UMBC Cyberdawgs Win 2015 Maryland Cyber Challenge

The Maryland Cyber Challenge, or MDC3, is held in Baltimore each year. The competition, organized by the CyberNEXS division of Leidos, provides a hands-on cybersecurity competition for participants through, among other things, a “king of the hill” style challenge. The event tests not only a team’s ability to break into a target machine, but also its ability to secure that machine from attacks by other competitors. In addition, competitors are given a forensics image of a computer, and tasked with finding hidden flags within the image.
In 2015, about 25 college and university teams qualified for the semi-finals, and eight of those teams made it to the finals. That eight includes two teams from UMBC: Cyberdawgs 1 and Cyberdawgs 2. The final round of competition began on October 28, but technical difficulties prevented the contest from finishing.
The contest resumed at noon on Saturday, February 20, 2016. The Cyberdawgs Team 1, Tyler Campbell, Josh Domangue, Chris Gardner, Anh Ho, Jacob Rust, and Julio Valcarcel took first place with 18,979 points, outscoring the winning team in the professional division by 5690 points. (No other results or point totals were released.)
The Cyber Defense Team’s meetings are open to all students that have a desire to learn hands-on cybersecurity skills, and no prior cyber experience is needed. The club meets during the Spring 2016 semester on Wednesdays at 7:10PM in ITE 231. To request access to their mailing list, send an email to Sorry, you need javascript to view this email address. If you have any questions about the club feel free to email Julio Valcarcel (Sorry, you need javascript to view this email address. ) or Anh Ho (Sorry, you need javascript to view this email address. ). The Cyber Defense Team’s faculty advisers are Dr. Charles Nicholas (Sorry, you need javascript to view this email address. ) and Dr. Rick Forno (Sorry, you need javascript to view this email address. ).
]]>
The Maryland Cyber Challenge, or MDC3, is held in Baltimore each year. The competition, organized by the CyberNEXS division of Leidos, provides a hands-on cybersecurity competition for...
http://www.csee.umbc.edu/2016/02/cyberdawgs-win-2015-maryland-cyber-challenge/
https://my3.my.umbc.edu/api/v0/pixel/news/58114/guest@my.umbc.edu/30505ed2fbd4b7096f19eada06a71ebb/api/pixel
computer-science
csee
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
9
0
true
Wed, 24 Feb 2016 15:37:45 -0500
Wed, 24 Feb 2016 15:37:45 -0500
talk: Learning from High-Dimensional Data via Transformations, 2/29
Learning from High-Dimensional Data via Transformations
Dr. Hossein Mobahi, MIT
12:00pm Monday 29, February 2016, ITE325b
High-dimensional data is ubiquitous in the modern world, arising in images, movies, biomedical measurements, documents, and many other contexts. The “curse of dimensionality” tells us that learning in such regimes is generally intractable. However, practical problems often exhibit special simplifying structures which, when identified and exploited, can render learning in high dimensions tractable. This is a great prospect however, but how to get there in not trivial. In this talk, I will address two challenges associated with high-dimensional learning and discuss my proposed solution.
First, parsimony (sparsity, low rank, etc.) is one of the most prevalent structures in high-dimensional learning applications. However, its presence is often implicit and it reveals itself only after a transformation of the data. Studying the space of such transformations and the associated algorithms for their inference constitute an important class of problems in high-dimensional learning. I will present some of my work in this direction related to image segmentation. I will show how low-rank structures become abundant in images when certain spatial and geometric transformations are considered. This work resulted in a state of the art algorithm for segmentation of natural images.
Second, important scenarios such as deep learning involve high-dimensional nonconvex optimization. Such optimization is generally intractable. However, I show how some properties in the optimization landscape, such as smoothness and stability, can be exploited to transform the objective function to simpler subproblems and allow obtaining reasonable solutions efficiently. The theory is derived by combining the notion of convex envelopes with differential equations. This results in algorithms involving high-dimensional convolution with the Gaussian kernel, which I show has a closed form in many practical scenarios. I will present applications of this work in image alignment, image matching, and deep learning. Furthermore, I will discuss how this theory justifies heuristics currently used in deep learning and suggests new training algorithms that offer a significant speedup.
