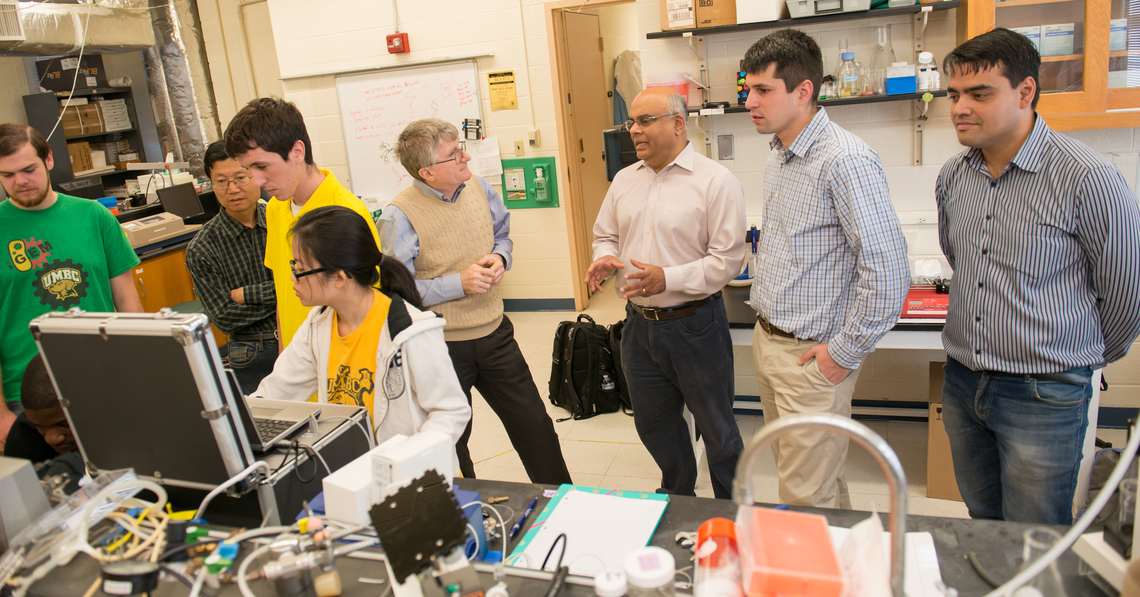
talk: Biomedical Engineering Projects at UMBC’s Center for Advanced Sensor Technology
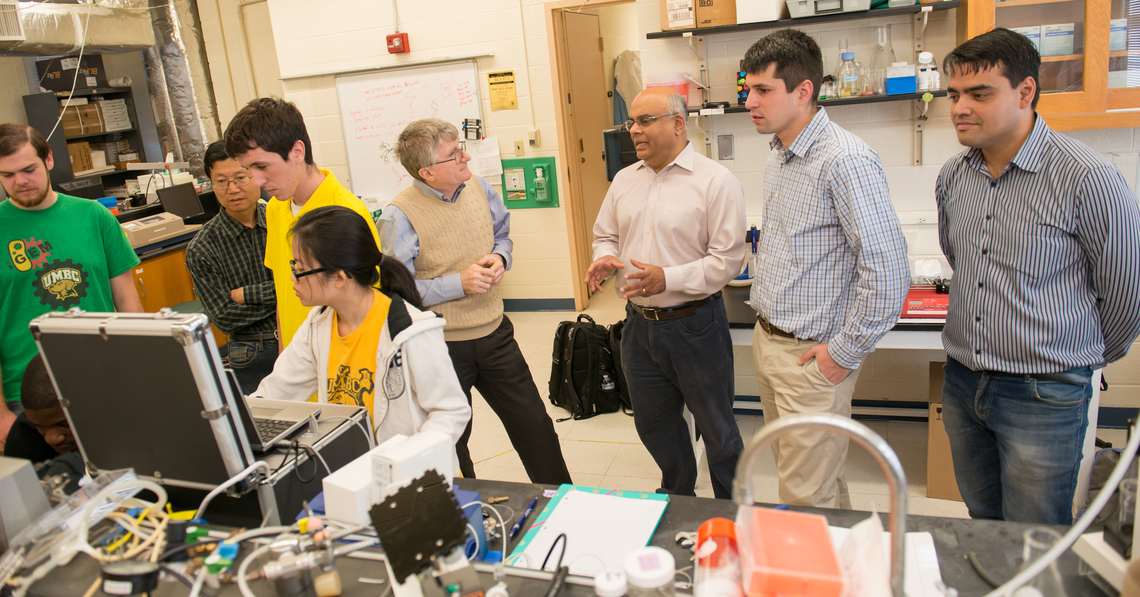
UMBC CSEE Research Seminar
Biomedical Engineering Projects at CAST
Dr. Yordan Kostov
UMBC Center for Advanced Sensing Technology
1-2pm, Friday, 9 December 2016, ITE 229
The Center for Advanced Sensor Technology is currently leading two projects: “Biologics manufacturing on demand,” funded by DARPA, and “A wearable asthma trigger monitoring system with integrated physiological monitor,” funded by NIH. The first project is focused on shrinking the footprint of a pharmaceutical factory down to suitcase, capable of producing biologics within twelve hours from the start. There is an ample need for drastically rethinking every detail of the process, with the need to miniaturize all the fluidic components (tanks, mixers, purification columns) and to create networked versions of the shakers, pumps, valves and sensors. The presentation highlights the need for novel sensing devices for process control and drug release. The second project is focused on development of three separate sensors for measuring CO2 in blood, concentration of dust particulate in air, and respiration rate. These sensors must be networked together to collect real time data and transfer them to a central depository via a cell phone app. The presentation highlights the different challenges in creating the sensors.
Dr. Yordan Kostov holds the B.Sc. and M.Sc. in Electrical Engineering, from Odessa Politechnic Institute, Ukraine. He received a Ph.D. Degree in Electrical/Chemical Engineering from Bulgarian Academy of Sciences for his work in the area of optical chemical sensors and biosensors. His post-doctoral training includes fellowships at University of Hannover, Germany and University of Maryland Biotechnology Institute. He was an assistant professor in the Department of Biotechincs, Sofia Technical University, Bulgaria. Since 2000, he is a research professor in the Department of Chemical and Biochemical Engineering, University of Maryland, Baltimore County (UMBC), with an appointment as assistant director of the UMBC Center for Advanced Sensor Technology. He is an affiliate professor in CSEE. Dr. Kostov is involved in the development of chemical and biochemical sensors for biotechnology and biomedical applications.
