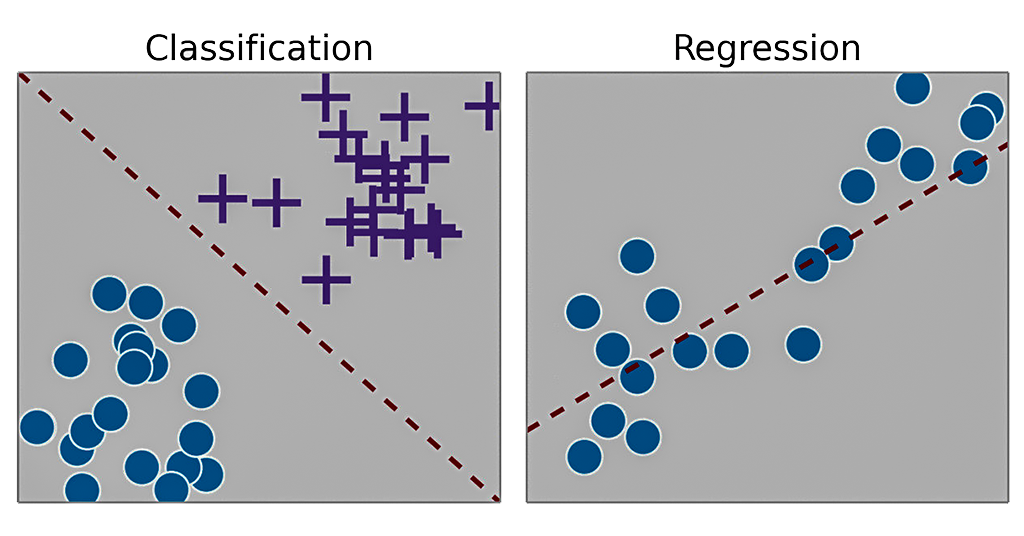
talk: Statistical Learning 101: Regression vs. Classification, 11:30 9/5
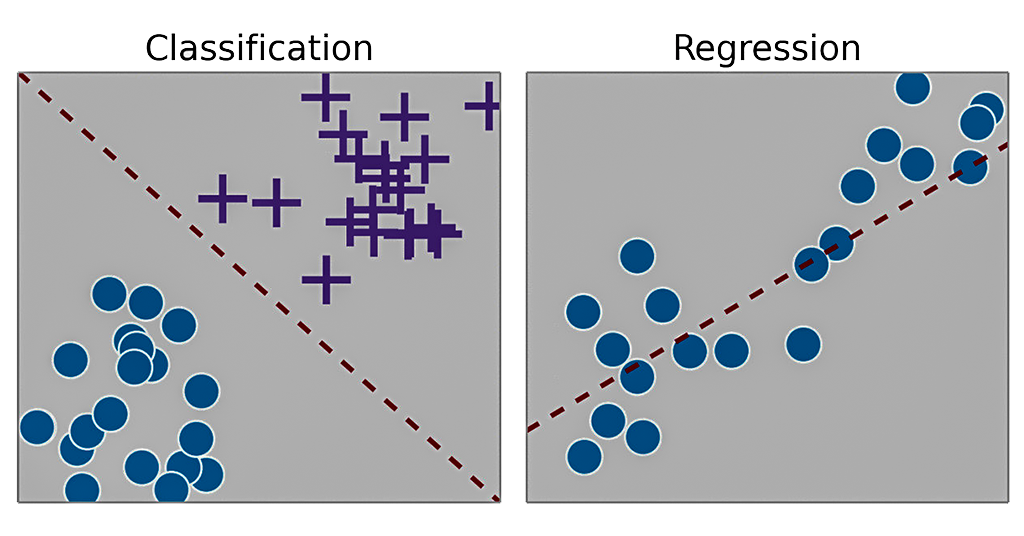
Statistical Learning 101: Regression vs. Classification
Dr. Ergun Simsek
Co-director, Computer Science and Information Technologies Department
Bahcesehir University, DC campus
11:30-12:30pm Wednesday, 5 September 2018, ITE 325b, UMBC
In the last decade, statistical learning, which is the concept of using algorithms to identify patterns and/or make predictions based on input data sets, has received increased interest due to its potential to answer diverse questions in various industries such as finance, business, and health. In this talk, I will introduce the two most fundamental methods of statistical learning that are applicable to both data and computer science: regression and classification. Real world examples will be provided to highlight the differences and similarities between these two methods and place them into appropriate contexts.
