Introduction to Quantum Computing and D-Wave Systems, 10am Tue 7/30
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
An Introduction to Quantum Computing: D-Wave Systems
Robert (Bo) Ewald and Edward (Denny) Dahl
D-Wave Systems, Inc
10:00-12:00 Tuesday, July 30, 2013, ITE 325b
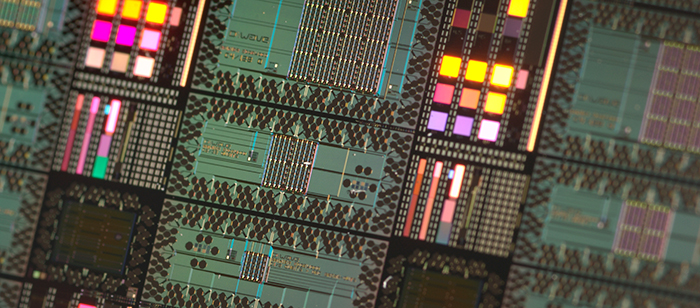
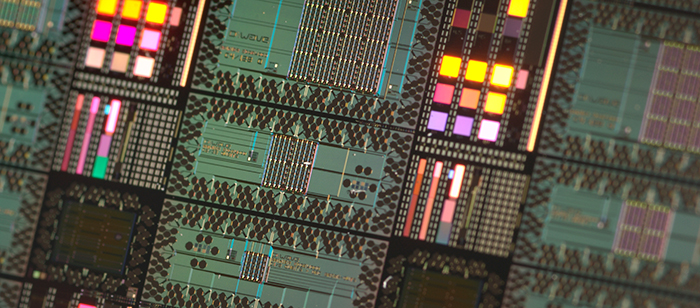
Bo Ewald and Denny Dahl from D-Wave Systems, Inc. will present an introduction to quantum computing and its role in their computing systems, complex machines constructed using state of the art ideas and approaches from many different fields of science and technology. While the quantum processor itself is the heart of the machine, the infrastructure that makes the processor go is also designed, built and tested extensively by D-Wave. In 2011, D-Wave System announced the D-Wave One, "the world's first commercially available quantum computer" which incorporated their 128 qubit chip-set using quantum annealing to solve optimization problems. This year a collaboration between NASA, Google and the Universities Space Research Association was announced that will create a Quantum Artificial Intelligence Lab at the NASA Ames Research Center that will use a 512 qubit D-Wave Two system to study how quantum computing might advance machine learning.
Bo Ewald has been Chief Revenue Officer and President of U.S. Business at D-Wave Systems Inc. since May 02, 2013. Mr. Ewald served as Chief Executive Officer of Graphics Properties Holdings, Inc., since April 9, 2007. Mr. Ewald has over 25 years experience in the high performance computing industry. He served as Chief Executive Officer of Silicon Graphics, Inc. from 2007 to 2009. He served as Chief Operating Officer and Executive Vice President of Scale8 Inc. He served as Chief Executive Officer of Linux Networx, Inc. until April 3, 2007 and oversaw its strategy & direction to drive continued growth. From 1984 to 1996, he held various management and executive positions at Cray Research, Inc., including President and Chief Operating Officer since December 1994. Before joining Cray Research Inc., he served as Head of the Computing and Communications Division of the Los Alamos National Laboratory and was responsible for providing computing and communications services to government customers nationwide from 1980 to 1984. Mr. Ewald is involved in various industry organizations and was appointed to the President's Information Technology Advisory Committee from 1997 to 2001. Mr. Ewald holds an M.S. Degree in Civil Engineering and Applied Mathematics from the University of Colorado and a BS Degree in Civil Engineering from the University of Nevada.