Hossein Mobahi is a postdoctoral researcher in the Computer Science and Artificial Intelligence Lab at the Massachusetts Institute of Technology. His research interests include machine learning, computer vision, optimization, and especially the intersection of the three. He obtained his PhD from the University of Illinois at Urbana-Champaign in Dec 2012. He is the recipient of Computational Science & Engineering Fellowship, Cognitive Science & AI Award, and Mavis Memorial Scholarship. His recent work on machine learning and optimization have been covered by the MIT news.
]]>
Learning from High-Dimensional Data via Transformations Dr. Hossein Mobahi, MIT 12:00pm Monday 29, February 2016, ITE325b High-dimensional data is ubiquitous in the modern world, arising in...
http://www.csee.umbc.edu/2016/02/talk-learning-from-high-dimensional-data-via-transformations-229/
https://my3.my.umbc.edu/api/v0/pixel/news/58098/guest@my.umbc.edu/e7d895191341a74ccf04d331c00f0de2/api/pixel
computer-engineering
data-science
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 21 Feb 2016 22:25:51 -0500
talk: Mini-MAC: Raising the Bar for Vehicular Security with a Lightweight Message Authentication Protocol

The UMBC Cyber Defense Lab presents
Mini-MAC: Raising the Bar for Vehicular Security with a
Lightweight Message Authentication Protocol
Jackson Schmandt, CSEE, UMBC
11:15am-12:30pm Friday, 26 February 2016, ITE 237
We propose Mini-MAC, a new message authentication protocol that works in existing automotive computer networks without delaying any message or increasing network traffic. Deployed in many vehicles, the CAN bus is a low-speed network connecting electronic control units, including those that control critical functionality such as braking and acceleration. The CAN bus is extremely vulnerable to malicious actors with bus access, including wireless access. Traditionally, Message Authentication Codes (MACs) help authenticate the sender of a message, and variants prevent message replay attacks; however, standard MACs are unsuitable for use on the CAN bus because of small payload sizes. Restrictions of the CAN bus, including the need not to delay messages or increase bus traffic, severely limit how well this network can be protected.
Mini-MAC is based on a counter-seeded keyed-Hash MAC (HMAC), augmented with message history and truncated to fit available message space. It does not increase bus traffic and incurs a very small performance penalty relative to the provably secure HMAC. It is the first proposal to combine these two tenets for vehicle networks. The message history feature protects against all transient attackers, even if they know the keys. Though the CAN bus cannot be properly secured against a dedicated attacker, Mini-MAC meaningfully raises the bar of vehicular security, enhancing the safety of drivers and others.
Jackson Schmandt is a MS student in Computer Engineering in the Mobile Pervasive Sensor System Lab. Joint work with Alan Sherman and Nilanjan Banerjee.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Mini-MAC: Raising the Bar for Vehicular Security with a Lightweight Message Authentication Protocol Jackson Schmandt, CSEE, UMBC 11:15am-12:30pm Friday,...
http://www.csee.umbc.edu/2016/02/talk-mini-mac-raising-the-bar-for-vehicular-security-with-a-lightweight-message-authentication-protocol/
https://my3.my.umbc.edu/api/v0/pixel/news/58000/guest@my.umbc.edu/8dbe2114a6646b1305be9b399227d7c9/api/pixel
computer-engineering
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 21 Feb 2016 16:51:39 -0500
Sun, 21 Feb 2016 16:51:39 -0500
talk: Trust and Integrity in Modern Supply Chains, 11:30 2/25
Establishment of Trust and Integrity in Modern Supply Chains
Ujjwal Guin, University of Connecticut
11:30 Thursday, 25 February 2016, ITE325b
With the advent of globalization and resulting horizontal integration, modern supply chain becomes extremely complex and requires immediate solutions for eliminating counterfeit integrated circuits (ICs), which pose a serious threat to the safety and security of our day-to-day lives. The reliability of such ICs could be questionable as they may have many defects and might not go through as much of a rigorous test process as their authentic counterparts. An adversary can also create a backdoor to bypass the security modules in these ICs. In this research, I have systematically addressed the aforementioned issues by risk analysis and assessment of test methods, and by proposing different Design-for-Anti-Counterfeit (DfAC) measures. As a part of risk analysis, I have developed taxonomies for counterfeit IC types, counterfeit defects, and test methods. Based on these taxonomies, I have introduced novel test metrics and developed a comprehensive framework for assessing a set of test methods to maximize test coverage. In the DfAC domain, I have proposed a suite of solutions to detect counterfeit ICs without performing conventional tests. A set of lightweight negative-bias temperature instability (NBTI)-aware ring oscillators have been developed for combating die and IC recycling. In addition, I have developed a comprehensive solution for preventing intellectual property piracy and IC overproduction by assuring forward trust between all entities involved in the system-on-chip design and fabrication process.
