaign=talk-translational-bioinformatics-approaches-to-evaluate-and-implement-genomic-medicine-programs-1pm-425
https://my3.my.umbc.edu/api/v0/pixel/news/43726/guest@my.umbc.edu/d1ef68d2adb2706bc8b6396913a7c951/api/pixel
bioinformatics
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 17 Apr 2014 23:28:57 -0400
Thu, 17 Apr 2014 23:28:57 -0400