6th Annual CSEE Welcome Back Picnic, 1-2:30 Wed Sept 9th, 312 University Cntr

The UMBC ACM Student Chapter Committee invites CSEE students, faculty and staff to its sixth annual Welcome Back Picnic. For more information, contact ua20019 at umbc.edu.
Hi All,
To the old timers, welcome back to UMBC! Hope you guys had a great summer! To all the new ones, welcome to UMBC! specifically to CSEE!
Before the semester takes its toll, we @ ACM Student Chapter and CSEE department, would like to invite you to our welcome back picnic (= free food).
It’s a opportunity to socialize with everyone and for the faculty and students to meet each other.
What: Sixth annual CSEE Welcome Back Picnic
Who: Limited to CSEE faculty, staff and students
Date: Wednesday, September 9th, 2015
Time: 1:00pm to 2:30pm
Location: University Center, Room 312
So get ready to dig into some good food and conversations. Have an amazing year ahead! Welcome once again,
UMBC ACM Student Chapter Committee and CSEE department
]]>
The UMBC ACM Student Chapter Committee invites CSEE students, faculty and staff to its sixth annual Welcome Back Picnic. For more information, contact ua20019 at umbc.edu. Hi All, To the old...
http://www.csee.umbc.edu/2015/09/6th-annual-csee-welcome-back-picnic-1-230-wed-sept-9th-312-university-cntr/
https://my3.my.umbc.edu/api/v0/pixel/news/53905/guest@my.umbc.edu/4449d31b2ca662dcaa03c4868fa01e94/api/pixel
csee
events
faculty-and-staff
news
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 07 Sep 2015 19:15:42 -0400
talk: Keith Clark, Programming Robotic Agents, 2pm Fri 10/2, ITE325
Programming Robotic Agents: A Multi-tasking Teleo-Reactive Approach
Keith Clark, Imperial College London
University of Queensland, University New South Wales
joint work with Peter Robinson, University of Queensland
2:00pm Friday, 2 October 2015, ITE325b
We present a multi-threaded/multi-tasking message communicating robotic agent architecture in which the concurrently executing tasks are programmed in TeleoR, a major extension of Nilsson’s Teleo-Reactive Procedures (TR) guard ~> action rule language for robotic agents.
The rule guards query rapidly changing percept facts, and more slowly changing told and remembered facts, using fixed facts, relation and function rules (the agent’s knowledge) in the agent’s deductive BeliefStore. Its operational semantics makes the languages well suited to robot/robot or human/robot co-operative tasks.
TeleoR extends TR in:
- being typed and higher order,
- having a typed higher order LP/FP language, QuLog, for encoding BeliefStore knowledge,
- having extra forms of rules and actions, and o having task atomic procedures to control the deadlock and starvation free sharing of several robotic resources by concurrently executing tasks.
Its use is illustrated in the video at http://bit.ly/teleor. It is being used at UNSW to write the control program for a two armed Baxter robot working in co-operation with a person concurrently engaged in several assembly tasks.
Keith Clark is Emeritus Professor of Computer Science at Imperial College London, England and a Visiting Professor at the University of Queensland and the University New South Wales. He has lectured in both mathematics and computer science.
Host: Sorry, you need javascript to view this email address.
Upcoming talks and directions
]]>
Programming Robotic Agents: A Multi-tasking Teleo-Reactive Approach Keith Clark, Imperial College London University of Queensland, University New South Wales joint work with Peter Robinson,...
http://www.csee.umbc.edu/2015/09/talk-keith-clark-programming-robotic-agents-2pm-fri-102-ite325/
https://my3.my.umbc.edu/api/v0/pixel/news/53907/guest@my.umbc.edu/1223a84b03bbb29514a2ce28068129aa/api/pixel
events
news
other
research
robotics
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 06 Sep 2015 11:23:44 -0400
Mon, 28 Sep 2015 23:23:44 -0400
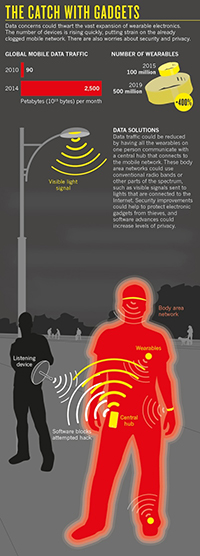
Anupam Joshi quoted in Nature news article on wearable technology

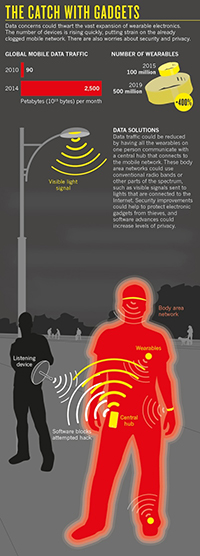
Used with permission by Nature Publishing Group
CSEE chair Anupam Joshi was interviewed and quoted in a news article What could derail the wearables revolution that appears in the current issue of Nature (v525n7567). The piece discusses on two issues caused by the rapid uptake of wearable technology: “finding improved ways to transmit data to and from wearables, and keeping all that information safe.”
