talk: Pescatore on Understanding Cybersecurity Market Dynamics, 3/4

Understanding Cybersecurity Market Dynamics
John Pescatore
SANS Institute
1:00-3:00 Tuesday, 4 March 2014
Suite 130, bwtech@UMBC, 5520 Research Park Drive, UMBC
There is no single cybersecurity market, and the factors that drive business decisions around security practices and purchases are complex and continually evolving. Based on more than 20 years of experience with cybersecurity technology and startups, this presentation will provide an understanding of the dynamics of the various markets that make up cybersecurity, as well as provide predictions of merging demand areas.
John Pescatore is SANS Director of Emerging Security Trends. He joined SANS in January 2013 after 14 years as Gartner’s lead security analyst. Before coming to Gartner he lead consulting groups at two early Internet security IPOs (Trusted Information Systems and Entrust) and spent 11 years in telecoms and computer security at GTE. He began his career at NSA and the US Secret Service. Follow him as @john_pescatore on Twitter or via his Security Trend Line blog on the SANS website.
Send your RSVP for this event to Sorry, you need javascript to view this email address. at BWTech.
]]>
Understanding Cybersecurity Market Dynamics John Pescatore SANS Institute 1:00-3:00 Tuesday, 4 March 2014 Suite 130, bwtech@UMBC, 5520 Research Park Drive, UMBC There is no single...
http://www.csee.umbc.edu/2014/02/talk-pescatore-on-understanding-cybersecurity-market-dynamics-34/
https://my3.my.umbc.edu/api/v0/pixel/news/41326/guest@my.umbc.edu/bcbc685bf0554f345d580fe86f318eb9/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 13 Feb 2014 10:14:08 -0500
Thu, 13 Feb 2014 10:14:08 -0500
Paid Federal Internship Opportunities
Paid Fully Funded Summer Federal Internship Positions!!!
The Washington Center (TWC) has internships available during the summer 2014 semester via the Federal Diversity Internship Initiative - and these internships will go fast! Specifically, positions are available with the United States' Veterans Administration (VA), Federal Aviation Administration (FAA), Federal Deposit Insurance Corporation (FDIC), National Archives and Records Administration (NARA), Department of Health and Human Services (HHS) and U.S. Department of Treasury.
Students
with Business/Human Resources, Communication, Computer &
Information Technology, Engineering, Public Administration and
Healthcare-related backgrounds are needed. Internships through the Federal Diversity Internship Initiative are fully-funded and paid opportunities. In addition, some support is provided for travel and other expenses. There is no out-of-pocket cost for participation.
To be considered for this opportunity, applications must be received by March 3, 2014.
To
submit the application, you must include basic academic and personal
information, your resume and an essay. Letters of recommendation are
required, but can arrive after submission. An official transcript will
also be required and should be sent as soon as possible. Be sure to
choose option 2 (the Federal Diversity Internship Initiative) on the
application! To apply to the Federal Diversity Internship Initiative, click here.
If you have any questions about the opportunity to pursue a paid, federal internship,
please do not hesitate to contact us. The Washington Center is happy to
assist with the application in any way and we look forward to working
with you this year.
Reid May
Office of Admissions & Institutional Relations
The Washington Center for Internships and Academic Seminars
info@twc.edu
www.twc.edu/federal
202-238-7900 (main line)
Please Paw if you've read this so I know to keep posting things like this ! THANKS
]]>
The Washington Center (TWC) has internships available during the summer 2014 semester via the Federal Diversity Internship Initiative - and these internships will go fast! Specifically, positions...
http://www.twc.edu/internships/additional-programs/federal-diversity-internship-initiative
https://my3.my.umbc.edu/api/v0/pixel/news/41298/guest@my.umbc.edu/a69589841655ce98266f546f57992804/api/pixel
computer
diversity
federal
government
health
information
internship
issa
job
paid
science
technology
Information Systems Security Association, UMBC Chapter
https://my3.my.umbc.edu/groups/issa
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/xxlarge.jpg?1392234532
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/xlarge.jpg?1392234532
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/large.jpg?1392234532
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/medium.jpg?1392234532
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/small.jpg?1392234532
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/xsmall.jpg?1392234532
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/041/298/490d3a9dd72716b3101890d0d8241c51/xxsmall.jpg?1392234532
11
0
true
Wed, 12 Feb 2014 14:53:42 -0500
Wed, 12 Feb 2014 16:11:36 -0500
Apply to the UMBC Cyber Scholars Program by 14 February

Computer Engineering, Computer Science, and Information Systems majors with at least a 3.25 GPA and an interest in cybersecurity are encouraged to apply for 2014-15 cohort of the UMBC Cyber Scholars Program.