Ujjwal Guin is a PhD candidate at the Electrical and Computer Engineering department of University of Connecticut, where he has been working with Dr. Mark M. Tehranipoor. His current research interests include Hardware Security and Trust, Supply Chain Security, Cybersecurity, and VLSI Design and Test. He has developed several on-chip structures and techniques to improve the security, trustworthiness, and reliability of integrated circuits. He has co-authored a book entitled “Counterfeit Integrated Circuits – Detection and Avoidance”. He has published several journal articles and refereed conference papers. He received Best Student Paper Award from the IEEE North Atlantic Test Workshop (NATW’2013). He is an active participant in the SAE International’s G-19A Test Laboratory Standards Development Committee. Mr. Guin received his B.E. degree from the Department of Electronics and Telecommunication Engineering of Bengal Engineering and Science University, Howrah, India in 2004 and the M.Sc. degree from the Department of Electrical and Computer Engineering of Temple University, Philadelphia, PA, USA in 2010.
Host: Chintan Patel
]]>
Establishment of Trust and Integrity in Modern Supply Chains Ujjwal Guin, University of Connecticut 11:30 Thursday, 25 February 2016, ITE325b With the advent of globalization and resulting...
http://www.csee.umbc.edu/2016/02/trust-integrity-hardware-supply-chains/
https://my3.my.umbc.edu/api/v0/pixel/news/57996/guest@my.umbc.edu/af52d075569978cbf3f2c5b09fae7ff9/api/pixel
computer-engineering
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 21 Feb 2016 11:53:55 -0500
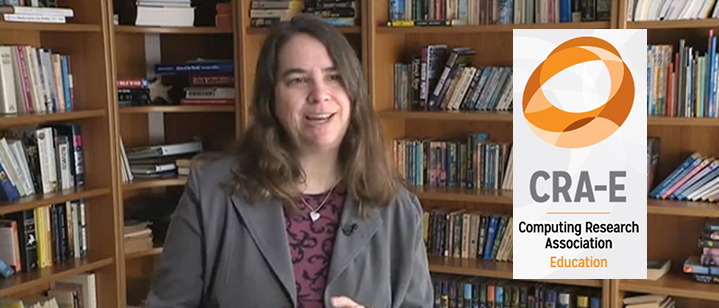
Marie desJardins recognized by CRA for Undergraduate Research Mentoring
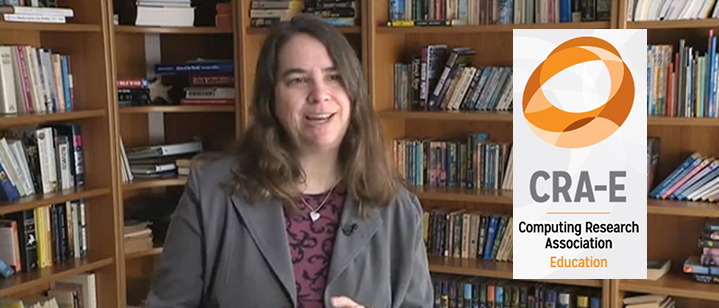
CSEE professor Marie desJardins has received an Undergraduate Research Faculty Mentoring Award from the Computing Research Association (CRA). The award recognizes faculty who have provided exceptional mentorship, undergraduate research experiences, and, in parallel, guidance on admission and matriculation of undergraduate students to research-focused graduate programs in computing. The award will be presented to Dr. desJardins at the CRA Conference at Snowbird in July.