Dr. Ergun Simsek earned his PhD from Duke University in 2006. He is the co-director of the Computer Science and Information Technologies Department at the Bahcesehir University’s newly established DC campus (BAU DC). He joined Bahcesehir University’s Electrical and Electronics Engineering Department and later was promoted to associate professor. Upon moving back to the United States, he spent six years at the George Washington University’s Department of Electrical & Computer Engineering before returning to BAU at their DC campus. Dr. Simsek’s private sector experience includes working for Schlumberger Doll Research (SDR) Center’s Math and Modeling Department as a post-doctoral research associate, where he helped develop new numerical techniques for various oil and gas industry applications. He continues researching how to solve emerging engineering problems through efficient and robust computational techniques.
Host: Dr. Richard Forno (*protected email*)
The post talk: Statistical Learning 101: Regression vs. Classification, 11:30 9/5 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Statistical Learning 101: Regression vs. Classification Dr. Ergun Simsek Co-director, Computer Science and Information Technologies Department Bahcesehir University, DC campus...
https://www.csee.umbc.edu/2018/08/talk-statistical-learning-101-regression-vs-classification-1130-8-5/
https://my3.my.umbc.edu/api/v0/pixel/news/78245/guest@my.umbc.edu/72505561c961d3ebf149569aaf8f1e0a/api/pixel
ai
data-science
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 30 Aug 2018 10:39:50 -0400
CMSC 201 Computer Science I for Non-CS Disciplines
Special Section (Catalog #7838) for Fall 2018
Gain a competitive advantage in your field!
Programming and problem-solving skills are musts for today’s
college graduates!
Enroll in a special
section of CMSC 201 Computer Science I that emphasizes programming topics
applicable to the social and biological sciences and other majors. Sample topics include statistical analysis,
working with large data sets, and data visualization using the popular Python programming language. You will also receive
more individual attention in this smaller CMSC 201 section!
This section fulfills
any major’s requirement for CMSC 201 and is open to all non-CS, non-engineering majors.
No programming
experience is required. Click here
for more details about this unique opportunity.
]]>
Gain a competitive advantage in your field! Programming and problem-solving skills are musts for today’s college graduates! Enroll in a special section of CMSC 201 Computer Science I...
https://www.csee.umbc.edu/2018/04/cmsc-201-computer-science-non-cs-disciplines-fall-2018/
https://my3.my.umbc.edu/api/v0/pixel/news/78103/guest@my.umbc.edu/913fa3add82a32b2ac70d92e74cc44be/api/pixel
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/xxlarge.jpg?1535052016
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/xlarge.jpg?1535052016
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/large.jpg?1535052016
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/medium.jpg?1535052016
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/small.jpg?1535052016
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/xsmall.jpg?1535052016
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/078/103/14c3eb8771891efffb837717ea96a8c9/xxsmall.jpg?1535052016
0
0
false
Thu, 23 Aug 2018 15:21:31 -0400
talk: Methods and Models: Data Science for Campus Parking, 11:15am Mon 8/13

Methods and Models: Data Science for Campus Parking
Professor John Hoag
Associate Professor, Ohio University
11:15-12:15pm Monday, 13 August 2018 in ITE 325B
How can data science improve the parking experience for students, faculty, and staff? Or are there other motives at work? This talk will define and approach this perennial campus problem from perspectives of telematics and modeling, starting with the “Smart Cities” life cycle of data collection and analysis – from best practices through optimization. Next, we will consider relevant probabilistic models and their implementations over a century of study. We will conclude by discussing unintended consequences such as LPRs and other outcomes.