The Cyber Scholars Program is a merit-based scholarship program for talented undergraduates majoring in computer science, information systems of computer engineering who are interested in pursuing a career within the field of cybersecurity. Cyber Scholars are supported financially and incorporated into a scholarship community, unique courses, mentoring, and the chance to take part in cybersecurity research and internships during in their academic careers.
Apply by 14 February 2014 by submitting a application along with two letters of recommendation and an official college transcript.
]]>
Computer Engineering, Computer Science, and Information Systems majors with at least a 3.25 GPA and an interest in cybersecurity are encouraged to apply for 2014-15 cohort of the UMBC Cyber...
http://www.csee.umbc.edu/2014/01/apply-to-the-umbc-cyber-scholars-program-by-14-february/
https://my3.my.umbc.edu/api/v0/pixel/news/40883/guest@my.umbc.edu/28b80125fc6c27ecd4e711a2cd1089d4/api/pixel
cybersecurity
news
undergraduate
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Fri, 31 Jan 2014 23:07:07 -0500
Cyber Scholars Program Scholarships Available
Money and good resume material
Computer Engineering, Computer Science, and Information Systems majors
with at least a 3.25 GPA and an interest in cybersecurity (and who are
not already part of another scholar program, such as Meyerhoff, Sherman,
CWIT, etc.) are encouraged to apply to be a part of the next cohort of
the Cyber Scholars Program, starting in Fall 2014.
TheCyber Scholars Program is a merit-based scholarship program for
talented undergraduates majoring in computer science, information
systems, and computer engineering at UMBC who are interested in pursuing a career within the field of cybersecurity.
Cyber Scholars are supported financially and incorporated into a scholarship
community, unique courses,
mentoring, and the chance to take part in cybersecurity research and
internships during in their academic careers.
Deadline: February 14th, 2014
Cyber Scholar Applicants must submit the following materials:
Mail or drop off completed application to:
Attn: Cindy Greenwood
Center for Women in Technology (CWIT)
1000 Hilltop Circle, ITE 452
Baltimore, MD 21250
CSEE professor Tim Finin has been appointed as a co-editor of the Viewpoints section of the Communications of the ACM, the monthly magazine of the Association for Computing Machinery. ACM was founded in 1947 and is the world’s largest educational and scientific computing society with the mission of providing resources that advance computing as a science and a profession.
The Communications of the ACM was started in 1957 and is sent to all ACM members (currently over 100,000) and is considered “the leading print and online publication for the computing and information technology fields”. CACM’s Viewpoints section is publishes short articles expressing opinions and views that pertain to issues of broad interest to the computing community, covering a wide range of topics, including scientific, technical, educational and social. Each month a handful of articles are published from those contributed by a set of distinguished ACM columnists and submitted by ACM members and computing professionals.
]]>
CSEE professor Tim Finin has been appointed as a co-editor of the Viewpoints section of the Communications of the ACM, the monthly magazine of the Association for Computing Machinery. ACM was...
http://www.csee.umbc.edu/2014/01/tim-finin-appointed-co-editor-of-cacm-viewpoints/
https://my3.my.umbc.edu/api/v0/pixel/news/40412/guest@my.umbc.edu/f8899a07c79406155490499376970ca7/api/pixel
faculty-and-staff
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Mon, 20 Jan 2014 09:23:19 -0500
CSEE PhD student presents research at 2014 Quantum Information Processing Conference
CSEE Ph.D. student Omar Shehab received a travel grant to present his research, UNKNOTTING as a k-local Hamiltonian problem, at the 2014 Quantum Information Processing conference, which will be held early in February in Barcelona, Spain. Later in February he will also attend the Workshop on Quantum Games and Protocols at the Simons Institute for the Theory of Computing, UC Berkeley.
Omar’s research include adiabatic quantum Hamiltonian complexity, quantum computational simulation of topology and use of quantum optics to understand device independent cryptography. His work on quantum computing is done in collaboration with his mentor, CSEE Professor Samuel Lomonaco.