Organizers: Tulay Adali (*protected email*) and Alan T. Sherman (*protected email*)
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks.
Other UMBC CSEE Seminar Series: The UMBC Cyber Defense Lab (CDL) meets biweekly Fridays 11:15am-12:30pm in ITE 229, for research talks about cybersecurity.
The post talk: Biomedical Engineering Projects at UMBC’s Center for Advanced Sensor Technology appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC CSEE Research Seminar Biomedical Engineering Projects at CAST Dr. Yordan Kostov UMBC Center for Advanced Sensing Technology 1-2pm, Friday, 9 December 2016, ITE 229 The Center for...
https://www.csee.umbc.edu/2016/12/biomedical-engineering-projects-umbc-cast/
https://my3.my.umbc.edu/api/v0/pixel/news/64598/guest@my.umbc.edu/8828a07043ea67cf8a78a34039c2d4d7/api/pixel
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 01 Dec 2016 23:13:30 -0500
Event: Wanted, One Million IT Security Specialists by 2018

Students, faculty, staff and community members are invited to join CWIT and STEMRules for a lunch event to hear from and network with diverse professionals from across the cybersecurity industry.
Wanted: One Million IT Security Specialists by 2018
You Could be One of Them
12-1:30pm Friday, 2 December 2016
Albin O. Kuhn Library Gallery (1st floor)
Lunch will be provided
RSVP: Please respond by December 1, 2016
UMBC CWIT and STEMRules host cyber professionals from the public, private, and nonprofit sectors who will relate their personal/professional journeys, answer questions and be available for networking. Speakers will include the following individuals:
- Veda Woods is an executive at an undisclosed Fortune 500 financial institution, a member of multiple boards and the executive director of the International Consortium of Minority Cybersecurity Professionals.
- William McBorrough is a second-generation engineer is the founder and Managing Director of Washington, DC-based McGlobalTech and an information security and risk management consultant.
- Pamela E. Carbajal is a Cyber Security Compliance and Policy Analyst, Senior Consultant, at Booz Allen Hamilton, a global management and technology consulting and engineering services firm.