Dr. John Hoag is Associate Professor of Information and Telecommunication Systems at Ohio University in Athens, OH. He earned Ph.D. and M.S. Degrees in Operations Research from Ohio State University and holds a Bachelor’s degree in Computer Science. His current portfolio can be termed Smart Cities, which subsumes transportation, energy, finance, public health, and more, for which he is forming interdisciplinary public-private teams whose scope encompasses data collection, telemetry, storage, and analysis. The Smart Cities displaced work he started in bioinformatics and translational biomedical science, where his efforts focused on computational complexity and system performance. He maintains an adjunct appointment in EECS at Case Western Reserve University.
Host: Dr. Richard Forno (*protected email*)
The post talk: Methods and Models: Data Science for Campus Parking, 11:15am Mon 8/13 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Methods and Models: Data Science for Campus Parking Professor John Hoag Associate Professor, Ohio University 11:15-12:15pm Monday, 13 August 2018 in ITE 325B How can data science improve the...
https://www.csee.umbc.edu/2018/08/talk-methods-and-models-data-science-for-campus-parking-1115am-mon-8-13/
https://my3.my.umbc.edu/api/v0/pixel/news/77868/guest@my.umbc.edu/ee48da26e32074af2b2f4334a8b5e0b0/api/pixel
computer-science
data-science
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
true
Fri, 10 Aug 2018 15:46:24 -0400
CMSC 201: Computer Science I for Non-CS Disciplines – Fall 2018

CMSC 201 Computer Science I for Non-CS Disciplines – Fall 2018
This fall, Dr. Susan Mitchell will teach a special section of CMSC 201 Computer Science I designed for social and biological sciences *and other majors*. The course will cover the same content and have the same rigor as the regular sections of CMSC 201 and prepare students to continue on to CMSC 202 if they wish. As with other sections, it fulfills any major’s requirement for CMSC 201. The key difference will be that the assignments and projects will emphasize topics applicable to many non-CS disciplines, such as statistical analysis, working with large data sets, and data visualization. The catalog description is:
An introduction to computer science through problem solving and computer programming. Programming techniques covered by this course include modularity, abstraction, top-down design, specifications documentation, debugging and testing. The core material for this course includes control structures, functions, lists, strings, abstract data types, file I/O, and recursion.
The course will include a lecture from 2:30pm to 3:45pm on Mondays and Wednesdays (Section 36-LEC) and a one-hour lab on either Monday (Section 37-DIS) or Wednesday (Section 38-DIS) from 11:00-11:50am.
Permission from the instructor is required to register for this section. No prior programming experience is required. The only prerequisite is that students must have completed MATH 150, 151 or 152 with a C or better; OR have MATH test placement into MATH 151; OR be concurrently enrolled in MATH 155 or completed it with a C or better.
For permission or questions, email Dr. Susan Mitchell at *protected email*
The post CMSC 201: Computer Science I for Non-CS Disciplines – Fall 2018 appeared first on Department of Computer Science and Electrical Engineering.
]]>
CMSC 201 Computer Science I for Non-CS Disciplines – Fall 2018 This fall, Dr. Susan Mitchell will teach a special section of CMSC 201 Computer Science I designed for social and biological...
https://www.csee.umbc.edu/2018/08/cmsc-201-computer-science-i-for-non-cs-disciplines-fall-2018/
https://my3.my.umbc.edu/api/v0/pixel/news/77859/guest@my.umbc.edu/052d2b83f6b11aa3ac69f256351cd1fc/api/pixel
computer-science
education
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Fri, 10 Aug 2018 09:00:52 -0400
CMSC 201 Computer Science I for Non-CS Disciplines
Special Section (Catalog #7838) for Fall 2018
Gain a competitive advantage in your field!
Programming and problem-solving skills are musts for today’s
college graduates!
Enroll in a special
section of CMSC 201 Computer Science I that emphasizes programming topics
applicable to the social and biological sciences and other majors. Sample topics include statistical analysis,
working with large data sets, and data visualization using the popular Python programming language. You will also receive
more individual attention in this smaller CMSC 201 section!