Dr. desJardins is a professor in UMBC’s Computer Science and Electrical Engineering department and Associate Dean of the College of Engineering and Information Technology. Her research is in the area of artificial intelligence, machine learning, and computer science education. Currently, her research group includes six undergraduates and five graduate students. Since 2005, she has mentored over 70 undergraduate students. At least 29 of them have enrolled in graduate programs in computing, with eight of the 29 having pursued a Ph.D. in computer science.
In announcing the award, the CRA noted that
“Many of the undergraduates Marie has mentored never imagined that they would be involved in research and consider graduate education. Marie’s strategy for working with undergraduate majors involves engaging with students in their first two years and building teams in which her more senior research students (graduate and undergraduate) help train and lead the junior students. She is known for her unconditional support, encouragement, and dedication. She encourages students from underrepresented minorities to get involved with national organizations and programs, including CRA-W, NCWIT, Grace Hopper, IJCAI and AAAI. She stays in touch with her mentees beyond their graduation, and she has helped some to become effective mentors themselves.”
This is the first year for the CRA Undergraduate Research Faculty Mentoring Award, which was also given to Pieter Abbeel of the University of California, Berkeley and Judy Goldsmith from the University of Kentucky.
Founded in 1972, CRA‘s membership includes more than 200 North American organizations active in computing research: academic departments of computer science and computer engineering, laboratories and centers (industry, government, and academia), and affiliated professional societies (AAAI, ACM, CACS/AIC, IEEE Computer Society, SIAM, USENIX). Its mission is to enhance innovation by joining with industry, government and academia to strengthen research and advanced education in computing. CRA executes this mission by leading the computing research community, informing policymakers and the public, and facilitating the development of strong, diverse talent in the field.
]]>
CSEE professor Marie desJardins has received an Undergraduate Research Faculty Mentoring Award from the Computing Research Association (CRA). The award recognizes faculty who have provided...
http://www.csee.umbc.edu/2016/02/marie-desjardins-recognized-by-cra-for-undergraduate-research-mentoring/
https://my3.my.umbc.edu/api/v0/pixel/news/57964/guest@my.umbc.edu/090abf5e04823aa218102b5b9ea2a8a9/api/pixel
computer-science
education
faculty-and-staff
news
research
teaching-innovation
undergraduate
undergraduate-researcher-profile
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
1
true
Fri, 19 Feb 2016 12:25:08 -0500
Fri, 19 Feb 2016 12:25:08 -0500
Rick Forno discusses Apple-FBI iPhone situation with BBC Radio

Dr. Rick Forno, Cybersecurity Graduate Program Director and Assistant Director of the UMBC Center for Cybersecurity, offered comments to BBC Radio Five regarding the issue of Apple being compelled by a federal judge to facilitate FBI access to an encrypted iPhone used by one of the San Bernadino attackers.
During the interview, he provided initial reactions to this developing situation and what the longer-term ramifications for Apple, the FBI, and privacy generally. From his perspective, Forno thinks it is possible for Apple to update one specific device so that the Department of Justice can access the content on that device, which would allow Apple to comply with the order. However, Forno explains that the real issue involved is the question of the future. “What is to stop the FBI or law enforcement—state, local, global—from contacting Apple asking for the same consideration on other devices,” he says.
(The story’s lead-in starts at 1:05:30 followed by his comments via Skype a few minutes later.)