The article described research on FaceBlock, a prototype application developed in UMBC’s Ebiquity Lab that can enhance personal privacy in environments with wearable devices like Google Glass.
“It’s a cliché that whenever there’s a new technology we start talking about Huxley and A Brave New World, but with wearables — and what’s loosely termed the Internet of Things — we truly are entering into a new era, and we have to start thinking of these issues,” says Anupam Joshi, head of the Center for Cybersecurity at the University of Maryland, Baltimore County.
…
In another high-profile incident, the introduction of Google Glass headsets two years ago triggered concerns that users would capture images of passers-by without their knowledge. Researchers at the Center for Cybersecurity took this opportunity to apply their work on computer codes that enforce privacy policies. They built the wryly named FaceBlock app, which blocks out the faces of people who have requested privacy from photographs taken by Google Glass. But for this to work, a Google Glass owner would have to opt in by installing the app. So the only way for such a system to reliably provide privacy would be for manufacturers to make it standard and implement it with dedicated hardware, says Joshi. “Let’s say that Google was to build in a feature like this into every Google Glass so that it would automatically obey these kinds of commands — then it would work.”
More information on the FaceBlock prototype and related UMBC research on privacy for wearable technology can be found in these papers.
- Roberto Yus, Primal Pappachan, Prajit Kumar Das, Eduardo Mena, Anupam Joshi and Tim Finin, FaceBlock: Privacy-Aware Pictures for Google Glass, 12th Int. Conf. on Mobile Systems, Applications, and Services, (demonstation paper), ACM, June 2014.
- Primal Pappachan, Roberto Yus, Prajit Kumar Das, Tim Finin, Eduardo Mena, and Anupam Joshi, A Semantic Context-Aware Privacy Model for FaceBlock, Workshop on Society, Privacy and the Semantic Web – Policy and Technology, held at Int. Semantic Web Conf., Oct. 2014.
- Roberto Yus, Primal Pappachan, Prajit Das, Tim Finin, Anupam Joshi and Eduardo Mena, Semantics for Privacy and Shared Context, Workshop on Society, Privacy and the Semantic Web-Policy and Technology, held at Int. Semantic Web Conf., Oct. 2014.
- Prajit Kumar Das, Tim Finin and Anupam Joshi, Energy efficient sensing for managing privacy on smartphones, Workshop on Society, Privacy and the Semantic Web – Policy and Technology, held at 2013 Int. Semantic Web Conf., Oct. 2013.
- Dibyajyoti Ghosh, Anupam Joshi, Tim Finin, and Pramod Jagtap, Privacy control in smart phones using semantically rich reasoning and context modeling, IEEE Workshop on Semantic Computing and Security, pp. 82-85, May 2012
]]>
Used with permission by Nature Publishing Group CSEE chair Anupam Joshi was interviewed and quoted in a news article What could derail the wearables revolution that appears in the current...
http://www.csee.umbc.edu/2015/09/anupam-joshi-quoted-in-nature-news-article-on-wearable-technology/
https://my3.my.umbc.edu/api/v0/pixel/news/53881/guest@my.umbc.edu/144ff383d7179b3ab7f2dd57411f4682/api/pixel
computer-engineering
computer-science
csee
cybersecurity
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 05 Sep 2015 11:41:17 -0400
Sat, 05 Sep 2015 11:41:17 -0400
For Your Convenience at the Munich Airport
"What could possibly go wrong?"
 As Lauren Reid asks, "What could possibly go wrong?"
As Lauren Reid asks, "What could possibly go wrong?"