]]>
CSEE Ph.D. student Omar Shehab received a travel grant to present his research, UNKNOTTING as a k-local Hamiltonian problem, at the 2014 Quantum Information Processing conference, which will be...
http://www.csee.umbc.edu/2014/01/csee-student-presents-quantum-computing-research-at-quantum-information-processing-conference/
https://my3.my.umbc.edu/api/v0/pixel/news/40196/guest@my.umbc.edu/f0fa5f5857eb27c46cd0b0871eb55223/api/pixel
computer-science
graduate
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
1
true
Mon, 13 Jan 2014 23:09:57 -0500
UMBC project to study what influences home energy use
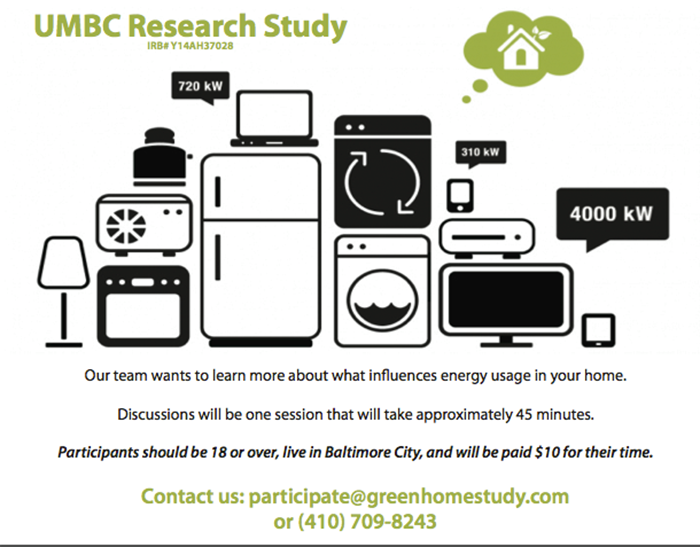
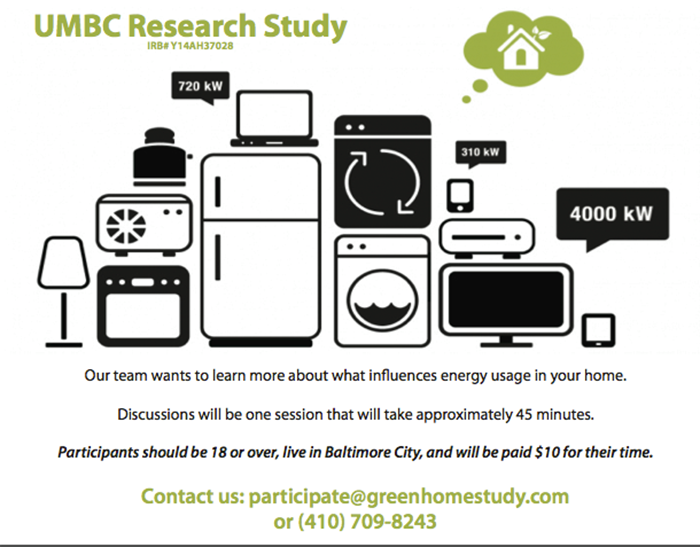
UMBC’s Mobile Pervasive and Sensor Systems Laboratory is looking for subjects who live in Baltimore City to interview for a study about what influences their energy use at home. The study is part of an NSF-sponsored Green Home Study project that aims to make it easier for off-grid and grid-tied home residents to make smart choices about managing energy.
]]>
UMBC’s Mobile Pervasive and Sensor Systems Laboratory is looking for subjects who live in Baltimore City to interview for a study about what influences their energy use at home. The study is part...
http://www.csee.umbc.edu/2014/01/umbc-project-to-study-what-influences-home-energy-use/
https://my3.my.umbc.edu/api/v0/pixel/news/40188/guest@my.umbc.edu/b6606b3255ca7aeffa95d4e54477267d/api/pixel
computer-engineering
computer-science
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Mon, 13 Jan 2014 17:21:06 -0500
PhD Defense: Chris Morris, Multi-Modal Saliency Fusion for Illustrative Image Enhancement

Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Ph.D. Dissertation Defense
Multi-Modal Saliency Fusion for Illustrative Image Enhancement
Christopher J. Morris
10:30-12:30, Wednesday, 15 January 2013, ITE 365 & 352
Digitally manipulated or augmented images are increasingly prevalent. Multisensor systems produce augmented images that integrate data into a single context. Mixed-reality images are generated from insertion of computer generated objects into a natural scene. Digital processing for application-specific tasks (e.g., compression or network transmission) can create images distorted with processing artifacts. Digital image augmentation can lead to the inclusion of artifacts that influence the perception of the image.