Dr. Denny Dahl received his PhD in physics from Stanford University in 1985 after completing a thesis on Quantum Monte Carlo computational techniques. He took a postdoctoral research position at Lawrence Livermore National Labs in the Parallel Processing Project and worked on simulation, analysis and applications of neural networks. Following this, Denny joined Thinking Machines Corporation and worked in their Technical Marketing Department. He obtained a patent for novel work in routing messages through the communication fabric of the CM-2, which was a massively parallel high performance computing platform. He also helped in providing technical support to a number of customers across a range of business verticals, including the petroleum and defense industries. Following Thinking Machines, Dr. Dahl participated in a range of start-up companies and developed expertise in high volume / high complexity RDBMS environments. He worked at a number of companies (eBay, Wells Fargo, JP Morgan Chase, Travelers Insurance, Western Asset Management, Williams Sonoma, Kroger, Walgreens, Teradata) providing architectural and development services related to batch and real-time data processing. Denny joined D-Wave Systems at the beginning of 2012, and has been involved in algorithm research, training, technical support for sales and communication functions within the company.
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County An Introduction to Quantum Computing: D-Wave Systems Robert (Bo) Ewald and Edward (Denny) Dahl D-Wave...
http://www.csee.umbc.edu/2013/07/introduction-to-quantum-computing-and-d-wave-systems-10am-tue-730/
https://my3.my.umbc.edu/api/v0/pixel/news/33241/guest@my.umbc.edu/8859a19590ffe405aade40610504ade7/api/pixel
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 27 Jul 2013 16:07:07 -0400
Sat, 27 Jul 2013 16:07:07 -0400
Ph.D. proposal: S. Rao, Accurate Estimation of Dynamic Power Supply Noise and its Effect on Path Delays, 7/29
Computer Science and Electrical Engineering
Ph.D. Dissertation Proposal
Framework for Accurate Estimation of Dynamic
Power Supply Noise and its Effect on Path Delays
Sushmita K. Rao
11:00am-1:00pm Monday, July 29, 2013, ITE 346
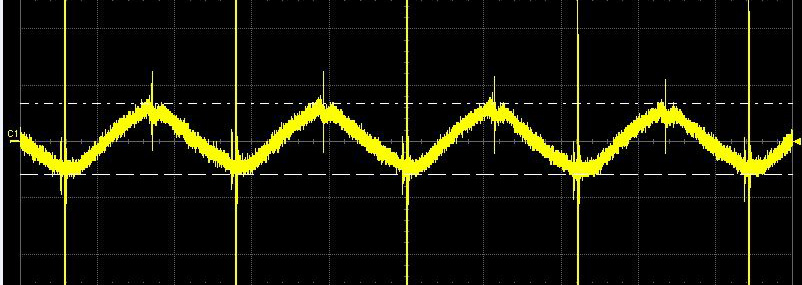
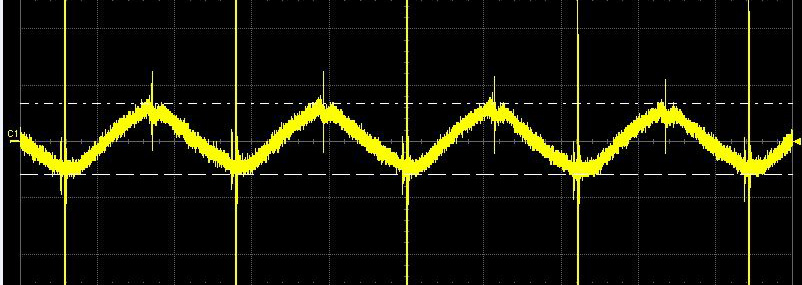
Power-supply noise is a major contributing factor for yield loss in sub-micron designs. Excessive switching in test mode causes supply voltage to droop more than in functional mode leading to failures in delay tests that would not occur otherwise under normal operation. Thus, there exists a need to accurately estimate on-chip supply noise early in the design phase to meet power requirements in normal mode and during test to prevent over-stimulation during test cycle and avoid false failures.