- Mahalakshmi “Maha” Venkataraman is a Senior Manager in the Software Engineering unit, and the technology lead for the anti-money laundering investigation team at Capital One, a major bank holding company.
- Lisa Jiggetts is the founder of the Women’s Society of Cyberjutsu, a nonprofit dedicated to empowering women to succeed in the cybersecurity field. She is a also a freelance mobile security consultant.





The post Event: Wanted, One Million IT Security Specialists by 2018 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Students, faculty, staff and community members are invited to join CWIT and STEMRules for a lunch event to hear from and network with diverse professionals from across the cybersecurity industry....
https://www.csee.umbc.edu/2016/12/event-wanted-one-million-security-specialists-2018/
https://my3.my.umbc.edu/api/v0/pixel/news/64599/guest@my.umbc.edu/5a63c156cfe59a27c1cae240b007cf07/api/pixel
computer-engineering
computer-science
cwit
cybersecurity
data-science
electrical-engineering
jobs
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 01 Dec 2016 09:16:52 -0500
talk: Genetic ancestry predicts striatal dopamine D2 receptors, 1pm Dec 2, ITE229
UMBC CSEE Seminar Series
Genetic ancestry predicts striatal dopamine D2 receptors
Dr. Corinde Wiers
National Institute on Alcohol Abuse and Alcoholism, Bethesda, MD
1-2pm Friday, 2 December 2016, ITE 229, UMBC
Genetic ancestry was recently found to be associated with cortical geometry, cortical surface, and total brain volume in humans. Despite ethnic differences in allele frequency in dopaminergic genes associated with dopamine D2/D3 receptor availability (D2R), no study to date has investigated the relationship between genetic ancestry and striatal D2R. Here, we show that genetic informative markers significantly predict dorsal striatal D2R in 117 healthy ethnically diverse residents of the New York metropolitan area using Positron Emission Tomography (PET) with [11C]raclopride, while correcting for age, sex, BMI, education years, and estimated socioeconomic status based on individuals’ ZIP codes. Striatal D2R may thus be modulated by genetic ancestry, although differences in environmental factors between ethnic groups could mediate these effects. Findings may have implications for pharmacological treatment targeting D2R, such as antipsychotic D2R antagonists.
Corinde Wiers, PhD, is a Research Fellow at the National Institute on Alcohol Abuse and Alcoholism, in the Laboratory of Neuroimaging of Nora D. Volkow, M.D. After her studies in Psychology and Psychobiology at the University of Amsterdam (Netherlands) and Sussex University (UK) in 2010, she completed her PhD in Psychology at the Berlin School of Mind and Brain and Free University Berlin (Germany) in 2014, where she investigated neural underpinnings of automatic approach behavior to alcohol cues, and neural effects of behavioral trainings in patients with alcohol use disorder. The main goal of Dr. Wiers’ research is to understand cognitive, neurobiological and (epi)genetic processes involved in drug addiction, using functional MRI, PET, psychophysics and molecular techniques. She currently works on how peripheral epigenetic markers relate to brain functioning in drug addiction and other psychiatric disorders. Further research interests include the neurobiology of sleep, effects of sleep deprivation, comorbidities of sleep and substance use disorders, and how neuroimaging techniques can be of use for treatment in psychiatry.
Host: Tulay Adali
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks.
Organizers: Tulay Adali and Alan Sherman
The post talk: Genetic ancestry predicts striatal dopamine D2 receptors, 1pm Dec 2, ITE229 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC CSEE Seminar Series Genetic ancestry predicts striatal dopamine D2 receptors Dr. Corinde Wiers National Institute on Alcohol Abuse and Alcoholism, Bethesda, MD 1-2pm Friday, 2 December...