Visual cues (e.g., depth or size cues) may no longer be perceptually consistent in an augmented image. A feature deemed important in its local context may no longer be in the broader integrated context. Inserted synthetic objects may not possess the appropriate visual cues for proper perception of the overall scene. Finer cues that distinguish critical features may be lost in compressed images. Enhancing augmented images to add or restore visual cues can improve the image’s perceptibility.
This dissertation presents a framework for illustrating images to enhance critical features. The enhancements improve the perception and comprehension of the augmented image. The framework uses a linear combination of image (2D), surface topology (3D), and task based saliency measures to identify the critical features in the image. The use of multi-modal saliency allows the visualization designer to adjust the definition of critical features based on the attributes of the scene and the task at hand. Upon identification, the features are enhanced using a non-photorealistic rendering (NPR) deferred illustration technique. The enhancements, inspired by an analysis of artists’ techniques, bolster the features’ perceptual cues.
To measure the amount of similar salient features between the enhanced image and the original image, the framework describes the Saliency Similarity Metric (SSM). The SSM is feedback with which to make informed decisions to tune the visualization. The benefits of illustrative enhancement are analyzed using objective and subjective evaluations. Using conventional metrics, illustrative enhancements improve the perceptual image quality of images distorted by noise or compression artifacts. User survey results reveal that enhancements must be carefully applied for perceptual improvement. The framework can be effectively utilized in mobile rendering, augmented reality, and sensor fusion applications.
Committee: Drs. Penny Rheingans (chair), Dan Bailey, Jian Chen, Thomas Jackman (Desert Research Institute), Anupam Joshi and Marc Olano
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Ph.D. Dissertation Defense Multi-Modal Saliency Fusion for Illustrative Image Enhancement Christopher J....
http://www.csee.umbc.edu/2014/01/phd-defense-chris-morris-multi-modal-saliency-fusion-for-illustrative-image-enhancement/
https://my3.my.umbc.edu/api/v0/pixel/news/40146/guest@my.umbc.edu/fae9b302bf932ef4b473dd8885a4dd8f/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Sat, 11 Jan 2014 10:46:33 -0500
Sat, 11 Jan 2014 10:46:33 -0500
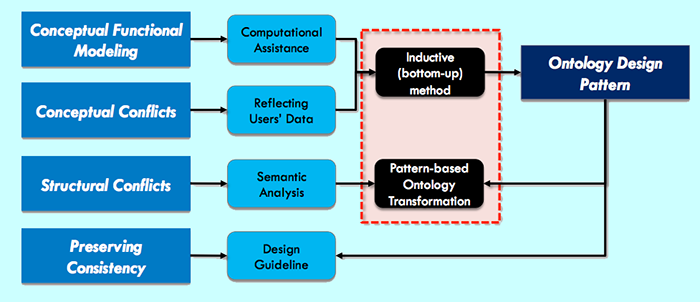
PhD proposal: Yunsu Lee, Functional Reference Ontology Development
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Ph.D. Dissertation Proposal
Functional Reference Ontology Development: a Design Pattern Approach
Yunsu Lee
1:00pm Friday, January 10, 2014, ITE325b, UMBC
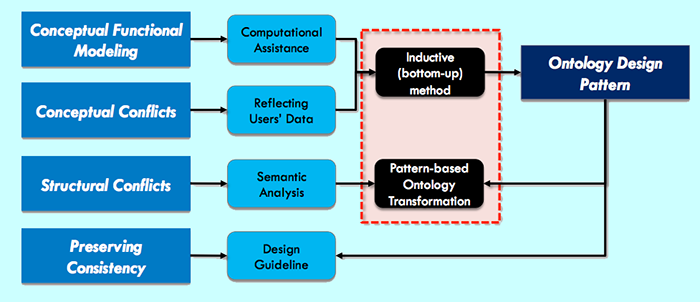
The next generation of smart manufacturing systems will be developed by composing advanced manufacturing components and IT services introducing new technologies. These new technologies can lead to dramatic improvements in the ability to monitor, control, and optimize all aspects of manufacturing. The ability to compose advanced manufacturing components and IT services enhances agility, resiliency, and productivity of a manufacturing system. In order to make the composition possible, functional knowledge of manufacturing components and IT services should be captured and shared explicitly. Recent researches have shown that a semantically precise and rich reference functional ontology enables effective composition. However, since domains of factories and production networks are large, evolving, and heterogeneous, developing a reference functional ontology is a challenging task. Specifically, conceptual functionality modeling that characterizes various features of manufacturing components and IT services at different levels of abstraction is a difficult task. Even if the reference functional ontology is developed successfully, there will certainly be interoperability issues between the reference functional ontology and local proprietary information models. Firstly, the conceptual conflict issues may arise primarily from the fact that the reference functional ontology does not reflect actual users’ or providers’ conceptualizations. Secondly, structural conflict issues may arise from diverse modeling choices in local, proprietary information models.