Simultaneous switching activity (SSA) of several logic components is one of the main sources of power-supply noise (PSN) which results in reduction of supply voltages at the power-supplies of the logic gates. Current research concentrate on static IR-drop which accounts for only part of the total voltage drop on the power grid and therefore insufficient for nanometer designs. To our knowledge, inductive drop is not included in current noise analysis techniques for simplification. The power delivery networks in today’s very deep-submicron chips are susceptible to slight variations and cause sudden large current spikes leading to higher Ldi/dt drop than resistive drop essentiating the need to be accounted. Simultaneous switching in localized areas in a chip too result in large instantaneous current to be drawn from a particular power bump or pad reducing supply voltage further. Thus, there arises a growing need to accurately characterize the resistive and inductive voltage drop caused by simultaneous switching of multiple paths. Power-supply noise also impacts circuit operation incurring a significant increase in path delays. It is critical to account for this increase in delay during the ATPG process else it can lead to overkill during transition and delay testing. However, it is infeasible to carry out full-chip SPICE-level simulations on a design to validate the large number of ATPG generated test patterns. Accurate and efficient techniques are required to quantify supply noise and its impact on path delays to ensure reliable operation in both mission mode and during test.
A scalable current-based dynamic method is presented to estimate both IR and Ldi/dt drop caused by simultaneous switching activity. Also presented is a technique to predict the increase in path delays caused by supply noise. The noise and delay estimation techniques use simulations of individual extracted paths in comparison to time-consuming full-chip simulations and thus it can be integrated with existing ATPG tools. Simulation results for combinational and sequential benchmark circuits are presented demonstrating the effectiveness of the convolution-based techniques.
Committee: Professors Chintan Patel (Chair), Mohamed Younis, Ryan Robucci and Nilanjan Banerjee
]]>
Computer Science and Electrical Engineering Ph.D. Dissertation Proposal Framework for Accurate Estimation of Dynamic Power Supply Noise and its Effect on Path Delays Sushmita K. Rao...
http://www.csee.umbc.edu/2013/07/ph-d-proposal-s-rao-accurate-estimation-of-dynamic-power-supply-noise-and-its-effect-on-path-delays-729/
https://my3.my.umbc.edu/api/v0/pixel/news/33240/guest@my.umbc.edu/78ba8dcc9382a603e519427394864d73/api/pixel
computer-engineering
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 27 Jul 2013 13:41:05 -0400
Sat, 27 Jul 2013 13:41:05 -0400
MS Defense: Sentiment Analysis on Tweets and their Relationship with Stock Market Trends, J. Sharma, 7/29

Computer Science and Electrical Engineering
MS Thesis Defense
Sentiment Analysis on Tweets and their
Relationship with Stock Market Trends
Jay Sharma
10:00 AM – 12:00 PM Monday, July 29, 2013, ITE 325
We investigate whether sentiment derived from micro-blogging site Twitter can be used to identify important events (product launch, quarter results etc.) and help to infer the future movement of the stock. We used the volume and key performance index of Apple Company’s financial tweets to identify important events and infer the future movement. We present the results of machine learning algorithms (Naïve Bayes, Maximum Entropy, and SVM) for classifying the sentiment of Apple Company’s financial tweets. Statistical analysis using Granger causality test showed that we were able to infer the movement of Apple Company’s stock close price in advance.
Committee: Professors Yelena Yesha (chair), Shujia Zhou, and Tim Finin
]]>
Computer Science and Electrical Engineering MS Thesis Defense Sentiment Analysis on Tweets and their Relationship with Stock Market Trends Jay Sharma 10:00 AM – 12:00 PM Monday, July 29,...
http://www.csee.umbc.edu/2013/07/ms-defense-sentiment-analysis-on-tweets-and-their-relationship-with-stock-market-trends-j-sharma-729/
https://my3.my.umbc.edu/api/v0/pixel/news/33179/guest@my.umbc.edu/9aa82ef1133879530375161ec33fc3e1/api/pixel
computer-science
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 25 Jul 2013 17:47:57 -0400
Thu, 25 Jul 2013 17:47:57 -0400
MS Defense: A. Korde, Radar Compressive Sensing for Noisy Signals, 7/24

MS Defense
Computer Science and Electrical Engineering
Detection Performance and Computational Complexity of
Radar Compressive Sensing for Noisy Signals
Asmita Korde
2:00-4:00 Wednesday, 24 July 2013, ITE 325
In recent years, compressive sensing has received a lot of attention due to its ability to reducethe sampling bandwidth, yet reproduce a good reconstructed signal back. Compressivesensing is a new theory of sampling which allows the reconstruction of a sparse signal bysampling at a much lower rate than the Nyquist rate. This concept can be applied to severalimaging and detection techniques. In this thesis, we explore the use of compressive sensing for radar applications. By using this technique in radar, the use of matched filter can be eliminated and high rate sampling can be replaced with low rate sampling. We analyze compressive sensing in the context of radar by applying varying factors such as noise and different measurement matrices. Different reconstruction algorithms are compared by generating ROC curves to determine their detection performance, which in turn are also compared against a traditional radar system. Computational complexity and MATLAB run time are also measured for the different algorithms. We also propose an algorithm called simplified OMP, which works well in noisy environments and has a very low computational complexity.