]]>
Dr. Rick Forno, Cybersecurity Graduate Program Director and Assistant Director of the UMBC Center for Cybersecurity, offered comments to BBC Radio Five regarding the issue of Apple being compelled...
http://www.csee.umbc.edu/2016/02/rick-forno-discusses-apple-fbi-iphone-situation-with-bbc-radio/
https://my3.my.umbc.edu/api/v0/pixel/news/57934/guest@my.umbc.edu/314bf519d6fea656635a177cd6020a53/api/pixel
computer-science
cybersecurity
in-the-news
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 18 Feb 2016 11:29:57 -0500
Thu, 18 Feb 2016 11:29:57 -0500
talk: Leveraging human insights into problem structure for scientific discovery
Leveraging Human Insights into
Problem Structure for Scientific Discovery
Ronan Le Bras, Cornell University
12:00pm 1:00pm Tuesday, 23 February 2016, ITE325b, UMBC
Most problems, from theoretical problems in combinatorics to real-world applications, comprise hidden structural properties not directly captured by the problem definition. A key to the recent progress in automated reasoning and combinatorial optimization has been to automatically uncover and exploit this hidden problem structure, resulting in a dramatic increase in the scale and complexity of the problems within our reach. The most complex tasks, however, still require human abilities and ingenuity. In this talk, I will show how we can leverage human insights to effectively complement and dramatically boost state-of-the-art optimization techniques. I will demonstrate the effectiveness of the approach with a series of scientific discoveries, from experimental designs to materials discovery.
Ronan Le Bras is a Ph.D. candidate in computer science at Cornell University. He received his M.S. and B.S. from Ecole Polytechnique Montreal in computer engineering and in software engineering. His research interests include computational methods for large-scale combinatorial optimization, reasoning, learning and human computation. His work is motivated by a range of applications, especially in the emerging field of computational sustainability. It has led to a series of scientific discoveries in areas such as graph theory, combinatorics, and discrepancy theory as well as materials science, experimental design and conservation biology. His work appears in the proceedings of AAAI, IJCAI, HCOMP, SAT, CP and VLDB.
Host: Tim Finin, Sorry, you need javascript to view this email address.
]]>
Leveraging Human Insights into Problem Structure for Scientific Discovery Ronan Le Bras, Cornell University 12:00pm 1:00pm Tuesday, 23 February 2016, ITE325b, UMBC Most problems, from...
http://www.csee.umbc.edu/2016/02/talk-leveraging-human-insights-into-problem-structure-for-scientific-discovery/
https://my3.my.umbc.edu/api/v0/pixel/news/57887/guest@my.umbc.edu/f0e31ffce8cfe18b7e83b8600d13e186/api/pixel
computer-science
data-science
news
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 17 Feb 2016 08:42:27 -0500
Wed, 17 Feb 2016 08:42:27 -0500
talk: From Forensics to Security, 1pm Fri 2/19 ITE325b

From Forensics to Security: Securing Complex
Systems through Data-driven Investigation
Dr. Robert Walls
Pennsylvania State University
1:00pm Friday, 19 February 2016, ITE 325b, UMBC
The cornerstone of modern security is understanding when and how systems are abused and exploited. Gathering such knowledge is essential as decades of experience demonstrate the infeasibility of building perfectly secure systems. Yet, the systems with the greatest need of securing—such as those underpinning critical Internet services—are often the most difficult to study.
In this talk, I will focus on my research efforts in digital forensics and security to study the abuse of complex and inter-connected systems. My work has focused on multiple aspects of this endeavor, including the analysis of partially structured data, the use of semantic relationships and investigator feedback to identify relevant information, and the transition of research results into practical tools and techniques.
Robert Walls is a Postdoctoral Scholar in the Department of Computer Science and Electrical Engineering at The Pennsylvania State University. His research interests include systems security and digital forensics. He is currently studying the abuse of Internet infrastructure, including advertising networks and the Domain Name System (DNS). Previously, he worked with law enforcement to develop novel forensic techniques for investigating crimes. He received his Ph.D. in Computer Science from the University of Massachusetts Amherst in 2014. He is also a recipient of the Yahoo! Key Scientific Challenges Award.
Host: Tim Finin, Sorry, you need javascript to view this email address.