This section fulfills
any major’s requirement for CMSC 201 and is open to all non-CS, non-engineering majors.
No programming
experience is required. Click here
for more details about this unique opportunity.
]]>
Gain a competitive advantage in your field! Programming and problem-solving skills are musts for today’s college graduates! Enroll in a special section of CMSC 201 Computer Science I...
https://www.csee.umbc.edu/2018/04/cmsc-201-computer-science-non-cs-disciplines-fall-2018/
https://my3.my.umbc.edu/api/v0/pixel/news/77831/guest@my.umbc.edu/15ace2dbcb1ed80af418f50974ee1d8f/api/pixel
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/xxlarge.jpg?1533760916
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/xlarge.jpg?1533760916
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/large.jpg?1533760916
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/medium.jpg?1533760916
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/small.jpg?1533760916
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/xsmall.jpg?1533760916
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/077/831/0505444168b5d9db738d31d2f66f5ab0/xxsmall.jpg?1533760916
5
0
false
Wed, 08 Aug 2018 16:43:25 -0400
Weaponized information seeks a new target in cyberspace: Users’ minds
 Cyberattacks target Americans’ thinking. Fancy Tapis/Shutterstock.com
Cyberattacks target Americans’ thinking. Fancy Tapis/Shutterstock.com
Weaponized information seeks a new target in cyberspace: Users’ minds
The Russian attacks on the 2016 U.S. presidential election and the country’s continuing election-related hacking have happened across all three dimensions of cyberspace – physical, informational and cognitive. The first two are well-known: For years, hackers have exploited hardware and software flaws to gain unauthorized access to computers and networks – and stolen information they’ve found. The third dimension, however, is a newer target – and a more concerning one.
This three-dimensional view of cyberspace comes from my late mentor, Professor Dan Kuehl of the National Defense University, who expressed concern about traditional hacking activities and what they meant for national security. But he also foresaw the potential – now clear to the public at large – that those tools could be used to target people’s perceptions and thought processes, too. That’s what the Russians allegedly did, according to federal indictments issued in February and July, laying out evidence that Russian civilians and military personnel used online tools to influence Americans’ political views – and, potentially, their votes. They may be setting up to do it again for the 2018 midterm elections.
Some observers suggest that using internet tools for espionage and as fuel for disinformation campaigns is a new form of “hybrid warfare.” Their idea is that the lines are blurring between the traditional kinetic warfare of bombs, missiles and guns, and the unconventional, stealthy warfare long practiced against foreigners’ “hearts and minds” by intelligence and special forces capabilities.
However, I believe this isn’t a new form of war at all: Rather, it is the same old strategies taking advantage of the latest available technologies. Just as online marketing companies use sponsored content and search engine manipulation to distribute biased information to the public, governments are using internet-based tools to pursue their agendas. In other words, they’re hacking a different kind of system through social engineering on a grand scale.
 Americans are used to seeing Russian propaganda that looks like this. AP Photo/Kirsty Wigglesworth
Americans are used to seeing Russian propaganda that looks like this. AP Photo/Kirsty Wigglesworth
Old goals, new techniques
More than 2,400 years ago, the Chinese military strategist and philosopher Sun Tzu made it an axiom of war that it’s best to “subdue the enemy without fighting.” Using information – or disinformation, or propaganda – as a weapon can be one way to destabilize a population and disable the target country. In 1984 a former KGB agent who defected to the West discussed this as a long-term process and more or less predicted what’s happening in the U.S. now.
The Russians created false social media accounts to simulate political activists – such as @TEN_GOP, which purported to be associated with the Tennessee Republican Party. Just that one account attracted more than 100,000 followers. The goal was to distribute propaganda, such as captioned photos, posters or short animated graphics, purposely designed to enrage and engage these accounts’ followers. Those people would then pass the information along through their own personal social networks.
Starting from seeds planted by Russian fakers, including some who claimed to be U.S. citizens, those ideas grew and flourished through amplification by real people. Unfortunately, whether originating from Russia or elsewhere, fake information and conspiracy theories can form the basis for discussion at major partisan media outlets.