https://www.csee.umbc.edu/2016/11/genetic-ancestry-predicts-striatal-dopamine-d2-receptors/
https://my3.my.umbc.edu/api/v0/pixel/news/64600/guest@my.umbc.edu/2eb9b42760edf9e99e3bb080dc41dac3/api/pixel
data-science
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 30 Nov 2016 22:59:45 -0500
Talk: The need for speed in cybersecurity
DHS Dpty Under Sec. of Cybersecurity Dr. Phyllis A. Schneck
CHMPR Distinguished Lecturers Series
Deputy Under Secretary of Cybersecurity
Department of Homeland Security
3:30pm Thur, 1 Dec 2016, UCC 310
3:00pm Coffee, tea, and cookies
As computers get faster, they change the world. Processors get smaller, the number of devices with processors gets bigger, and the amount of information that can be produced and transported grows exponentially. Everything on the planet, unless one can eat it, is likely to have electronic logic within - and, most recently, to be connected to other devices. Our way of life and critical infrastructures, from power and water to finance is enabled by this ability to process light, and transport information at that speed. The speed of computing is enabling new conveniences and capabilities, and furthering science in directions never before imagined from DNA studies to particle physics. This amazingly connected world, however, introduces new vulnerabilities as many connected devices were not designed to be safe from unauthorized access and use. We must pay special attention to protecting infrastructure components such as information and the intricate signaling systems that generate and distribute electricity. This requires specialized algorithms to mine the masses of data to recognize normal internet activity from potential threat indicators. The goal is to create a more self-healing network, accomplishing with information what nature does with biological responses - creating an electronic immune system. Cognitive computing can provide groundbreaking results in data mining and analysis that will enhance the Cybersecurity to protect the other applications such as genomic and physics research. Software and hardware developers need to work together to create the algorithms and custom hardware to minimize heat, maximize computation and, finally, create a secure design.
We can use the speed of computing to enhance Cybersecurity as well - thus the paradox of the need for speed to protect itself.
Dr. Phyllis Schneck is the Deputy Under Secretary for Cybersecurity & Communications with the Department of Homeland Security, where she is also the Chief Cybersecurity Official. Previously held positions include Chief Technology Officer for Global Public Sector, McAfee, Inc.; VP of Enterprise Services, eCommSecurity; and VP of Corporate Strategy for SecureWorks, Inc. Schneck earned her Ph.D. in computer science from Georgia Tech and pioneered the field of info security and security-based high-performance computing at Georgia Tech. She holds seven information security patents and has six research publications in the areas of info security, real-time systems, telecom and software engineering.
I
f you plan on attending, please RSVP to Michelle Bobovych at
bobovych@umbc.edu to ensure we have a sufficient number of chairs.

CHMPR Distinguished Lecturers Series
The Need for Speed
Deputy Under Secretary of Cybersecurity
Department of Homeland Security
3:30pm Thursday, 1 December 2016, UC 310
3:00pm Coffee, tea, and cookies
As computers get faster, they change the world. Processors get smaller, the number of devices with processors gets bigger, and the amount of information that can be produced and transported grows exponentially. Everything on the planet, unless one can eat it, is likely to have electronic logic within – and, most recently, to be connected to other devices. Our way of life and critical infrastructures, from power and water to finance is enabled by this ability to process light, and transport information at that speed. The speed of computing is enabling new conveniences and capabilities, and furthering science in directions never before imagined from DNA studies to particle physics. This amazingly connected world, however, introduces new vulnerabilities as many connected devices were not designed to be safe from unauthorized access and use. We must pay special attention to protecting infrastructure components such as information and the intricate signaling systems that generate and distribute electricity. This requires specialized algorithms to mine the masses of data to recognize normal internet activity from potential threat indicators. The goal is to create a more self-healing network, accomplishing with information what nature does with biological responses – creating an electronic immune system. Cognitive computing can provide groundbreaking results in data mining and analysis that will enhance the Cybersecurity to protect the other applications such as genomic and physics research. Software and hardware developers need to work together to create the algorithms and custom hardware to minimize heat, maximize computation and, finally, create a secure design.
We can use the speed of computing to enhance Cybersecurity as well – thus the paradox of the need for speed to protect itself.
Dr. Phyllis Schneck is the Deputy Under Secretary for Cybersecurity & Communications with the Department of Homeland Security, where she is also the Chief Cybersecurity Official. Previously held positions include Chief Technology Officer for Global Public Sector, McAfee, Inc.; VP of Enterprise Services, eCommSecurity; and VP of Corporate Strategy for SecureWorks, Inc. Schneck earned her Ph.D. in computer science from Georgia Tech and pioneered the field of info security and security-based high-performance computing at Georgia Tech. She holds seven information security patents and has six research publications in the areas of info security, real-time systems, telecom and software engineering.