]]>
As Lauren Reid asks, "What could possibly go wrong?"
https://my3.my.umbc.edu/api/v0/pixel/news/53805/guest@my.umbc.edu/74e2a1eb251c288b5bce9173b972f530/api/pixel
Information Systems Security Association, UMBC Chapter
https://my3.my.umbc.edu/groups/issa
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
1
0
true
Wed, 02 Sep 2015 13:33:09 -0400
Wed, 02 Sep 2015 13:34:39 -0400
UMBC to build immersive virtual reality system with NSF Major Research Infrastructure award
Professors Jian Chen, Penny Rheingans, Karl Steiner, Michael Summers, and Craig Saper received a Major Research Infrastructure grant from the National Science Foundation to build PI2, an immersive virtual reality system to support research in interactive computing and digital humanities.

PI2 will be one of the most advanced visualization facilities of its kind in the mid-Atlantic region. The team sees it as enabling new research efforts on the visual exploration of data and knowledge discovery for biology, math, engineering, visual arts, and digital humanities as well as a tool to study and enhance the potential of the medium itself.
The instrument will feature a curved wall with a 27M pixel resolution made from multi-column, thin-bezel, and stereo-capable LCD panels with a six degree-of-freedom tracking system. The system will integrate and leverage many important characteristics: immersion, hybrid reality, high resolution, large field of view, large space and size, body-centric human-computer interaction, and support for heterogeneous data fusion.
The short-term goal is to accelerate science and education by addressing complex data analysis tasks which may have at least three sources: (1) big data, (2) environments inaccessible or too dangerous for humans so that simulation is necessary, and (3) high-fidelity environments for engineering and human behavior studies.
PI2 is expected to become an integral and vital part of a long-term vision for complex data analysis at UMBC, in effect, a human-computer symbiosis in which humans guide computers to identify features of potential interest that the computer then locates and displays. Developing this vision requires advances in multiple areas, including semi-automatic feature detection, visual representations, and interaction, where traditional display modalities limit what can be displayed and perceived. The instrument will facilitate broad interdisciplinary research and provides an innovative teaching and research environment for a diverse student population. Expectations include:
- Advancing multiple avenues of creative inquiry currently blocked or severely restricted will advance rapidly. The instrument encourages visual thinking among researchers in sciences, healthcare, biomedicine, national security, humanities, and education;
- Establishing appropriate levels of technologies needed for different classes of knowledge discovery analysis; and
- Assembling a set of research projects to investigate the use of the instrument with the expectation of creating a novel, demonstrably useful, rich, and expressive set of techniques for many cyber-physical and cyber-human systems.
PI2 will integrate advances in natural language processing, wearable computing, visualization, data mining, and interaction and its ability to synthesize, capture, create, and analyze visual information in unprecedented detail will transform the way analysts interact with visual information. Its capabilities will benefit multiple research areas at UMBC, including brain connectome, woodland ecology, interpersonal experiences, biomedicine, universal access, engineering physics, simulations, systems biology, education, digital humanities, green technologies, and unmanned-vehicle studies.
For more information, contact Sorry, you need javascript to view this email address. .
]]>
Image from Mechdyne of a visualization wall at the University of Illinois at Chicago’s Electronic Visualization Lab made with displays from Planar. Professors Jian Chen, Penny Rheingans, Karl...
http://www.csee.umbc.edu/2015/08/umbc-to-build-immersive-virtual-reality-system-with-nsf-major-research-infrastructure-award/
https://my3.my.umbc.edu/api/v0/pixel/news/53718/guest@my.umbc.edu/c150691bd46d89fe1d5bef1b850335f4/api/pixel
computer-science
data-science
news
research
research-awards
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
5
1
true
Sun, 30 Aug 2015 15:43:08 -0400
Sun, 30 Aug 2015 15:43:08 -0400
PhD defense: Yu Wang, Physically-Based Modeling and Animation

Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Ph.D. Dissertation Defense
The Modeling Equation: Solving the Physically-Based
Modeling and Animation Problem with a Unified Solution
Yu Wang
12:00pm Friday, 28 August 2015, ITE 352
Physically-based modeling research in computer graphics is based largely on derivation or close approximation from physics laws defining the material behaviors. From rigid object dynamics, to various kinds of deformable objects, such as elastic, plastic, and viscous fluid flow, to their interaction, almost every natural phenomena can find a rich history in computer graphics research. Due to the nonlinear nature of almost all real world dynamics, the mathematical definition of their behavior is rarely linear. As a result, solving for the dynamics of these phenomena involves non-linear numerical solvers, which sometimes introduces numerical instability, such as volume gain or loss, slow convergence.