As ideas with niche online beginnings moved into the traditional mass media landscape, they serve to keep controversies alive by sustaining divisive arguments on both sides. For instance, one Russian troll factory had its online personas host rallies both for and against each of the major candidates in the 2016 presidential election. Though the rallies never took place, the online buzz about them helped inflame divisions in society.
The trolls also set up Twitter accounts purportedly representing local news organizations – including defunct ones – to take advantage of Americans’ greater trust of local news sources than national ones. These accounts operated for several years – one for the Chicago Daily News, closed since 1978, was created in May 2014 and collected 20,000 followers – passing along legitimate local news stories, likely seeking to win followers’ trust ahead of future disinformation campaigns. Shut down before they could fulfill that end, these accounts cleverly aimed to exploit the fact that many Americans’ political views cloud their ability to separate fact from opinion in the news.
These sorts of activities are functions of traditional espionage: Foment discord and then sit back while the target population becomes distracted arguing among themselves.
Fighting digital disinformation is hard
Analyzing, let alone countering, this type of provocative behavior can be difficult. Russia isn’t alone, either: The U.S. tries to influence foreign audiences and global opinions, including through Voice of America online and radio services and intelligence services’ activities. And it’s not just governments that get involved. Companies, advocacy groups and others also can conduct disinformation campaigns.
Unfortunately, laws and regulations are ineffective remedies. Further, social media companies have been fairly slow to respond to this phenomenon. Twitter reportedly suspended more than 70 million fake accounts earlier this summer. That included nearly 50 social media accounts like the fake Chicago Daily News one.
Facebook, too, says it is working to reduce the spread of “fake news” on its platform. Yet both companies make their money from users’ activity on their sites – so they are conflicted, trying to stifle misleading content while also boosting users’ involvement.
Real defense happens in the brain
The best protection against threats to the cognitive dimension of cyberspace depends on users’ own actions and knowledge. Objectively educated, rational citizens should serve as the foundation of a strong democratic society. But that defense fails if people don’t have the skills – or worse, don’t use them – to think critically about what they’re seeing and examine claims of fact before accepting them as true.
American voters expect ongoing Russian interference in U.S. elections. In fact, it appears to have already begun. To help combat that influence, the U.S. Justice Department plans to alert the public when its investigations discover foreign espionage, hacking and disinformation relating to the upcoming 2018 midterm elections. And the National Security Agency has created a task force to counter Russian hacking of election systems and major political parties’ computer networks.
These efforts are a good start, but the real solution will begin when people start realizing they’re being subjected to this sort of cognitive attack and that it’s not all just a hoax.
Richard Forno, Senior Lecturer, Cybersecurity & Internet Researcher, University of Maryland, Baltimore County
This article was originally published on The Conversation. Read the original article.
The post Weaponized information seeks a new target in cyberspace: Users’ minds appeared first on Department of Computer Science and Electrical Engineering.
]]>
Cyberattacks target Americans’ thinking. Fancy Tapis/Shutterstock.com Weaponized information seeks a new target in cyberspace: Users’ minds Richard Forno, University of Maryland, Baltimore...
https://www.csee.umbc.edu/2018/07/weaponized-information-seeks-a-new-target-in-cyberspace-users-minds/
https://my3.my.umbc.edu/api/v0/pixel/news/77688/guest@my.umbc.edu/7d92d247c93e19804dabc704d5f4e317/api/pixel
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
1
true
Mon, 30 Jul 2018 08:47:53 -0400
UMBC’s Sherman receives $5.4m in funding for cybersecurity research and scholarships

UMBC receives $5.4m in funding for new cybersecurity projects
NSF and NSA Fund Three Cybersecurity Projects by Prof. Alan Sherman
Professor Alan Sherman and colleagues were recently awarded more than $5.4 million dollars in three new grants to support cybersecurity research and education at UMBC, including two from the National Science Foundation (NSF) and one from the National Security Agency (NSA). Dr. Sherman leads UMBC’s Center for Information Security and Assurance which was responsible for UMBC’s designation as a National Center of Academic Excellence in Cybersecurity Research and Education.