Committee: Professors Tinoosh Mohsenin (Chair), Joel Morris, Tulay Adali, and Mohamed Younis
]]>
MS Defense Computer Science and Electrical Engineering Detection Performance and Computational Complexity of Radar Compressive Sensing for Noisy Signals Asmita Korde 2:00-4:00 Wednesday,...
http://www.csee.umbc.edu/2013/07/ms-defense-a-korde-radar-compressive-sensing-for-noisy-signals-724/
https://my3.my.umbc.edu/api/v0/pixel/news/33133/guest@my.umbc.edu/4df12e1517a8df339ec5690886da46f3/api/pixel
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
1
true
Wed, 24 Jul 2013 22:22:02 -0400
Wed, 24 Jul 2013 22:22:02 -0400
MS defense: Multicast Routing with Byzantine Robustness, D. Mukherjee, 2:30 7/23

Computer Science and Electrical Engineering
MS Thesis Defense
Multicast Routing with Byzantine Robustness
Debdatta Mukherjee
2:30-4:30 Tuesday, july 23, 2013, ITE 346
Network problems arise when nodes behave in arbitrary ways such as sending malformed messages, sending incorrect messages or not forwarding messages at all to other nodes in the network. These faults are called Byzantine failures. In a real network, these faults can be a result of hardware failure, cyber-attacks or network congestion. Due to the serious problems these faults can cause, it becomes important to make the network robust against them, so that the network continues to operate properly or degrades in an acceptable way in the presence of such faults. In this thesis, we propose methods that include multiple node disjoint path calculations and robust flooding to find byzantine-free multicast trees. By finding such trees, we can guarantee the delivery of the messages from a source to a particular multicast group.
Committee: Professors Deepinder Sidhu (chair), Kostas Kalpakis and Sergei Nirenburg
]]>
Computer Science and Electrical Engineering MS Thesis Defense Multicast Routing with Byzantine Robustness Debdatta Mukherjee 2:30-4:30 Tuesday, july 23, 2013, ITE 346 Network problems...
http://www.csee.umbc.edu/2013/07/ms-defense-multicast-routing-with-byzantine-robustness-d-mukherjee-230-723/
https://my3.my.umbc.edu/api/v0/pixel/news/33006/guest@my.umbc.edu/249fbb6681dde4c55763636577e14154/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
5
0
true
Mon, 22 Jul 2013 12:43:10 -0400
Mon, 22 Jul 2013 12:43:10 -0400
MS defense: Social Media Data Analytics Applied to Hurricane Sandy, Han Dong, 7/29

MS Defense
Computer Science and Electrical Engineering
Social Media Data Analytics Applied to Hurricane Sandy
Han Dong
12:30-2:30 Monday, 29 July 2013, ITE 325b
Social media websites are an integral part of many people’s lives in delivering news and other emergency information. This is especially true during natural disasters. Furthermore, the role of social media websites is becoming more important due to the cost of recent natural disasters. These online platforms are usually the first to deliver emergency news to a wide variety of people due to the significantly large number of users registered. During disasters, extracting useful information from this pool of social media data can be useful in understanding the sentiment of the public; this information can then be used to improve decision making. In this work, I am presenting a system that automates the process of collecting and analyzing social media data from Twitter. I also explore a variety of visualizations that can be generated by the system in order to understand the public sentiment. I demonstrate an example of utilizing this system on the Hurricane Sandy disaster from October 26, 2012 to October 30, 2012. Finally, a statistical analysis is performed to explore the causality correlation between an approaching hurricane and the sentiment of the public.