The objective of our research is to assess utility of design patterns in addressing the issues in the reference functional ontology development, specifically OWL ontology design patterns (ODPs). To achieve the objective, we will assess inductive approaches to identifying the ODPs, and explore development of a methodology for resolving structural differences between the reference functional ontology and local proprietary information models. The key potential contributions of this work include 1) new method to identify information patterns of functionalities in manufacturing components and IT services, 2) new inductive ODP development process which starts with the pattern definition of the specific functionality concepts, with subsequent grouping of these patterns into more general patterns, and 3) ODP-based ontology transformation to resolve structural conflicts between the reference functional ontology and local proprietary information models.
Committee: Drs. Yun Peng (chair), Tim Finin, Yelena Yesha, Milton Halem, Nenad Ivezic (NIST) and Boonserm Kulvatunyou (NIST)
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Ph.D. Dissertation Proposal Functional Reference Ontology Development: a Design Pattern Approach Yunsu...
http://www.csee.umbc.edu/2014/01/phd-proposal-yunsu-lee-functional-reference-ontology-development-a-design-pattern-approach/
https://my3.my.umbc.edu/api/v0/pixel/news/40080/guest@my.umbc.edu/035a57fc175ae42a5d2e2a7392c4efc1/api/pixel
computer-science
defense
graduate
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 09 Jan 2014 17:12:00 -0500
NSA Best Scientific Cybersecurity Paper Competition

The National Security Agency is soliciting nominations for the 2013 Best Scientific Cybersecurity Paper Competition. The competition is for scientific papers published between October 1, 2012 and December 31, 2013 that show an outstanding contribution to cybersecurity science. The nomination deadline is March 31, 2014.
The competition was created to stimulate research toward the development of systems that are resilient to cyber attacks. Entries are judged on scientific merit, the strength and significance of the work reported, and the degree to which the papers exemplify how to perform and report scientific research in cybersecurity.
The three winning papers from the 2012 cometition can be viewed at the Cyber-Physical Systems website.
This year’s nominations will be reviewed by a panel of distinguished experts including Dr. Whitfield Diffie, Dr. Dan Geer (In-Q-Tel), Dr. John McLean (NRL), Professor Angela Sasse, (University College London), Prof. Fred Schneider (Cornell), Mr. Phillip Venables (Goldman Sachs), Prof. David Wagner (UC Berkeley), and Dr. Jeannette Wing (Microsoft Research).
The contest winner and honorable mentions will be announced on the NSA external web site and the winner will be invited to present the winning paper to an audience of cybersecurity experts. For more information on eligibility criteria, criteria for judging and nomination procedures, see the 2013 Best Scientific Cybersecurity Paper Competition site.
]]>
The National Security Agency is soliciting nominations for the 2013 Best Scientific Cybersecurity Paper Competition. The competition is for scientific papers published between October 1, 2012 and...
http://www.csee.umbc.edu/2014/01/nsa-best-scientific-cybersecurity-paper-competition/
https://my3.my.umbc.edu/api/v0/pixel/news/40038/guest@my.umbc.edu/0b9fb561c056640d79ac79c4fc346d02/api/pixel
cybersecurity
news
research
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
1
true
Wed, 08 Jan 2014 11:48:25 -0500