]]>
From Forensics to Security: Securing Complex Systems through Data-driven Investigation Dr. Robert Walls Pennsylvania State University 1:00pm Friday, 19 February 2016, ITE 325b, UMBC The...
http://www.csee.umbc.edu/2016/02/talk-from-forensics-to-security-1pm-fri-219-ite325b/
https://my3.my.umbc.edu/api/v0/pixel/news/57798/guest@my.umbc.edu/431065ba41627f1bdf7b3405b9410eb9/api/pixel
computer-science
cybersecurity
data-science
news
other
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 16 Feb 2016 00:21:55 -0500
Tue, 16 Feb 2016 00:21:55 -0500
talk: From Forensics to Security, 1pm Fri 2/19 ITE325b

From Forensics to Security: Securing Complex
Systems through Data-driven Investigation
Dr. Robert Walls
Pennsylvania State University
1:00pm Friday, 19 February 2016, ITE 325b, UMBC
The cornerstone of modern security is understanding when and how systems are abused and exploited. Gathering such knowledge is essential as decades of experience demonstrate the infeasibility of building perfectly secure systems. Yet, the systems with the greatest need of securing—such as those underpinning critical Internet services—are often the most difficult to study.
In this talk, I will focus on my research efforts in digital forensics and security to study the abuse of complex and inter-connected systems. My work has focused on multiple aspects of this endeavor, including the analysis of partially structured data, the use of semantic relationships and investigator feedback to identify relevant information, and the transition of research results into practical tools and techniques.
Robert Walls is a Postdoctoral Scholar in the Department of Computer Science and Electrical Engineering at The Pennsylvania State University. His research interests include systems security and digital forensics. He is currently studying the abuse of Internet infrastructure, including advertising networks and the Domain Name System (DNS). Previously, he worked with law enforcement to develop novel forensic techniques for investigating crimes. He received his Ph.D. in Computer Science from the University of Massachusetts Amherst in 2014. He is also a recipient of the Yahoo! Key Scientific Challenges Award.
Host: Tim Finin, Sorry, you need javascript to view this email address.
]]>
From Forensics to Security: Securing Complex Systems through Data-driven Investigation Dr. Robert Walls Pennsylvania State University 1:00pm Friday, 19 February 2016, ITE 325b, UMBC The...
https://www.csee.umbc.edu/2016/02/talk-from-forensics-to-security-1pm-fri-219-ite325b/
https://my3.my.umbc.edu/api/v0/pixel/news/57853/guest@my.umbc.edu/f6f7cf3a2dd1bde98b35c76f15bcdc35/api/pixel
computer-science
cybersecurity
data-science
news
other
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 16 Feb 2016 00:21:55 -0500
2016 Maryland Computing Education Summit, April 12, UMBC

On Tuesday, April 12, 2016, the CS Matters in Maryland project and the Maryland State Department of Education will jointly host a CE21-Maryland Summit for Computing Education at the University of Maryland, Baltimore County (UMBC) campus in Baltimore, Maryland. This event invites the attendance of teachers, administrators, legislators, industry leaders, and others who have an interest in expanding computer science in Maryland schools. UMBC President Freeman Hrabowski will be the summit’s keynote speaker.
Register here for the Maryland computing education summit. The early registration deadline for this event is February 29. Participants who register by the early deadline will receive a confirmation email no later than March 12 indicating whether your registration is confirmed. Late registrations will be accepted and confirmed on a rolling basis. Walk-in registration will be available if capacity or cancellations permit. All registrations are subject to available capacity at the meeting venue.
More information including the schedule is available here.
]]>
On Tuesday, April 12, 2016, the CS Matters in Maryland project and the Maryland State Department of Education will jointly host a CE21-Maryland Summit for Computing Education at the University of...
http://www.csee.umbc.edu/2016/02/2016-maryland-computing-education-summit-april-12-umbc/
https://my3.my.umbc.edu/api/v0/pixel/news/57637/guest@my.umbc.edu/2d9f225b3f2d9559928bcb9e5f579bf8/api/pixel
computer-engineering
computer-science
education
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 09 Feb 2016 21:56:32 -0500
Tue, 09 Feb 2016 21:56:32 -0500