As a result of the large amount of data collected by this system; scalable machine learning algorithms are needed for analysis. Boosting is a popular and powerful ensemble method in the area of supervised machine learning algorithms due to its theoretical convergence guarantees, simple implementation and ability to use different learning algorithms to produce a classifier with high accuracy. A novel parallel implementation of the multiclass version of Boosting (AdaBoost.MH) is proposed and our experimental results show that the parallel implementation achieves classification error percentages similar to serial implementation with fewer execution iterations. By distributing the tasks, the number of Boosting iterations decreased linearly at least up to 16 computational threads.
Committee: Professors Milton Halem (chair), Yelena Yesha, John Dorband and Shujia Zhou
]]>
MS Defense Computer Science and Electrical Engineering Social Media Data Analytics Applied to Hurricane Sandy Han Dong 12:30-2:30 Monday, 29 July 2013, ITE 325b Social media websites are...
http://www.csee.umbc.edu/2013/07/ms-defense-social-media-data-analytics-applied-to-hurricane-sandy-han-dong-11am-717/
https://my3.my.umbc.edu/api/v0/pixel/news/32882/guest@my.umbc.edu/be0a009f505ea7ffd8201ec33417e5f4/api/pixel
computer-science
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
1
true
Thu, 18 Jul 2013 11:27:50 -0400
Fri, 26 Jul 2013 09:27:50 -0400
MS defense: linked data for cybersecurity, Arnav Joshi, 9am 7/22

MS Defense
Computer Science and Electrical Engineering
Linked Data for Cybersecurity Vulnerability Descriptions
Arnav Joshi
9:00-11:00 Monday, 22 July 2013, 325b ITE
The Web is typically our first source of information about new software vulnerabilities, exploits and cyber-attacks. Information is found in semi-structured vulnerability databases as well as in text from security bulletins, news reports, cybersecurity blogs and Internet chat rooms. It can be useful to cybersecurity systems if there is a way to recognize and extract relevant information and represent it as easily shared and integrated semantic data. We describe such an automatic framework that generates and publishes a RDF linked data representation of cybersecurity concepts and vulnerability descriptions extracted from the National Vulnerability Database and other text sources. Entities, relations and concepts are represented using custom ontologies for the cybersecurity domain and also mapped to objects in the DBpedia knowledge base, producing a rich resource of machine-understandable linked data. The resulting cybersecurity linked data collection can be used for many purposes, including automating early vulnerability identification, mitigation and prevention efforts.
Committee: Professors Tim Finin (chair), Anupam Joshi and Tim Oates
]]>
MS Defense Computer Science and Electrical Engineering Linked Data for Cybersecurity Vulnerability Descriptions Arnav Joshi 9:00-11:00 Monday, 22 July 2013, 325b ITE The Web is typically...
http://www.csee.umbc.edu/2013/07/cybersecurity-linked-data/
https://my3.my.umbc.edu/api/v0/pixel/news/32730/guest@my.umbc.edu/8fe948ca6a037d75dbbdbeb86e336ac7/api/pixel
computer-science
cybersecurity
defense
graduate
news
research
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Wed, 17 Jul 2013 10:55:13 -0400
Wed, 17 Jul 2013 10:55:13 -0400
UMBC Prof. Helen Burgess recognized for first truly digital dissertation in U.S.
UMBC Professor Helen J. Burgess was recognized has for creating "the first truly digital dissertation in the United States" by the Networked Digital Library of Theses and Dissertations. Dr. Burgess is an Associate Professor of English in the Communication and Technology track and specializes in digital humanities.
Her 2003 doctoral dissertation, Highways of the mind: the haunting of the superhighway from the World's Fair to the World Wide Web, was completed at West Virginia University.
In addition to the recognition, Dr. Burgess received an Innovative ETD Award from NDLTD for her work.