This summer, NSF funded Sherman’s second CyberCorps Scholarship for Service (SFS) grant (Richard Forno, CoPI) that will fund 34 cybersecurity scholars over five years and support research at UMBC and in the Cyber Defense Lab (CDL). The $5 million award supports scholarships for BS, MS, MPS, and PhD students to study cybersecurity through UMBC degree programs in computer science, computer engineering, cyber, or information systems. SFS scholars receive tuition, books, health benefits, professional expenses, and an annual stipend ($22,500 for undergraduates, $34,000 for graduate students). In return, each scholar must engage in a summer internship and work for government (federal, state, local, or tribal) for one year for each year of support. The program is highly competitive and many of the graduates now work for the NSA.
A novel aspect of UMBC’s SFS program is that it builds connections with two nearby community colleges—Montgomery College (MC) and Prince Georges Community College (PGCC). Each year, one student from each of these schools is selected for a scholarship. Upon graduation from community college, the student transfers to UMBC to complete their four-year degree. In doing so, UMBC taps into a significant pool of talent and increases the number of cybersecurity professionals who will enter government service. Each January, all SFS scholars from UMBC, MC, and PGCC engage in a one-week research study. Working collaboratively, they analyze a targeted aspect of the security of the UMBC computer system. The students enjoy the hands-on experience while helping to improve UMBC’s computer security. Students interested in applying for an SFS scholarship should consult the CISA SFS page and contact Professor Sherman. The next application deadline is November 15.
With $310,000 of support from NSF, Sherman and his CoPIs, Drs. Dhananjay Phatak and Linda Oliva, are developing educational Cybersecurity Assessment Tools (CATS) to measure student understanding of cybersecurity concepts. In particular, they are developing and validating two concept inventories: one for any first course in cybersecurity, and one for college graduates beginning a career in cybersecurity. These inventories will provide science-based criteria by which different approaches to cybersecurity education can be assessed (e.g., competition, gaming, hands-on exercises, and traditional classroom). This project is collaborative with the University of Illinois at Urbana-Champaign.
With $97,000 of support from NSA, Sherman is developing a virtual Protocol Analysis Lab that uses state-of-the-art tools to analyze cryptographic protocols for structural weaknesses. Protocols are the structured communications that take place when computers interact with each other, as for example happens when a browser visits a web page. Experience has shown that protocols are so complicated to analyze that there is tremendous value in studying them using formal methods. Sherman and his graduate students are making it easier to use existing tools including CPSA, Maude NPA, and Tamerin, applying them to analyze particular protocols, and developing associated educational materials.
The post UMBC’s Sherman receives $5.4m in funding for cybersecurity research and scholarships appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC receives $5.4m in funding for new cybersecurity projects NSF and NSA Fund Three Cybersecurity Projects by Prof. Alan Sherman Professor Alan Sherman and colleagues were recently awarded...
https://www.csee.umbc.edu/2018/07/nsf-and-nsa-fund-three-cybersecurity-projects-by-prof-alan-sherman/
https://my3.my.umbc.edu/api/v0/pixel/news/77650/guest@my.umbc.edu/b291f995e8ceb362547ad3489392aee6/api/pixel
computer-science
cybersecurity
news
research
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
5
1
true
Wed, 25 Jul 2018 22:15:49 -0400
talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346
Robot Governance – Institutions and Issues
Dr. Aaron Mannes, ISHPI Information Technologies
10:30-11:30 Tuesday, 24 July 2018, ITE 346
Inexpensive sensors and information storage and processing have enabled the large-scale production of robots: autonomous systems capable of acting on the world. These systems represent an enormous technological and economic opportunity that will change society in countless and unpredictable ways. They will also bring new policy challenges. This presentation examines the missions the government will need to undertake to address the challenges raised by this new technology, identifies critical gaps the government faces in carrying out these missions, and discusses institutional options to address these gaps.