The contribution of this project is a unified particle-based model that implements an extended SPH solver for modeling fluid motion, integrated with rigid body deformation using shape matching. The model handles phase changes between solid and liquid, including melting and solidification, where material rigidity is treated as a function of time and particle distance to the object surface, and solid fluid coupling, where rigid body motion causes secondary fluid flow motion. Due to the stability of the fluid-rigid interplay solver, we can introduce artistic control to the framework, such as rigging, where object motion is predefined by either artistic control, or procedurally generated dynamics path. Interaction with the fluid can be indirectly achieved by rigging the rigid particles which implicitly handles rigid-fluid coupling. We used marching cubes to extract the surfaces of the objects, and applied the PN-triangles to replace the planar silhouettes with cubic approximations. We provide discussion on evaluation metrics for physically-based modeling algorithms. In addition, GPU solutions are designed for physics solvers, isosurface extraction and smoothing.
Committee: Drs. Marc Olano (CSEE; Advisor, Chair), Penny Rheingans (CSEE), Jian Chen (CSEE), Matthias Gobbert (Math), Lynn Sparling (Physics)
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Ph.D. Dissertation Defense The Modeling Equation: Solving the Physically-Based Modeling and Animation...
http://www.csee.umbc.edu/2015/08/phd-defense-yu-wang-physically-based-modeling-and-animation/
https://my3.my.umbc.edu/api/v0/pixel/news/53568/guest@my.umbc.edu/e888fcdb70074f9cf8efa8209f3ab323/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 24 Aug 2015 22:17:32 -0400
"IS 498: Data Analytics for Cybersecurity" Spring 2016
Infosec, 3rd Programming Course or UL IS Elective
Special Topic "IS
498: Data Analytics for Cyber Security "
Dr. Vandana Janeja
Semester - Spring 2016 - M/W 1:00-2
Prerequisite: IS
147 and IS 410
Cyber attacks pose an increasing threat to the nation's critical infrastructure
including computer networks, cyber physical systems such as
industrial control systems, sensor networks to name a few. This
course will be geared towards understanding the cyber security arena
and the relevant technological challenges and potential solutions. It
will introduce key topics in data analytics relevant for cyber
security and will deal with practical applications where these can be
used. Other specific topics will include categorizing cyber threats
and types of solutions, understanding vulnerabilities, Intrusion
detection systems, federal initiatives, Data analytics for cyber
security, case studies in using data analytics for cyber security,
hands on tools for discovering cyber security threats.
This course can be
used to satisfy the third programming course requirement for the IS
major. This course will be part of the cyber security certificate,
which is planned to be offered in the next year.
]]>
Special Topic "IS 498: Data Analytics for Cyber Security " Dr. Vandana Janeja Semester - Spring 2016 - M/W 1:00-2 Prerequisite: IS 147 and IS 410 Cyber attacks pose an increasing threat to...
https://my3.my.umbc.edu/api/v0/pixel/news/53530/guest@my.umbc.edu/e59ce6c3f9ec60297f0b2b71735881b9/api/pixel
analytics
cybersecurity
infosec
programming
ul
Information Systems Security Association, UMBC Chapter
https://my3.my.umbc.edu/groups/issa
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
2
0
true
Sun, 23 Aug 2015 22:27:32 -0400
CSEE faculty comment on Ashley Madison data breach

CSEE faculty Anupam Joshi and Rick Forno were interviewed this week by several media outlets on the impact and cybersecurity aspects of the Ashley Madison data breach.
Ashley Madison is a popular website with “more than 33 million members in 46 countries” that provides services “for married men and women looking to have a discreet affair.” Last month a group claimed to have obtained data about the site’s users and threatened to release it unless the site’s Toronto-based company, Avid Life Media Inc., shut down the service. Earlier in the spring, the company had announced plans for an IPO later in the year. The company called the hacker’s bluff and the group, the Impact Team, released more than 30G of customer data in several dumps this week. Avid Life has confirmed that some of the customer data posted is legitimate.
Professor Joshi, director of the UMBC Center for Cybersecurity and also chair of the CSEE department, was interviewed by ABC2. In the interview, he cautioned that data breaches are increasingly becoming part of daily life. “Information is valuable,” he said. “People are after information. No security is perfect and once you marry these things, there is an incentive for someone to spend the right time and effort to steal some information.” He also spoke about users falling into a false sense of security. “Nothing is really secure on the Internet,” he warned. “If you don’t want the thing you’re doing to show up on ABC2 at some point then don’t do it.”