“In Helen J. Burgess’ doctoral dissertation ‘Highways of the mind: the haunting of the superhighway from the World's Fair to the World Wide Web’ she produced the first truly digital dissertation in the United States which took full advantage of a Web-based format — incorporating an HTML and multimedia environment. Her dissertation consists of well-organized Web pages, persistence index links, photographs as well as video and audio clips linked throughout the document. This allows the reader to completely immerse into the digital environment and provide immediately accessible examples indicated in textual format. As a true testament to time and durability, Burgess’ ETD is still as functional today as the day it was posted online a decade ago. The bundle of dissertation files contain the Web page version as well as a "linear" book format version in PDF format, along with copies of all multimedia objects preserved in their original format, for preservation purposes.”
]]>
UMBC Professor Helen J. Burgess was recognized has for creating "the first truly digital dissertation in the United States" by the Networked Digital Library of Theses and Dissertations. Dr....
http://www.csee.umbc.edu/2013/07/umbc-prof-helen-burgess-recognized-for-first-truly-digital-dissertation-in-u-s/
https://my3.my.umbc.edu/api/v0/pixel/news/32354/guest@my.umbc.edu/a1a7130f42180aeb39973b40b1150852/api/pixel
humanities
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
31
8
true
Mon, 08 Jul 2013 22:03:14 -0400
Mon, 08 Jul 2013 22:03:14 -0400
UMBC & SAIC Announce 2013 Maryland Cyber Challenge
MCLEAN, Va., July 8, 2013 /PRNewswire/ – Science Applications International Corporation (SAIC) (NYSE: SAI), Maryland's Department of Business and Economic Development (DBED), and the University of Maryland, Baltimore County (UMBC) announced the third annual 2013 statewide cyber competition, the Maryland Cyber Challenge™, will be held October 8 through October 9 at the Baltimore Convention Center in Baltimore, Maryland. Registration is now open for aspiring cyber warriors from around the nation to compete at the Maryland event, located in the growing epicenter for the cybersecurity industry.
The Maryland Cyber Challenge™ is designed to attract more students and young professionals to pursue careers in cybersecurity and is held in conjunction with the CyberMaryland2013 Conference and Cyber Hall of Fame. It is the premier statewide cyber competition showcasing today's students and tomorrow's technologists with three levels of competition: high school, college and professional. Teams will have the opportunity to develop and improve their cybersecurity skills in a real-world environment. Founders of the event include SAIC, UMBC, DBED, the National Cyber Security Alliance (NCSA), and the Tech Council of Maryland (TCM).
Orientation sessions for teams in each of three divisions — high school, collegiate and industry and government professionals — will be held at UMBC in July and August. Two qualifying rounds will be conducted online using SAIC's Cyber Network Exercise System (CyberNEXS™), a scalable training, exercise and certification system that has successfully sharpened the cybersecurity skills of more than 15,000 students and professionals globally. CyberNEXS™ is expected to be a part of planned solutions company Leidos, Inc., following SAIC's planned separation into two independent, publicly traded companies, subject to board of directors approval, as announced Aug. 30, 2012.
The final rounds of the challenge will be held at the conference as part of Maryland's activities to recognize the 10th anniversary of National Cyber Security Awareness Month. High school teams will compete in a cyber-defense challenge, while collegiate and professional teams will go head-to-head in a "capture the flag" scenario. Winners of each division will be announced on October 9 during the CyberMaryland Conference.
The CyberMaryland Conference is a two day event designed to showcase industry innovations, create a platform for discussing cyber policy, recognize cyber pioneers and groom the next generation of IT experts. The goal of the event is to further demonstrate why Maryland is considered the nation's epicenter for information security excellence. In 2012, the Conference attracted over 800 cyber leaders and professionals from across the country. This included federal, state and local government agency leaders, educators, private industry CTOs, CISOs, analysts and technologists, cyber security entrepreneurs and investors. Conference registration will open in the coming weeks. For more information, go to https://www.fbcinc.com/e/cybermdconference/.
More details about the event will be announced in the coming weeks ahead.