If you plan on attending, please RSVP to Michelle Bobovych at *protected email* to ensure we have a sufficient number of chairs.
The post talk: Dr. Phyllis Schneck (DHS) on The Need for Speed in Cybersecurity appeared first on Department of Computer Science and Electrical Engineering.
]]>
CHMPR Distinguished Lecturers Series The Need for Speed Dr. Phyllis A. Schneck Deputy Under Secretary of Cybersecurity Department of Homeland Security 3:30pm Thursday, 1 December 2016, UC...
https://www.csee.umbc.edu/2016/11/talk-phyllis-schneck-dhs-cybresecurity/
https://my3.my.umbc.edu/api/v0/pixel/news/64601/guest@my.umbc.edu/c232c85dcd5cfcaa03d8c06fb777f31f/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 29 Nov 2016 10:23:42 -0500
UMBC Hour of Code, 11-2 Dec 7-8, Main Street
The CS Education student org, with support from the CS Matters in Maryland CS education project, is planning UMBC’s first-ever Hour of Code event. Hour of Code is an initiative that organizes hands-on learning experiences for students of all ages during CS Education Week (December 5-11, 2016, coinciding with Admiral Grace Hopper’s birthday).
UMBC’s Hour of Code will offer a hands-on experience for anybody who wants to try their hand at coding, December 7 and 8 from 11am-2pm on Main Street. We will have several special guests on Thursday — some students from Lakeland Elementary School will learn to code along with President Freeman Hrabowski from 11am-noon that day.
We need many volunteers to help make this event a success! Although coding experience is useful, it is NOT necessary! We will have training events in advance of the event for everyone who volunteers, and we also have some no-coding-required jobs as well, including running a Makey Makey activity and helping out with the elementary school students.
Please sign up to volunteer. Stephanie Milani (Psychology major / CS minor) is organizing the volunteer effort — please feel free to contact her if you have any questions at *protected email*
The post UMBC Hour of Code, 11-2 Dec 7-8, Main Street appeared first on Department of Computer Science and Electrical Engineering.
]]>
The CS Education student org, with support from the CS Matters in Maryland CS education project, is planning UMBC’s first-ever Hour of Code event. Hour of Code is an initiative that organizes...
https://www.csee.umbc.edu/2016/11/umbc-hour-of-code-2016/
https://my3.my.umbc.edu/api/v0/pixel/news/64602/guest@my.umbc.edu/8f8b8c40ab2c88d63c9c71be59e7fd8d/api/pixel
computer-engineering
computer-science
education
news
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Mon, 21 Nov 2016 13:43:31 -0500
Boosting Base-Station Anonymity in Wireless Sensor Networks
Sami Alsemairi PhD DIssertation Defense, 9:30 Wed Nov. 9, IT
Dissertation Defense Announcement
Cross-Layer Techniques for Boosting Base-Station Anonymity in Wireless Sensor Networks
Sami Alsemairi
9:30 Wednesday, 9 November 2016, ITE 346
Wireless Sensor Networks (WSNs) provide an effective solution for surveillance and data gathering applications in hostile environments where human presence is infeasible, risky or very costly. Examples of these applications include military reconnaissance, guarding boarders against human trafficking, security surveillance, etc. A WSN is typically composed of a large number of sensor nodes that probe their surrounding and transmit measurements over multi-hop paths to an in-situ Base-Station (BS). The BS not only acts as a sink of all collected sensor data but also provides network management and serves as a gateway to remote commend centers. Such an important role makes the BS a target of adversary attacks that opt to achieve Denial-of-Service (DoS) and nullify the WSN utility to the application. Even if the WSN applies conventional security mechanisms such as authentication and data encryption, the adversary may apply traffic analysis techniques to locate the BS and target it with attacks. This motivates a significant need for boosting BS anonymity to conceal its location.
In this dissertation, we address the challenges of BS anonymity and develop a library of techniques to counter the threat of traffic analysis. The focus of our work is on the link and network layers. We first exploit packet combining as a means to vary the traffic density throughout the network. We call this technique combining the data payload of multiple packets (CoDa), where a node groups the payload of multiple incoming data packets into a single packet that is forwarded toward the BS. CoDa cuts on the number of transmissions that constitute evidences for implicating the BS as a destination of all traffic and thus degrades the adversary’s ability in conducting effective traffic analysis.