Dr. Aaron Mannes is the Senior Policy Advisor at ISHPI Information Technologies, where he supports the Apex Data Analytics Engine (DA-E) at the Department of Homeland Security Science and Technology Directorate. In supporting DA-E, Dr. Mannes collaborates on big data projects that support the Homeland Security Enterprise and researches technology policy. He started at DHS as an American Association for the Advancement of Science Policy Fellow in September 2015. From 2004 to 2015, Dr. Mannes was a researcher at the University of Maryland Institute for Advanced Computer Studies (UMIACS) where he was the subject matter expert on terrorism and international affairs collaborating with a team of inter-disciplinary scientists to build computational tools to support decision-makers facing 21st century security and development problems. Dr. Mannes earned his Ph.D. at the University of Maryland’s School of Public Policy in 2014. His dissertation topic was the evolving national security role of the vice president.
Dr. Mannes is the author or co-author of four books on terrorism and has written scores of articles, papers, and book chapters on an array of topics including Middle East affairs, terrorism, technology, and other international security issues for popular and scholarly publications including Politico, Policy Review, The Wall Street Journal, Foreign Policy, The Journal of International Security Affairs, The Huffington Post, The National Interest, The Jerusalem Post, and The Guardian.
This research was conducted with the support of the Apex Data Analytics Engine in the Department of Homeland Security (DHS) Science and Technology Directorate (S&T). In no way should anything stated in this seminar be construed as representing the official position of DHS S&T or any other component of DHS. Opinions and findings expressed in this seminar, as well as any errors and omissions, are the responsibility of the presenter alone.
The post talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Robot Governance – Institutions and Issues Dr. Aaron Mannes, ISHPI Information Technologies 10:30-11:30 Tuesday, 24 July 2018, ITE 346 Inexpensive sensors and information storage...
https://www.csee.umbc.edu/2018/07/talk-robot-governance-institutions-and-issues-1030-tue-7-24-itr346/
https://my3.my.umbc.edu/api/v0/pixel/news/77605/guest@my.umbc.edu/1729d29bc363b882d0ac2732137fc2f9/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 23 Jul 2018 17:27:32 -0400
SANS Diversity Training Program/Scholarship in Cybersecurity
Applications Due July 3rd!
Hey ISSA members,
If you are interested in cybersecurity, be sure to check out the SANS Diversity Cyber Academy (DCA). Apply to this program to get GIAC certifications in the Information Security field, candidates will also participate in advanced technical training and be taught hands-on cyber defense and incident handing skills.
LINK below:
Good Luck!
~Your ISSA board
]]>
Hey ISSA members, If you are interested in cybersecurity, be sure to check out the SANS Diversity Cyber Academy (DCA). Apply to this program to get GIAC certifications in the Information...
https://my3.my.umbc.edu/api/v0/pixel/news/77302/guest@my.umbc.edu/8059dc73cfc1ec0236830e768c2dcef3/api/pixel
Information Systems Security Association, UMBC Chapter
https://my3.my.umbc.edu/groups/issa
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
1
0
true
Tue, 26 Jun 2018 22:27:32 -0400
Tue, 26 Jun 2018 22:28:13 -0400
Scholarship Opportunity
Apply for a scholarship for IS students here!
Hello, everyone! We hope you are all enjoying your summer break so far.
We have received information regarding a wonderful scholarship opportunity for rising freshman, sophomores, and juniors.
Good luck!
-Your ISSA executive board
]]>
Hello, everyone! We hope you are all enjoying your summer break so far. We have received information regarding a wonderful scholarship opportunity for rising freshman, sophomores, and juniors....
https://apply.freshprints.com/scholarship6/?source=club
https://my3.my.umbc.edu/api/v0/pixel/news/77230/guest@my.umbc.edu/7c93cad445643367aa9b72093c655138/api/pixel
Information Systems Security Association, UMBC Chapter
https://my3.my.umbc.edu/groups/issa
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
2
0
true
Tue, 19 Jun 2018 17:44:20 -0400
Fri, 22 Jun 2018 21:41:40 -0400


 Cyberattacks target Americans’ thinking.
Cyberattacks target Americans’ thinking.