Quick Facts:
- Started in 2011 as the Maryland Cyber Challenge and Conference
- Open to competitors nationwide
- Three divisions include high school, college and professional
- Team size: 3-6
- Powered by the SAIC CyberNEXS competition engine
- Technical focus: vulnerability mitigation, computer forensics, cyber defense and capture the flag
- Approximately 700 competitors across 115 teams in the past two years
- More than $160K in awards distributed over the past two years by the National Security Agency and SAIC
Key Dates:
- Orientation sessions and practice rounds will begin in July 2013
- Qualification Round 1 for all divisions is tentatively September 21, 2013
- Qualification Round 2 is tentatively September 26
- Cram sessions for final teams will be held the week of September 30, 2013
- Finals are in person October 8-9, 2013 at the Baltimore Convention Center
- Winners and awards will be announced at the completion of finals
Supporting Quotes:
State of Maryland
"In Maryland, we are committed to advancing cyber innovation and growing our Innovation Economy," said Governor O'Malley. "The Maryland Cyber Challenge showcases the work of our State's highly-skilled and talented students and professionals whose work helps to establish Maryland as the nation's epicenter for cybersecurity."
UMBC
"The Maryland Cyber Challenge enables us to support the robust cyber industry in our State and to excite young Marylanders about defending our nation's cyber systems," said Freeman A. Hrabowski. "We are delighted to again have strong partners in cultivating new talent and promoting this crucial industry."
SAIC
"The growing cybersecurity field is becoming a standard specialty within STEM education. Future cyber experts can become better skilled to help protect our nation's critical information infrastructure," said Lou Von Thaer, SAIC senior vice president and sector president. "By bringing together great minds to take on challenges, whether policy or technical, we contribute directly to protect national security, advance education and grow careers."
National Cyber Security Alliance
"As 21st Century innovation continues to be affected by cyber issues, careers in cybersecurity are more important than ever before," said Michael Kaiser, executive director of the National Cyber Security Alliance. "We're thrilled to see activities like the Maryland Cyber Challenge that develop and intrigue young minds to consider the profession and look forward to an inspiring event where we hope many participants walk-away with a strong desire to pursue the field."
Follow the Maryland Cyber Challenge:
LinkedIn: www.linkedin.com/pub/maryland-cyber-challenge-and-competition/33/207/a11
Facebook: https://www.facebook.com/MarylandCyberChallenge
YouTube:http://www.youtube.com/watch?v=K4kXNfa64xI
Twitter: @MarylandCyber
Website: www.marylandcyberchallenge.com
]]>
MCLEAN, Va., July 8, 2013 /PRNewswire/ – Science Applications International Corporation (SAIC) (NYSE: SAI), Maryland's Department of Business and Economic Development (DBED), and the University...
http://www.csee.umbc.edu/2013/07/2013-maryland-cyber-challenge-announced/
https://my3.my.umbc.edu/api/v0/pixel/news/32340/guest@my.umbc.edu/9ac601ab064a495fa00e57862f215cd8/api/pixel
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Mon, 08 Jul 2013 13:16:44 -0400
Mon, 08 Jul 2013 13:16:44 -0400
CYBR student places 3rd in Microsoft Cybersecurity Essay Contest
First-year Cybersecurity MPS student Andrew Shiffer placed third in Microsoft's "Cybersecurity 2020" student essay contest. The contest allows Microsoft to solicit original research about cybersecurity policy challenges from university students at any stage in their educational careers. Andrew's paper is entitled "A Cybersecurity Triumvirate: Policies, Outcomes, and Emerging Trends."
Andrew will receive $2,000 prize (which he is applying toward his studies at UMBC) and the opportunity for his work to be published by Microsoft at a later date. According to a follow-up note from Microsoft, it appears that Andrew is the only American finalist — the first and second place students both came from Canadian universities.
Well done, Andrew!
]]>
First-year Cybersecurity MPS student Andrew Shiffer placed third in Microsoft's "Cybersecurity 2020" student essay contest. The contest allows Microsoft to solicit original research about...
http://www.csee.umbc.edu/2013/07/14169/
https://my3.my.umbc.edu/api/v0/pixel/news/32089/guest@my.umbc.edu/0e7a0c1fa13c3802b89c45994ee64e22/api/pixel
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
10
0
true
Tue, 02 Jul 2013 07:45:23 -0400
Tue, 02 Jul 2013 07:45:23 -0400