Next we develop a novel technique for increasing BS anonymity by establishing a sleep/active schedule among the nodes that are far away from the BS, and increasing the traffic density in selected parts of the network in order to give the impression that the BS is located in the vicinity of the sleeping nodes. We call this technique Adaptive Sampling Rate for increased Anonymity (ASRA). Moreover, we develop three novel techniques based on a hierarchical routing topology. The first, which we call Hierarchical Anonymity-aware Routing Topology (HART), forms clusters and an inter-cluster-head routing topology so that a high traffic volume can be observed in areas away from the BS. The second is a novel cross-layer technique that forms a mesh topology. We call this technique cluster mesh topology to boost BS’s anonymity (CMBA). CMBA opts to establish a routing topology such that the traffic pattern does not implicate any particular node as a sink.
The third technique creates multiple mesh-based routing topologies among the cluster-heads (CHs). By applying the closed space-filling curves such as the Moore curve, for forming a mesh, the CHs are offered a number of choices for disseminating aggregated data to the BS through inter-CH paths. Then, the BS forwards the aggregated data as well so that it appears as one of the CH. We call this technique boosting the BS anonymity through multiple mesh-based routing topologies (BAMT). We validate the effectiveness of all anonymity-boosting techniques through simulation and highlight the trade-off between anonymity and overhead.
Committee: Drs. Mohamed Younis (Chair), Charles Nicholas, Chintan Patel, Richard Forno and Waleed Youssef
]]>
Dissertation Defense Announcement Cross-Layer Techniques for Boosting Base-Station Anonymity in Wireless Sensor Networks Sami Alsemairi 9:30 Wednesday, 9 November 2016, ITE 346 Wireless...
https://www.csee.umbc.edu/2016/11/cross-layer-techniques-boosting-base-station-anonymity-wireless-sensor-networks/
https://my3.my.umbc.edu/api/v0/pixel/news/63726/guest@my.umbc.edu/e3c3ac04a407a140aca27d4f21681882/api/pixel
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/xxlarge.jpg?1478579259
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/xlarge.jpg?1478579259
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/large.jpg?1478579259
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/medium.jpg?1478579259
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/small.jpg?1478579259
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/xsmall.jpg?1478579259
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/726/a76d17856fa028a3edcc0af51f345410/xxsmall.jpg?1478579259
3
0
true
Mon, 07 Nov 2016 23:27:56 -0500
Mon, 07 Nov 2016 23:29:17 -0500
Engineering Plaintext Private Information Retrieval Systems
A talk by UMBC alumnus Dr. Russ Fink, 1pm Fri 11/4, ITE229
Practical Engineering of Plaintext
Private Information Retrieval Systems
Dr. Russell Fink
Chief Engineer, Cyber Operations Branch
Johns Hopkins University Applied Physics Laboratory
1-2pm Friday, 4 November 2016, ITE 229
Cloud computing has come a long way in the last decade, with many advances in supported platforms, security, and cost effectiveness. As organizations are increasingly turning to the cloud to outsource their big data storage and processing needs, both problems and opportunities arise for understanding and analyzing large repositories of data.
One problem in particular is querying large data in a safe and secure way – querying a large data set can compromise search privacy, revealing the interests, motivations, and true identity of the data querier to the data owner, hindering legitimate uses including data analytics, security, and law enforcement. Alice, wishing to search Bob’s queue of plaintext data, may turn to Private Information Retrieval (PIR) techniques to maintain her privacy without sacrificing bandwidth or deploying a trusted device in Bob’s spaces.
We have prototyped a PIR system based on the homomorphic Paillier cryptosystem and Bethencourt/Song search method, and discovered important engineering techniques along the way that are useful for deploying a scalable system. In this talk, I will introduce and motivate the PIR problem and describe the Paillier homomorphic retrieval system and Bethencourt’s technique. I will give an overview of our specific advances, notably, a novel technique for private regular expression pattern searching over plaintext, including an algorithm for resisting a privacy attack against the resulting search automaton.
