Professor Elisa Bertino of Purdue University
Professor Elisa Bertino of Purdue UniversitySecurity and Privacy in the IoT
Professor Elisa Bertino
Purdue University
1:00-2:00 pm Friday, 20 November 2020
Participate via Webex
Phone +1-202-860-2110; code: 120 706 1902
The Internet of Things (IoT) paradigm refers to the network of physical objects or”things” embedded with electronics, software, sensors, and connectivity to enable objects to exchange data with servers, centralized systems, and/or other connected devices based on a variety of communication infrastructures. IoT makes it possible to sense and control objects creating opportunities for more direct integration between the physical world and computer-based systems. IoT will usher automation in a large number of application domains, ranging from manufacturing and energy management (e.g., Smart Grid), to healthcare management and urban life (e.g. Smart City). However, because of its fine-grained, continuous, and pervasive data acquisition and control capabilities, IoT raises concerns about security and privacy. Deploying existing security solutions to IoT is not straightforward because of device heterogeneity, highly dynamic and possibly unprotected environments, and large scale. In this talk, after outlining key challenges in IoT security and privacy, we present initial approaches to securing IoT data and then focus on our recent work on security analysis for cellular network protocols and edge-based anomaly detection.
Elisa Bertino is a professor of Computer Science at Purdue University. Prior to joining Purdue, she was a professor and department head at the Department of Computer Science and Communication of the University of Milan. She has been a visiting researcher at the IBM Research Laboratory (now Almaden) in San Jose, at the Microelectronics and Computer Technology Corporation, at Rutgers University, and at Telcordia Technologies. Her main research interests include security, privacy, database systems, distributed systems, and sensor networks. Her research focuses on digital identity management, biometrics, IoT security, security of 4G and 5G cellular network protocols, and policy infrastructures for managing distributed systems. Prof. Bertino has published more than 700 papers in all major refereed journals, and in proceedings of international conferences and symposia. She has given keynotes, tutorials, and invited presentations at conferences and other events. She is a Fellow member of ACM, IEEE, and AAAS. She received the 2002 IEEE Computer Society Technical Achievement Award “For outstanding contributions to database systems and database security and advanced data management systems”, the 2005 IEEE Computer Society Tsutomu Kanai Award for “Pioneering and innovative research contributions to secure distributed systems”, and the ACM 2019-2020 Athena Lecturer Award.
The post talk: Elisa Bertino on Security and Privacy in the IoT, 1-2 Fri 11/20 appeared first on Department of Computer Science and Electrical Engineering.
]]>
 Remotegrity was the first voter-verifiable Internet voting system used in 2011 for a public office election in Takoma Park, Maryland
Remotegrity was the first voter-verifiable Internet voting system used in 2011 for a public office election in Takoma Park, Maryland Alan Sherman, right, talking with Rick Forno on campus in 2018. Photo by Marlayna Demond ’11 for UMBC.
Alan Sherman, right, talking with Rick Forno on campus in 2018. Photo by Marlayna Demond ’11 for UMBC.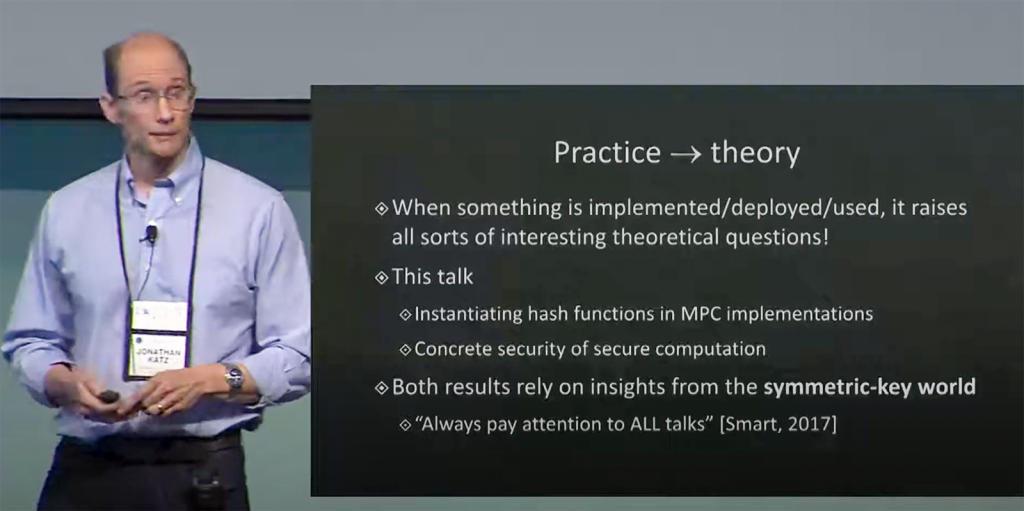

 Jack Suess. Photo by Marlayna Demond ’11 for UMBC.
Jack Suess. Photo by Marlayna Demond ’11 for UMBC.
 BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the protocol).
BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the protocol).