Dr. Forno, Center for Cybersecurity assistant director and head of UMBC Cybersecurity Graduate Program spoke to Beta Boston and TV Newsroom about public reactions as the data breach revealed several government officials as users of the website. “Depending on who you talk to, you’ll get two wildly different opinions on the issue,” he said. “Some people will say, `Well, they broke the law, they hacked into this private company’s computers and stole data.’ Yeah, that’s true. But from the other side, you have to say, were they doing this for a public service?” He also discussed the incident with South Korea-based radio program “This Morning with Alex Jensen.”
Some material adapted from an Insights article by Achsah Callahan.
]]>
CSEE faculty Anupam Joshi and Rick Forno were interviewed this week by several media outlets on the impact and cybersecurity aspects of the Ashley Madison data breach. Ashley Madison is a...
http://www.csee.umbc.edu/2015/08/csee-faculty-comment-on-ashley-madison-data-breach/
https://my3.my.umbc.edu/api/v0/pixel/news/53522/guest@my.umbc.edu/8bfd372b0e66c188082625d11f4098ee/api/pixel
cybersecurity
faculty-and-staff
news
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sat, 22 Aug 2015 11:30:00 -0400
Sat, 22 Aug 2015 11:30:00 -0400
PhD proposal: Assistive Contactless Capacitive Electrostatic Sensing System, 12pm 8/21

Ph.D. Proposal
ACCESS: An Assistive Contactless Capacitive
Electrostatic Sensing System
Alexander Nelson
12:00pm Friday, 21 August 2015, ITE 325b
The objective of ACCESS is to develop fabric capacitor sensor arrays as a holistic, wearable, touchless sensing solution. The fabric sensors are lightweight, flexible, and can therefore be integrated into items of everyday use. Further, the capacitive sensing hardware is low-power, unobtrusive, and easily maintainable. The research includes: the construction of fabric sensor prototypes and custom sensing hardware; the development of adaptive signal processing and gesture recognition; and the creation of an assistive cyber-physical interface for mobility impairment. The research is conducted with advisement from medical professionals and private consultants, and evaluated in clinical trials by individuals with upper-extremity mobility impairment. Proposed future work includes evaluation of the assistive device for computational overhead, the inclusion of personal contextual information in gesture recognition and device actuation, and investigation of a dense spatial-resolution capacitor sensor array as a low-resolution greyscale imaging system.
Committee: Drs. Nilanjan Banerjee and Ryan Robucci (Chairs), Chintan Patel, Sandy McCombe-Waller (UMB Medical School)
]]>
Ph.D. Proposal ACCESS: An Assistive Contactless Capacitive Electrostatic Sensing System Alexander Nelson 12:00pm Friday, 21 August 2015, ITE 325b The objective of ACCESS is to develop...
http://www.csee.umbc.edu/2015/08/phd-proposal-assistive-contactless-capacitive-electrostatic-sensing-system-12pm-821/
https://my3.my.umbc.edu/api/v0/pixel/news/53495/guest@my.umbc.edu/776bc6d1a9e148b889d4ca616b355001/api/pixel
computer-engineering
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 20 Aug 2015 21:24:37 -0400
Opportunities through robotics: Kavita Krishnaswamy ’07

An interview with UMBC Computer Science Ph.D. student Kavita Krishnaswamy appeared in a recent post on the UMBC Alumni Blog.
Every so often, we’ll chat with an alum about what they do and how they got there. Today we’re talking with Kavita Krishnaswamy ’07, mathematics and computer science. Krishnaswamy has spinal muscular atrophy and has not been able to leave her house in six years. Thanks to Beam Telepresence Technology, a robotic program that allows her to remotely view and navigate spaces through her computer screen, she’s presented her doctoral thesis and attended conferences across the country. The current Ph.D. student talks about her experience with the Beam and her research on robotics and accessibility.
Read the full interview on the UMBC alumni blog.
]]>
An interview with UMBC Computer Science Ph.D. student Kavita Krishnaswamy appeared in a recent post on the UMBC Alumni Blog. Every so often, we’ll chat with an alum about what they do and how...
http://www.csee.umbc.edu/2015/08/opportunities-through-robotics-kavita-krishnaswamy-07/
https://my3.my.umbc.edu/api/v0/pixel/news/53416/guest@my.umbc.edu/3818f1a827c844df3997d036229c1fa3/api/pixel
alumni
computer-science
graduate
news
research
robotics
students
Computer Science and Electrical Engineering
https://my3.my.umbc.edu/groups/csee
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 18 Aug 2015 09:37:00 -0400


 As Lauren Reid asks, "What could possibly go wrong?"
As Lauren Reid asks, "What could possibly go wrong?"