Russell A. (“Russ”) Fink is the Chief Engineer of the Cyber Operations Branch, Asymmetric Operations Sector, of the Johns Hopkins University Applied Physics Laboratory. He holds a Bachelor’s degree in computer science from the University of Maryland, College Park; a Master’s degree in computer systems management from the University of Maryland, University College; and a Ph.D. from the University of Maryland, Baltimore County for his work on electronic voting and trustworthy computing. His research interests include systems security engineering, trusted computing, machine learning, and privacy preserving cryptographic applications.
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks.
Statistics and Big Data at Google
Dr. Tim Hesterberg, Google
5:00-6:00pm Thursday, 3 November 2016
UC 310, UMBC
Google lives on data. Search, Ads, YouTube, Maps...they all live on data. Join Senior Quantitative Analyst (and Lady Statistician) Tim Hesterberg, as he shares stories about how we use data, how we're experimenting to make improvements (yes, this includes your searches), and how we adapt statistical ideas to do things that have never been done before. This will be a general-audience, non-technical talk. No statistics background is needed!
Dr. Tim Hesterberg is a Senior Statistician at Google. He previously worked at Insightful (S-PLUS), Franklin & Marshall College, and Pacific Gas & Electric Co. He received his Ph.D. in Statistics from Stanford University, under Brad Efron. Hesterberg is author of the "Resample" package for R and primary author of the "S+Resample" package for bootstrapping, permutation tests, jackknife, and other resampling procedures, is co-author of Chihara and Hesterberg "Mathematical Statistics with Resampling and R" (2011), and is lead author of "Bootstrap Methods and Permutation Tests" (2010), W. H. Freeman, ISBN 0-7167-5726-5, and numerous technical articles on resampling.
]]>
Statistics and Big Data at Google Dr. Tim Hesterberg, Google 5:00-6:00pm Thursday, 3 November 2016 UC 310, UMBC Google lives on data. Search, Ads, YouTube, Maps...they all live on data. Join...
https://www.csee.umbc.edu/2016/11/hesterberg-statistcs-big-data-google/
https://my3.my.umbc.edu/api/v0/pixel/news/63582/guest@my.umbc.edu/86f352aa7c055cfa9c35ba2d6f6198d8/api/pixel
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/xxlarge.jpg?1478053110
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/xlarge.jpg?1478053110
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/large.jpg?1478053110
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/medium.jpg?1478053110
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/small.jpg?1478053110
https://assets4-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/xsmall.jpg?1478053110
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/582/7176562eb0d9aab6bacb1f87bfd5708c/xxsmall.jpg?1478053110
1
0
true
Tue, 01 Nov 2016 22:20:44 -0400
Six new SFS cybersecurity scholars to join UMBC in 2017
Six new cybersecurity scholars were inducted into UMBC's NSF-sponsored Scholarship for Service program in an event held in Germantown on October 20. Three are currently students at Montgomery College and three are from Prince Georges Community College. After they complete their associates degree in spring 2017, they will transfer to UMBC to complete their undergraduate degrees.
This pioneering cooperation between UMBC, Montgomery College, and Prince Georges Community College in cybersecurity is made possible by a
grant from the National Science Foundation (Dr.
Alan Sherman (UMBC),
Joe Roundy (MC), and
Casey O'Brien (PGCC), CoPIs).
As part of their education, the SFS scholars will solve IT security problems for their county government.
As SFS Scholars, the students receive tuition, fees, annual reimbursement of professional development expenses, a nine-month stipend and assistance with federal cybersecurity internships and career placement.
]]>
Six new cybersecurity scholars were inducted into UMBC's NSF-sponsored Scholarship for Service program in an event held in Germantown on October 20. Three are currently students at Montgomery...
https://www.csee.umbc.edu/2016/10/new-umbc-sfs-cybersecurity-scholars/
https://my3.my.umbc.edu/api/v0/pixel/news/63542/guest@my.umbc.edu/7f7400a568ffeaf44dff4509a9aaa511/api/pixel
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/xxlarge.jpg?1477935258
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/xlarge.jpg?1477935258
https://assets1-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/large.jpg?1477935258
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/medium.jpg?1477935258
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/small.jpg?1477935258
https://assets3-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/xsmall.jpg?1477935258
https://assets2-my.umbc.edu/system/shared/thumbnails/news/000/063/542/16a8377b6822cf94bd3e69f57df6dac6/xxsmall.jpg?1477935258
1
0
true
Mon, 31 Oct 2016 13:35:19 -0400